Each year introduces new cyberattack trends that MSSPs must track, analyze and solve for their customers. Many new attack techniques amount to nothing. Others have devastating impact. But it’s important to remain diligent in monitoring the behaviors of cybercriminal organizations.
What security challenges will you face in 2019? Here are four predictions that could affect how you safeguard your customers in the fast-moving cyber threat landscape.
Cryptojacking will impact your resources.
In case you’re not aware, but as of late 2017, cryptomining made up a half of percent of the world’s energy consumption. In 2019, the main cryptocurrencies will become too expensive to mine legitimately, and cryptomining facilities will either liquidate assets, wait for a price spike again or switch to mining a different altcoin. The legitimate mining of coins is too difficult, thus the spike in cryptojacking.
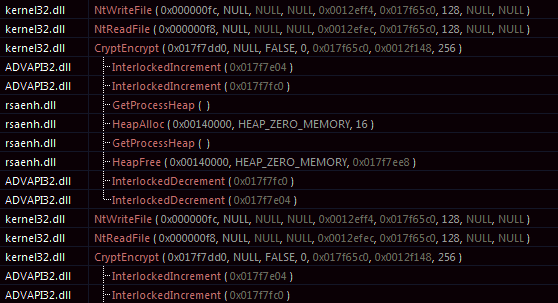
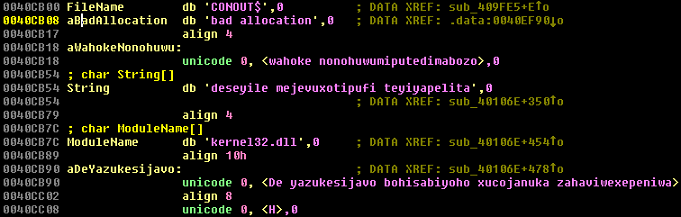
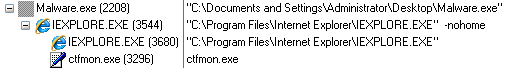
Cryptominers are a type of malware that are discretely embedded on machines with a single objective: use your processing power to illegally mine for cryptocurrency. It’s not a breach or compliance issue, so it doesn’t always grab the headlines. But cryptojacking will steal resources — from both you and your customers. This form of malware is also very difficult to detect.
The impact to your customers will likely be slower computers and collateral damage that’s a byproduct of the malware itself. To MSSPs, it can be even more damaging. If you have less compute power, you’ll need more boxes to serve your customers … costing you more and more money until the malware is properly mitigated.
The best methods for stopping malware include an overlapping approach of next-generation firewalls, secure email solutions, real-time sandboxing and advanced endpoint security, which help detect and block modern and never-before-seen malware variants, including emerging cryptojacking attacks.
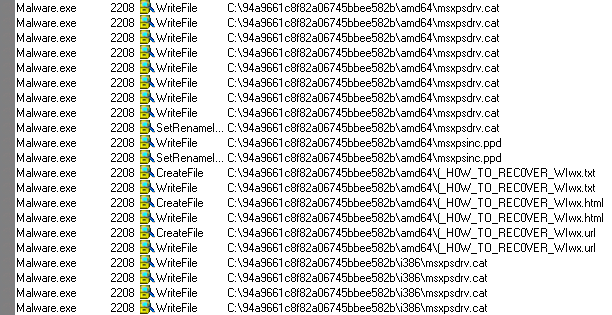
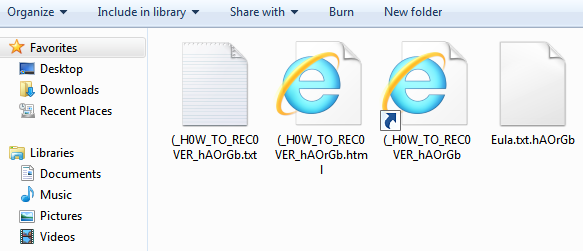
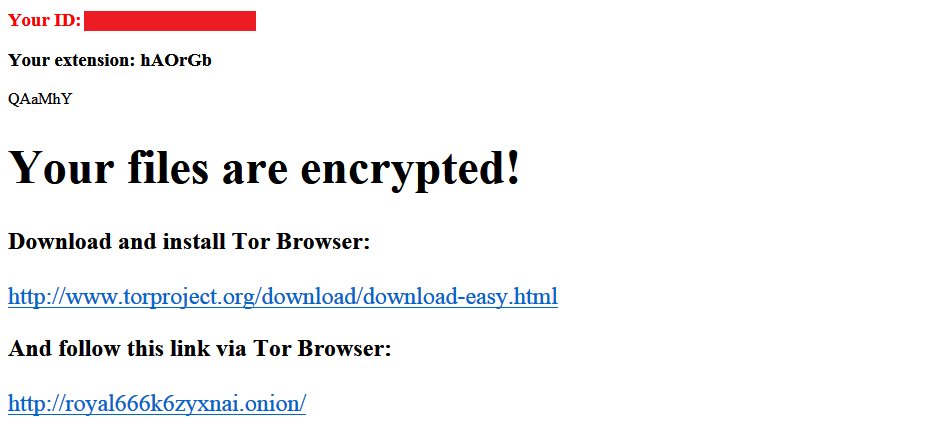
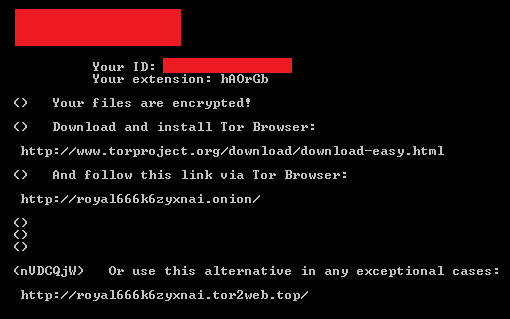
Ransomware will spike again.
While many cybersecurity vendors are still collecting full-year data for 2018, SonicWall’s year-to-date threat intelligence shows a massive ransomware spike in 2018 after a down 2017. And SonicWall’s early prediction is that 2019 will likely witness the same trend. Despite wild downward swings in cryptocurrency prices, the demands remain the same, but language is changed to reflect specific dollar amounts: “Send $750 USD worth of bitcoin.”
