Snoopdog ransomware charges 36K in BTC for recovery. 20% discount negotiable
The SonicWall Capture Labs threat research team have been tracking ransomware that encrypts and gives files a “.snoopdog” filename extension. The operator charges 1 BTC for file retrieval. However, as with most ransomware today, the price is negotiable and a discount may be provided to the victim.
Infection Cycle:
Upon execution, the malware encrypts files on the system. Each file is given a “.snoopdog” extension to indicate that it has been encrypted.
The following files are dropped onto the infected system:
- %APPDATA%\Roaming\noputana.exe (copy of original malware) [detected as: GAV: Snoopdog.RSM (Trojan)]
- %APPDATA%\Roaming\userkey.dat
- !DECRYPT_FILES.txt (dropped in all dirs where files were encrypted)
The following keys are added to the registry:
- HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run HelloAV “%APPDATA%\Roaming\noputana.exe”
- HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run WelcomeBack “%APPDATA%\Roaming\!DECRYPT_FILES.txt”
!DECRYPT_FILES.txt contains the following message:
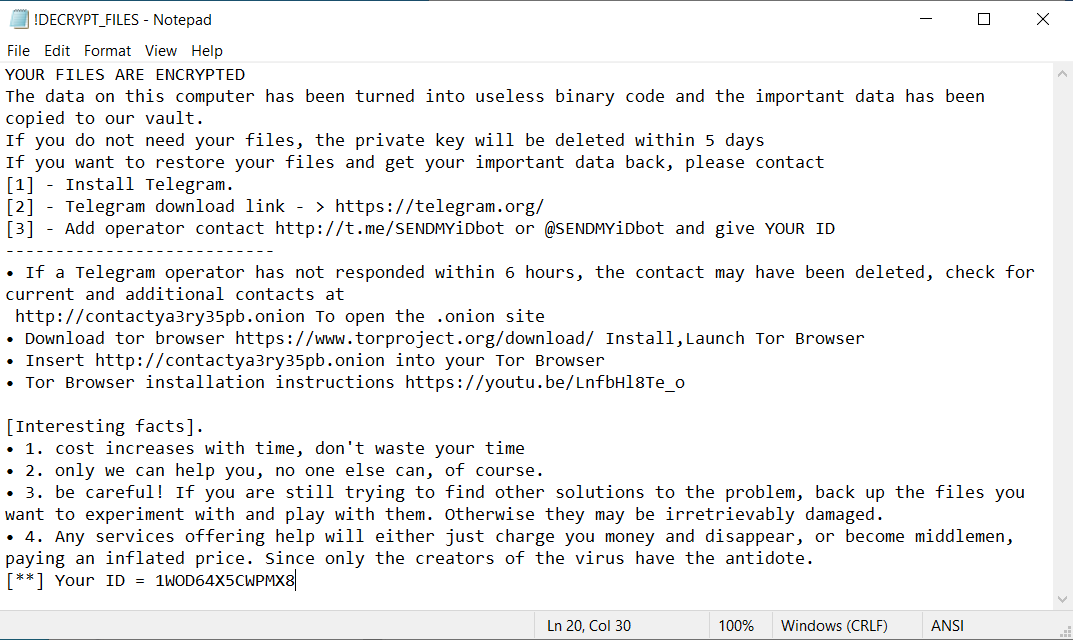
