Cybersecurity News & Trends – 10-29-21
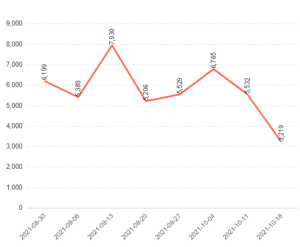
News outlets continue quoting the Mid-Year Update to the 2021 SonicWall Cyber Threat Report. Meanwhile, SonicWall’s The Year of Ransomware report catches attention with third-quarter data: a 148% surge in global ransomware attacks making 2021 the worst year ever recorded. In industry news, hackers launch SEO poisoning, Microsoft launches a cybersecurity job campaign, U.S. cyber teams take down REvil, and Russian hackers hide behind American home Wi-Fi networks.
SonicWall in the News
‘The Year of Ransomware’ Continues with Unprecedented Late-Summer Surge
AIThority: Citing SonicWall’s “The Year of Ransomware” report, there was a 148% surge in global ransomware attacks (495 million) year to date. The third-quarter surge makes 2021 the worst year SonicWall has ever recorded.
The World Is Now Facing a Spate of Coordinated Cyber Attacks
Telecom TV: Ransomware incursions have reached “pandemic levels” while old-fashioned DDoS attacks still pack a punch. Meanwhile, “never-before-seen” malware variants are emerging every day, according to a recent cyber threat report from SonicWall. The author goes on to name SonicWall “the world’s most quoted expert on ransomware.”
Unprecedented and Coordinated Cyber Attacks
National Security News: An “unprecedented” and “coordinated” spate of cyberattacks is hitting many U.K. VoIP services. So says the Comms Council in the U.K. There have been 495 million known ransomware attacks perpetrated so far this year, according to a recent threat report from SonicWall titled “The Year of Ransomware.”
Thwarting Phishing Threats with Simulations
Security Boulevard: Social engineering schemes continue to flourish, making their way into company inboxes with the intent to mislead employees into downloading malicious software. How likely is this to happen to your company? According to SonicWall, there was a record-high 304.7 million ransomware attacks in the first half of 2021. So the short answer is, it’s very likely.
How Safe is the U.K. From Cybercrime?
TechMonitor: The U.K. comes fifth in a new global ranking that combines five cybersecurity and anti-money laundering protections indices. The author notes the growing importance of countering phishing and ransomware attacks, significantly as the latter has increased by 151% in the first half of 2021, from the same period in 2020, according to the mid-year update on SonicWall’s Cyber Threat Report.
The Invisible War
Handelsblatt (Germany): An outstanding article in one of Germany’s most important daily newspapers mentions SonicWall as an expert in cybersecurity and quotes the 2021 Cyber Threat Report Mid-Year Update. The authors cite several vital stats from the report to explain the rise of various threats that have weakened cybersecurity throughout the world. The article appeared online and in the print issue of the publication.
How to Create a Relevant Cybersecurity Strategy
Accounting Web (U.S.): Using SonicWall’s Mid-Year Update on the 2021 Cyber Threat Report, the author illustrates the sharp rise in cybersecurity attacks. The article is mostly about how CPAs and other accounting professionals play a crucial role in protecting financial data. However, the author also provides an overview of the most common cyberattacks, such as malware and phishing, and offers tips on making sure your organization has the proper protections in place.
‘Clumsy’ BlackByte Malware Reuses Crypto Keys, Worms into Networks
Dark Reading (U.S.): A unique malware named “BlackByte” was discovered during a recent incident response engagement. The malware reportedly avoids Russian computers and uses a single symmetric key for encrypting every compromised system. Additionally, the report cites SonicWall’s “Cyber Threat Report: Mid-Year Update” and notes that the number of ransomware attacks in the first half of the year rose 150% to almost 305 million.
