Cybersecurity News & Trends – 06-17-22
Stories about cybersecurity news and trends curated from major news outlets, trade pubs and infosec bloggers.
SonicWall news finishes a strong week with more mentions from the 2022 SonicWall Cyber Threat Report, bylines by our cybersecurity leaders, and quotes. And of course, Industry News was very busy. From DarkReading, we learn about the retiring Internet Explorer and how it (and the associated cyber risk) will linger for years. KrebsOnSecurity and SC Media report on ransomware attackers launching a searchable public database of their victims. SiliconValley News reports on the 9-year jail sentence earned by the infamous hacker who stole millions of private images from iCloud. From Reuters, hackers managed to crash the Russian Davos event and (temporarily) stop President Vladimir Putin from speaking. In the New Zealand Herald, the story about how a spelling error saved a man from Perth $6M. And finally, our big read for the week on the successful dismantling of a huge Russian Botnet, compiled from the US Department of Justice, Bloomberg Law, Politico, and Forbes.
Remember, cybersecurity is everyone’s business. Be safe out there!
SonicWall News
Contractors Beset by Ransomware Threats Have Too Few Options
Bloomberg Law, Bill Conner Quote: The contracting community is aware of the confusion. Chester Wisniewski at Sophos, Carolyn Crandall at SentinelOne, and Bill Conner at SonicWall all outlined suggestions to Bloomberg Government in a series of interviews. Conner, SonicWall’s president and CEO, said he wants the government to install so-called “cyber czars” at each federal agency to better streamline communication.
SonicWall Recognizes APAC Partners and Distributors at FY2022 Partner Awards
Channel Life (Australia), SonicWall News: SonicWall has recognized its distributors and partners for their efforts in producing the company’s most successful year to date. The recent SonicWall FY2022 Partner Awards recognized companies for their commitment to demonstrating excellence, innovation and leadership in cybersecurity during the fiscal year. They are also thanked for continuing to drive digital transformation for businesses that leverage SonicWall solutions.
The Powerful Cyberattack That Has America on Alert
Swiss Info (Deutsch), SonicWall Threat Report Mention: The Cyber Threat Report 2022 of the US firm SonicWall, shows a rebound of 105% in data hijacking last year, surpassing 623 million attacks worldwide – almost twenty attempts per second – with the United States in the lead (421 million or 67.5% of the total).
SonicWall Awards Top Partners for FY22
ARN (Australia), SonicWall News: Cyber security vendor SonicWall has awarded its top-performing partners for its 2022 fiscal year ending 31 January.
The Cybersecurity Challenges of Remote Working and How a Brand Can Eliminate Them
E Business (UK), SonicWall Mention: SonicWall provides trusted solutions delivering wireless, switches, firewalls, and CCTV that can keep businesses safe from an attack and avoid downtime.
Best Practices for Protecting Against Phishing, Ransomware and Email Fraud
CXOtoday (India), SonicWall Byline: Security teams and the organizations they support live in difficult times: they increasingly are the targets of sophisticated threats developed by a shadowy and very well financed cybercrime industry that has demonstrated it can often outsmart even the most robust security defenses.
Dicker Data, Hitech Support, Next Telecom, Datacom score SonicWall Honors
CRN (Australia), SonicWall News: “SonicWall has awarded Australian partners Dicker Data, Hitech Support, Next Telecom, Datacom System and Dell Australia for their work at its Asia-Pacific Partner Awards for the 2022 financial year.”
What is a Cyberattack? Types and Defenses
eSecurity Planet, SonicWall Threat Report Mention: Driven by the global pandemic, the increase in remote and hybrid work, and unprepared network defenses, cyberattacks have been rising exponentially. The 2022 SonicWall Cyber Threat Report found that all types of cyberattacks increased in 2021. Encrypted threats spiked 167%, ransomware increased 105%, and 5.4 billion malware attacks were identified by the report.
Ransomware, the Cyberattack That Set Off Alarms in Latin America
Forbes Colombia, SonicWall Threat Report Mention: The Cyber Threat Report 2022 of the US firm SonicWall, shows a rebound of 105% in data hijacking last year, surpassing 623 million attacks worldwide – almost twenty attempts per second – with the United States in the lead (421 million or 67.5% of the total).