userkey.dat contains the following data:
1WOD64X5CWPMX8
The following applications are killed if found to be running:
msftesql.exe vmware-vmx.exe vmware-authd.exe sqlagent.exe sqlbrowser.exe sqlservr.exe
sqlwriter.exe oracle.exe ocssd.exe dbsnmp.exe synctime.exe mydesktopqos.exe
agntsvc.exe isqlplussvc.exe xfssvccon.exe mydesktopservice.exe ocautoupds.exe
agntsvc.exe agntsvc.exe agntsvc.exe encsvc.exe firefoxconfig.exe tbirdconfig.exe
ocomm.exe mysqld.exe mysqld-nt.exe mysqld-opt.exe dbeng50.exe sqbcoreservice.exe
excel.exe infopath.exe msaccess.exe mspub.exe onenote.exe outlook.exe powerpnt.exe
steam.exe thebat.exe thebat64.exe thunderbird.exe visio.exe winword.exe wordpad.exe
taskmgr.exe
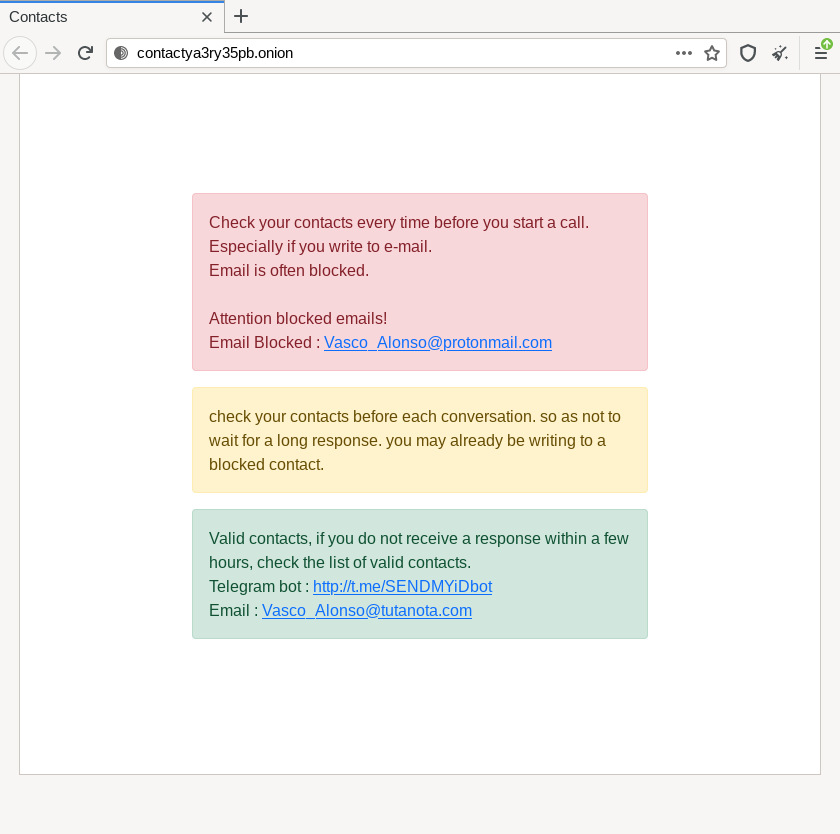
The tOr link leads to the following page:
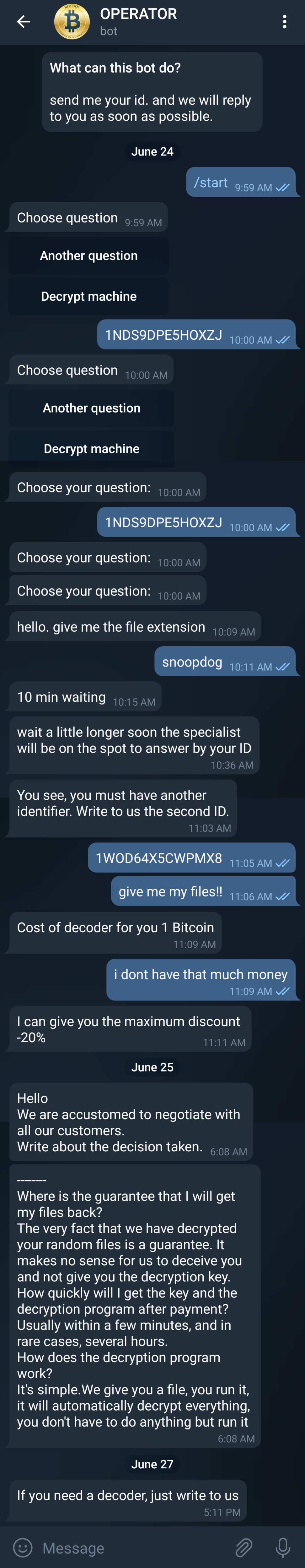
A Telegram link (http://t.me/SENDMYiDbot) is provided for communication with the malware operators. We had the following conversation with the operator:
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: Snoopdog.RSM (Trojan)
This threat is also detected by SonicWALL Capture ATP w/RTDMI and the Capture Client endpoint solutions.





