New MSN messenger worm – Agent.LVB (Nov 25, 2009)
SonicWALL UTM Research team observed a new MSN messenger Worm in the wild spreading by sending malicious URLs to the online Instant Messenger contacts on the victim machine.
The IM messages looks like this:

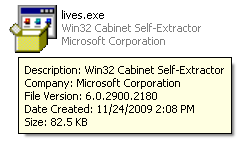
If the target user clicks on the link it will download a copy of the MSN messenger worm. The executable file is a Microsoft Cabinet Self-Extractor file and it looks like:
Upon execution, the MSN messenger worm performs following activities:
- Drops malicious executable files on the victim machine:
- (Temp)IXP000.TMPbots.exe [Detected as GAV: Agent.LVB_2 (Trojan)]
- (WINDOWS)bakajok.exe.exe [Detected as GAV: Agent.LVB_2 (Trojan)]
- Creates a registry entry HKLMSOFTWAREMicrosoftWindowsCurrentVersionRunJava Update: “bakajok.exe.exe” to ensure that the dropped copy of the malware starts on every system reboot.
- It opens up a dialog box:

- It connects to a malicious IRC server hosted at bub.th3k(REMOVED)net on TCP port 27034 and waits for C&C commands. A memory dump of the Worm shows the strings related to the IRC bot component:

- The worm detects any security tool and will stop execution. It will come back on next restart due to autostart registry entry.
SonicWALL Gateway AntiVirus provides protection against this malware via GAV: Agent.LVB (Worm) signature.



