Frequently Asked Questions: The E-rate Program
While we’ve explained the ins and outs of the E-rate program during the five-part SonicWall E-rate Fear Less series, we wanted to use the final episode to explore the common questions about the E-rate program itself and how SonicWall cyber security solutions may be funded via the program.
Episode Five: E-rate Fear Less Series Q&A
Holly Davis interviews SonicWall software business development director John Mullen.
The final video in our five-part series explores these common E-rate program questions:
- Why SonicWall for the K12 Environment?
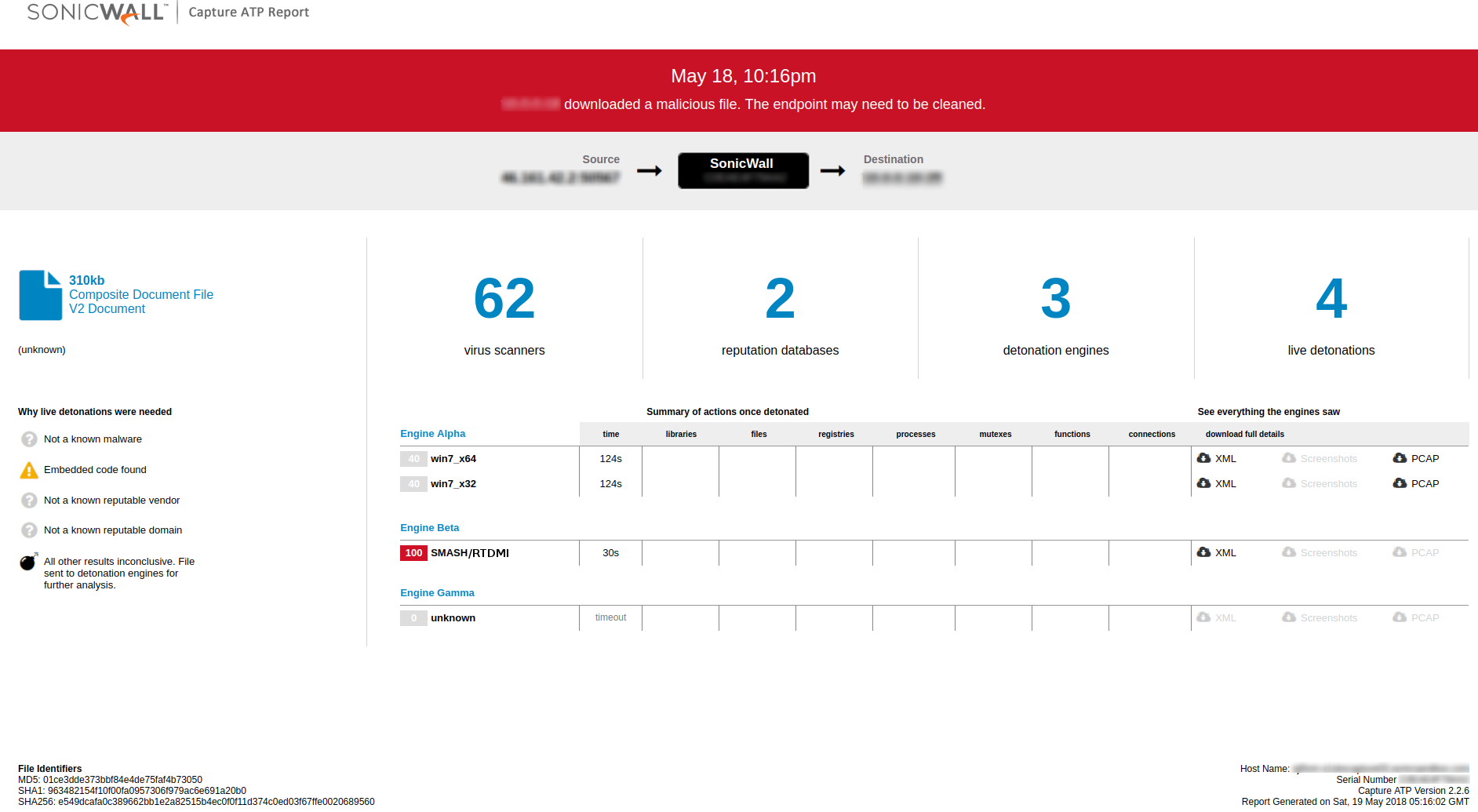
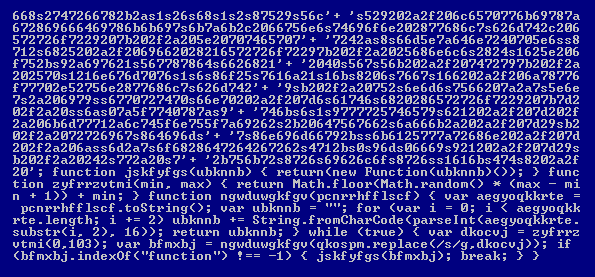
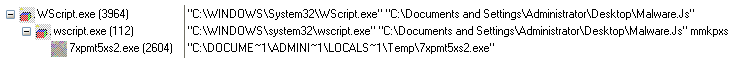
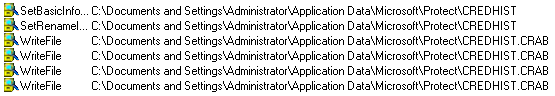
- What is SonicWall Capture ATP?
- Why would SonicWall Capture ATP sandboxing be necessary for K12?
- What is SonicWall SECaaS?
- Does E-rate fund firewalls in their entirety?
- Is Capture ATP funded by the E-rate program?
- Is SECaaS funded by the E-rate program?
- How do I get started with the E-rate program?
- Where can we find additional resources about the E-rate program?
What technology is eligible for funding the E-rate program?
To help offset funding and staffing shortages, the U.S. Department of Education and the FCC launched the E-rate program, which helps make telecommunications and information services more affordable for schools, campuses, districts and libraries.
The E-rate program is operated by Universal Service Administration Company (USAC), which has a core focus of providing underfunded verticals the access to affordable technology and security services. This includes schools, libraries, rural healthcare organizations and more.
USAC provides a yearly Eligible Services List (ESL), which outlines which types of products and services can be procured via E-rate program discounts.
SonicWall and E-rate
With the most comprehensive channel program in the industry, combined with additional E-rate discounts, SonicWall and our partners are best positioned to meet the needs of K12 customers and help them take full advantage of the funding E-rate provides for securing their networks.
Through its global channel of more than 24,000 technology partners, SonicWall is actively involved in helping K12 education organizations cost-effectively obtain and deploy network security solutions. SonicWall provides a broad array of E-rate-eligible products and services, including firewalls and turnkey Security-as-a-Service solutions.
If you are an eligible K12 organization, please contact your preferred SonicWall reseller for information on E-rate benefits and discounts, or visit the SonicWall E-rate page for information, tools and guidance.