Through November 2018, SonicWall recorded an 119 percent year-to-date increase in ransomware attacks. In fact, each SonicWall customer faced an average of 56 ransomware attacks — in November alone. That’s a 149 percent increase over the same month last year.
Ransomware is very visible, very damaging and potentially very expensive — either for ransom payout or post-infection remediation. Simply, ransomware has a scare factor and will be noticed by your customers.
Ransomware is also a mess to clean up for MSSPs and costs you even more in support calls and tickets. The worst part? If a customer becomes a ransomware victim, there’s a high likelihood your reputation is tarnished and your relationship damaged.
Encrypted threats will continue slow rise.
It’s slow and steady, but cyberattacks via encrypted traffic (SSL/TLS) will continue to increase in volume. As long as an attacker applies for an TLS certificate with the same name that matches his/her domain registration, the (often free) certificate is theirs. Any malicious payloads delivered from said domain/website cannot be inspected by traditional means.
For the most part, SSL/TLS traffic remains an unchecked attack vector for cybercriminals to exploit. Until organizations get serious about responsibly decrypting and inspecting SSL/TLS traffic, cybercriminals will leverage it to circumvent strong networks security controls.
As an MSSP, it’s smart to advise customers to leverage next-generation firewalls and other security appliances that offer deep packet inspection of SSL/TLS traffic. This will help further reduce the attack surface area of your customers.
Customers will want you to prove your worth.
Cybersecurity is a booming — and expensive — business. So much so, many of your customers are more educated about malware trends, evolving attack strategies and criminal behavior. And thanks to data breaches published daily in the news, it’s now part of the mainstream dialogue, too.
In short, savvy customers have more awareness than ever and want indicators that demonstrate how you’re protecting their business — and how much it costs to get those results.
Many security vendors and MSSPs are already down this path. If you’re one that hasn’t yet added this to your value-add, it’s time to plan and market solutions and services that deliver customized threat intelligence to your customers. New real-time data and analysis make it easier to prove your worth.
This story originally appeared on MSSP Alert and was republished with permission.