Industry News
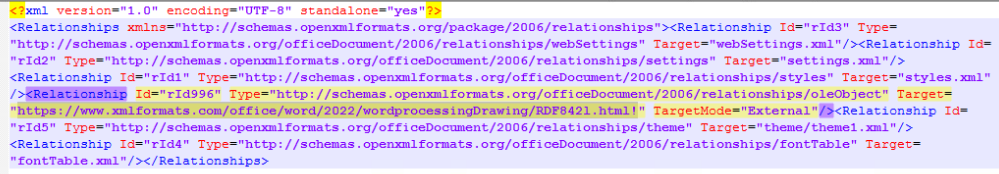
Internet Explorer Is Now Retired but Remains an Attack Target
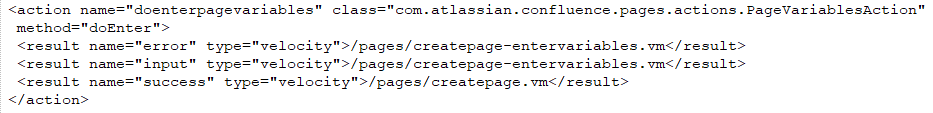
DarkReading: Microsoft’s June 15th official end-of-support for Internet Explorer 11 desktop software has left behind a browser that has been around for almost 27 years. Even so, IE will likely remain a lucrative target for attackers.
Despite Microsoft’s long-standing plans to discontinue Internet Explorer (IE), some organizations continue to use it. Microsoft has maintained the MSHTML (aka Trident), IE browser engine in Windows 11 through 2029. This allows organizations to continue to use IE mode while transitioning to Microsoft Edge. So IE is not dead yet.
Although IE is typically a minor player in the global browser market (0.52%), many companies use it internally or have legacy applications tied to IE. This week, Nikkei Asia stories and Japan Times cited a Keyman’s Net survey showing that almost 49% of 350 Japanese companies surveyed use IE daily. Likewise, South Korea’s MBN indicated that many large organizations are still using IE and will likely continue using it for the foreseeable future.
Ransomware Group Launches Searchable Victim Data
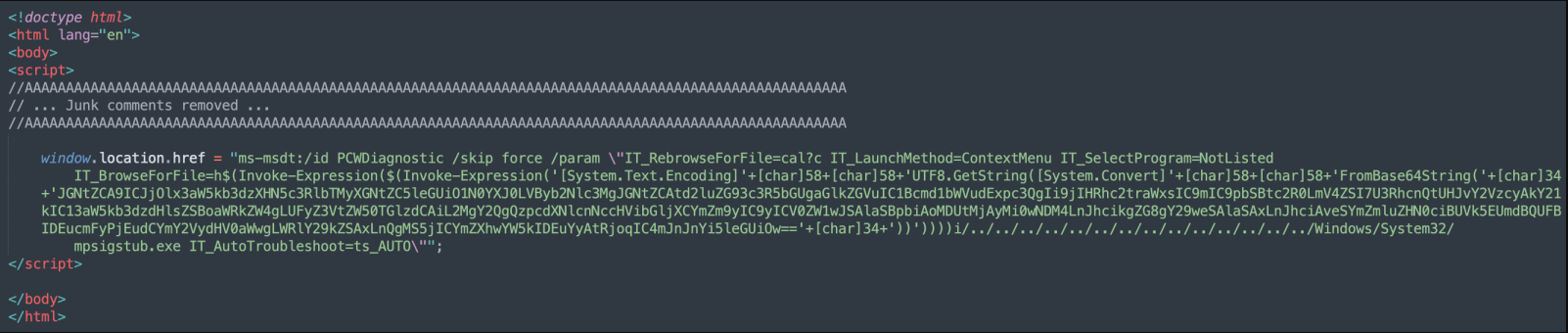
KrebsOnSecurity – Cybercriminals that target corporate data theft and demand ransoms to keep it from being published have tried many methods to shame victims into paying. The ALPHV ransomware group, also known as “BlackCat,” has made the gambit harder and harder to avoid.
They previously tried publishing victim data in repositories on the Dark Web. Now they’re going big with a new public website to post their booty on individual victims. And they’re inviting the public to search the leaked data.
ALPHV announced its new victim-shaming website that they had hacked a luxury resort and spa in the western United States. The database of shame includes the personal data of more than 1,500 resort employees and 2,500 resort residents. In addition, the page’s top has two buttons that allow guests to “Check Yourself” – one for employees and the other for guests.
SC Media also reported that their security expert described the site as “kinda like a bad guy’s version of HaveIBeenPwned,” with the main difference being that data on HaveIBeenPwned is anonymized. ALPHV displays all, including full names, dates, expenditures, and other personal data, including email addresses, birthdays, and social security numbers.
SC Media and KrebsOnSecurity chose not to reveal the hotel’s name to protect their personal information. The whole point of the ALPHV website is to pressure the hotel for payment.
