Citrix ADC and Gateway Authorization Bypass Vulnerability
Citrix ADC is an application delivery and load balancing solution that provides a high-quality user experience for web, traditional, and cloud-native applications – regardless of where they are hosted. It also provides web application acceleration as well as a Gateway functionality. Citrix ADC and Gateway are accessed primarily via HTTPS on port 443/TCP.
Vulnerability(CVE-2020-8193)
An authorization bypass vulnerability exists in Citrix Application Delivery Controller and Gateway. The
vulnerability can let remote users to get a valid session ID on Web UI without authentication. A remote, unauthenticated attacker could exploit the vulnerability by sending crafted requests to the target server.
Successful exploitation can result in authentication bypass.
The NetScaler IP (NSIP) address is the IP address which is used to access the NetScaler appliance for management purpose over HTTP (port 80). To restrict the NSIP administrative Web UI from unauthenticated users, the Admin UI needs the remote user to login by using HTTP POST request.
After the remote users authenticate themselves, the server will generate a sessionID in the cookie for the
administrative session. An authorization bypass vulnerability exists in Citrix Application Delivery Controller and Gateway.Due to the design flaw this vulnerability can be triggered by posting to the report() function .
![]()
Based on the value specified in parameter type, the function report() will call the respective private functions
inside pcidss.php script. Due to the implementation flaw, the report function only checks the presence of “loginchallengeresponse” in the parameters of the POST request. This allows for authentication bypass and the attacker can get a valid session id which can later be used to gain direct access to the device.
Impact
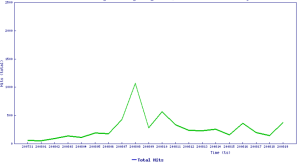
A quick check on shodan reveals hundreds of vulnerable systems
SonicWall Capture Labs provides protection against this threat via the following signatures:
- IPS 15098:Citrix Products Authorization Bypass 1
- IPS 15099:Citrix Products Authorization Bypass 2
Threat Graph
Vulnerable Products
Citrix ADC and Citrix Gateway versions before 13.0-58.30, 12.1-57.18, 12.0-63.21, 11.1-64.14 and 10.5-70.18 and Citrix SDWAN WAN-OP versions before 11.1.1a, 11.0.3d and 10.2.7
Citrix has patched this vulnerability and the fix is available here.