Industry News
Ransomware Gangs Use SEO Poisoning to Infect Visitors
Bleeping Computer: SEO poisoning, also known as “search poisoning,” is an attack method that relies on optimizing websites using ‘black hat’ SEO techniques to rank higher in Google search results. Due to their high ranking, victims who land on these sites believe they are legitimate, and actors enjoy a heavy influx of visitors who look for specific keywords. According to this story, two campaigns have surfaced recently. One is linked to Gootloader and the other to the SolarMarker backdoor. Most campaigns deploy SEO poisoning payloads via PDFs that drop the malware into the victim’s device. Additionally, threat actors use redirects to prevent their sites from being removed from search results. Adding to the problem, threat actors also hacked the Formidable Forms plugin found on many WordPress websites.
Microsoft Launches Campaign to Fill 250,000 Cybersecurity Jobs
Axios: Microsoft announced Thursday that it’s launching a national campaign to help fill 250,000 cybersecurity jobs in the U.S. by 2025, including providing a free curriculum to every public community college. The company’s president Brad Smith warned that the current workforce shortage is at crisis levels and threatens to undermine the country’s ability to protect itself against cyber and ransomware attacks.
U.S. to Create Diplomatic Bureau to Lead Cybersecurity Policy
Dark Reading: Plans are underway to revitalize the State Department and make cybersecurity a core priority with the addition of 500 new civil service positions, a 50% increase in its information technology budget, and the creation of the Bureau of Cyberspace and Digital Policy, officials have announced.
Ransomware Hackers Freeze Millions in Aid for Papua New Guinea
Bloomberg: The government’s payment system was locked by attackers last week. Hackers demanded payment from the nation hard hit by Covid-19. While government officials restored the system, they claimed they did not pay a ransom.
Martin County Tax Collector’s Possibly Hit by Ransomware Attack
WPTV News: A possible ransomware attack may have caused a lengthy closure of the Martin County Tax Collector’s offices for nearly two weeks. The Florida county office has been sending residents to a nearby county for help with processing payments. WPTV news investigated the incident when county officials did not explain the lengthy “network problems” they were experiencing.
Avista Warns Customers of Ransomware Attack
KXLY News: Avista, the chief energy provider for the Pacific Northwest, announced that one of its energy efficiency vendors was the target of a ransomware attack earlier this month. The company said it doesn’t believe any of its customers’ sensitive information was compromised. However, the company also noted that hackers got access to customers’ email addresses, utility numbers, service addresses and energy usage.
Feds Take Down Top Ransomware Hacker Group REvil
The Verge: The government has successfully hacked the hacking group REvil, the entity behind the ransomware that’s been linked to leaked Apple leaks, attacks on enterprise software vendors, and more, according to a report from Reuters. The outlet’s sources tell it that the FBI, Secret Service, Cyber Command, and organizations from other countries have worked together to take the group’s operations offline this month. In addition, the group’s dark web blog, which exposed information gleaned from its targets, is also reportedly offline.
Russian Hackers Reportedly Hid Behind Americans’ Home Networks to Mask Their Activities
Gizmodo: In case you missed it, the “SolarWinds” hackers are back. A recent report from Microsoft researchers shows that certain cyber-spies—believed to be members of Russia’s Foreign Intelligence Service—have been targeting droves of American tech firms with a new hacking campaign. According to Microsoft and other sources, Russian military hackers used weaknesses in home WiFi networks to wage hacking campaigns against high-level American targets.
In Case You Missed It
- Cyber Threat Alert: Ransomware Breaks Another Record – Ray Wyman
- Why Cybersecurity Must be First – Ray Wyman
- How to Protect Multi-Cloud Environments with a NSv Virtual Firewall – Tiju Cherian
- What’s driving job growth in cybersecurity? – Ray Wyman
- SonicWall Earns Its Third Perfect Score In A Row From ICSA Labs – Kayvon Sadeghi
- SonicWall Delivers Choice, Flexibility as Part of Cloud Evolution – Jayant Thakre
- Check Before You Click and Fight the Phish! – Ray Wyman
- The State of Cybersecurity Funding for State and Local Government – Ray Wyman
- CRN Recognizes Another Rising SonicWall Channel Star – Ray Wyman
- What is Cryptomining and how can it affect Cybersecurity? – Ray Wyman
- Living in the Wild West of the IoT – SonicWall Staff
- IoT Devices: If You Connect It, Protect It – Amber Wolff
- The Halfway Point: How Cybercrime Has Impacted Government in 2021 – Amber Wolff