Hacker Sentenced to 9 Years for Hacking Apple iCloud and Stealing Private Images
SiliconValley: Nine years of federal imprisonment have been given to a Californian man accused of hacking Apple iCloud and stealing private images and videos of young women, some nude and some engaged in personal activities.
According to court records, Hao Kuo Chi, 41, from La Puente in California, was sentenced Wednesday at a federal court in Tampa, Florida. According to court records, he pleaded guilty to three counts of computer fraud and one count of conspiracy to commit computer crime last October.
Chi also ran a notorious website Anon-IB for many years, where users posted images labeled as “revenge porn.” Officials claim that Chi hacked into victims’ Apple iCloud accounts to steal their private photos and videos. They also said he shared and traded the images with other users on AnonIB.
Chi’s email accounts contained the iCloud credentials for approximately 4,700 victims and had collected enough media to fill 3.5 terabytes on iCloud and physical storage devices.
Court testimony reveals that he shared stolen content with conspirators over 300 times. While some conspirators publicly released the images, he kept some of the images for himself connected to 500 victims.
Hackers Crash “Russian Davos” and Stops Putin’s Speech
Reuters: Hackers impeded President Putin’s speech at Russia’s top economic forum last Friday. This happened as Russia worked to adjust to its “new reality.” The meeting was already struggling due to a lack of Western participation. Nevertheless, the 25th St Petersburg International Economic Forum was attended by many state companies, with many stalls featuring floor-to-ceiling display screens and glamorous attendants.
Dmitry Peskov, a spokesperson for the Kremlin, stated that a denial-of-service attack (which involves flooding servers with fake traffic) had caused the forum’s admission and accreditation systems to be hampered. Although he did not blame the incident on the ongoing war in Ukraine, reporters noted that it was unofficially suspected.
Spelling Mistake Stops Perth Man’s $6m Fortune from Being Stolen by BEC Hackers
NZ Herald: This story illustrates how cybersecurity is everyone’s business. A Perth businessman almost lost $6 million to hackers, but one misspelled word saved him from watching his fortune falling into the wrong hands.
He was at the end of a multimillion-dollar property settlement with a trusted buyer. But unfortunately, the other party’s business email account in the deal was compromised by cybercriminals. The hackers intercepted the emails and changed the bank account details to their accounts.
An entry-level employee noticed that the word “group” was misspelled as “gruop.” After her timely alert, an inspection revealed that the business email account was compromised, and the bankers stopped the transaction just in time.
Also see “BEC – Business Email Compromise”
US and Global Law Enforcement Partners Dismantle Russian Botnet
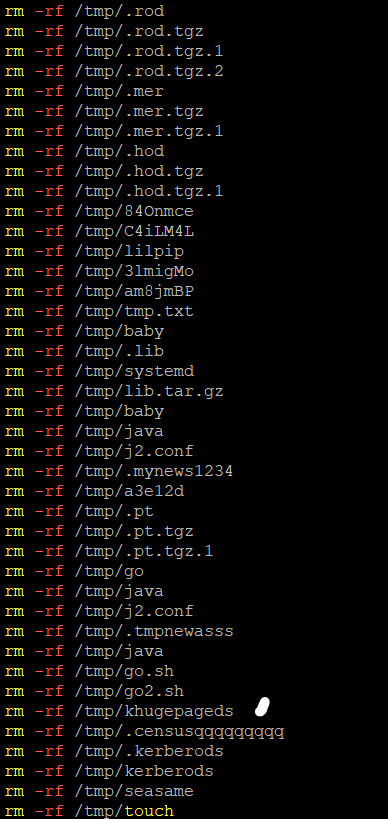
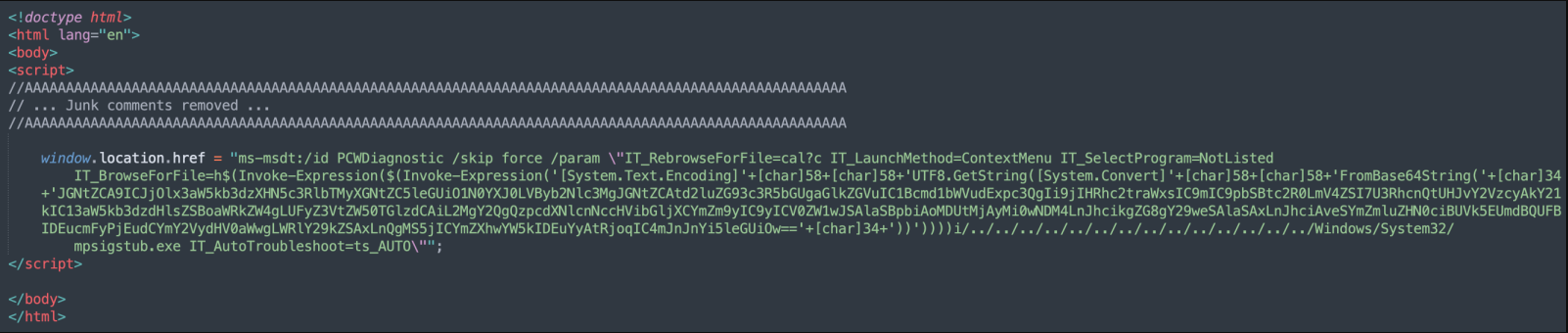
Multiple Sources: According to the US Department of Justice, US cybersecurity agents worked with law enforcement partners from the UK, Netherlands and Germany to dismantle the infrastructure of a Russian botnet called RSOCKS that hacked into millions of computers around the globe.
A botnet is an internet-connected group of devices that have been hacked and are controlled by attackers. They are often used to commit malicious acts. Each device connected to the internet has an Internet Protocol (IP) address.
Bloomberg Law provides additional details that the Botnet targeted IoT devices like clocks, routers and streaming devices. Hackers used these compromised devices as proxy servers to allow paying customers to access the compromised devices’ IP addresses and launch attacks. According to Bloomberg, the group’s Twitter account claimed access to more than eight million residential IPs and more than a million mobile IPs.
Politico reported that proxy services, which aren’t inherently illegal, provide IP addresses for their clients for a fee. However, the service includes bypassing censorship and accessing geo-blocked for a specific region. Prosecutors claim that RSOCKS was hacking into millions of devices using brute force attacks.
Customers could visit a web-based storefront to rent proxies for a specified period. Additionally, the customer could download a list of IP addresses and ports associated with the Botnet’s backend server and route malicious internet traffic through these compromised devices while hiding the source.
A related story by Forbes states that the Botnet was the home of a darknet market called Hydra Market. The marketplace’s closure is linked to subsequent seizures, including a superyacht owned by Viktor Vekselberg and $5.4M cash from Konstantin Malofeyev. The US DOJ identified Malofeyev as a Russian oligarch who attempted to use the Botnet services to circumvent sanctions.
In Case You Missed It
BEC Attacks: Can You Stop the Imposters in Your Inbox? – Ken Dang
SonicWall CEO Bill Conner Selected as SC Media Excellence Award Finalist – Bret Fitzgerald
Cybersecurity in the Fifth Industrial Revolution – Ray Wyman
What is Cryptojacking, and how does it affect your Cybersecurity? – Ray Wyman
Why Healthcare Must Do More (and Do Better) to Ensure Patient Safety – Ken Dang
SonicWall Recognizes Partners, Distributors for Outstanding Performance in 2021 – Terry Greer-King
Anti-Ransomware Day: What Can We Do to Prevent the Next WannaCry? – Amber Wolff
CRN Recognizes Three SonicWall Employees on 2022 Women of the Channel List – Bret Fitzgerald
Enjoy the Speed and Safety of TLS 1.3 Support – Amber Wolff
Four Cybersecurity Actions to Lock it All Down – Ray Wyman
Understanding the MITRE ATT&CK Framework and Evaluations – Part 2 – Suroop Chandran
Five Times Flawless: SonicWall Earns Its Fifth Perfect Score from ICSA Labs – Amber Wolff
NSv Virtual Firewall: Tested and Certified in AWS Public Cloud – Ajay Uggirala
How SonicWall’s Supply-Chain Strategies Are Slicing Wait Times – Amber Wolff
SonicWall SMA 1000 Series Earns Best-Of Enterprise VPNs Award from Expert Insights – Bret Fitzgerald
World Backup Day: Because Real Life Can Have Save Points Too – Amber Wolff
CRN Honors SonicWall With 5-Star Rating in 2022 Partner Program Guide – Bret Fitzgerald
Cyberattacks on Government Skyrocketed in 2021 – Amber Wolff
Meeting the Cybersecurity Needs of the Hybrid Workforce – Ray Wyman
Third-Party ICSA Testing – Perfect Score Number 4 – Kayvon Sadeghi
Ransomware is Everywhere – Amber Wolff
Shields Up: Preparing for Cyberattacks During Ukraine Crisis – Aria Eslambolchizadeh