Ragnar Locker Ransomware
Overview:
SonicWall Capture Labs Threat Research Team recently found a new sample and activity for Ragnar Locker Ransomware.
Cyberattacks using Ragnar Ransomware have impacted Biological E Ltd, Capcom, and Campari Group.
A description of the corporations that were hit last week and this week are below:
- Biological E limited is a privately held biopharmaceutical company based in Hyderabad, Telangana, India.
- Capcom Co., Ltd. is a Japanese video game developer and publisher.
- Campari, is an Italian company active since 1860 in the branded beverage industry. It produces spirits, wines, and soft drinks.
Ragnar injects a module capable of collecting sensitive data from infected machines and uploads the data it finds to their servers. The ransomware notifies the victim of the files that will be released to the public if the ransom is not paid.
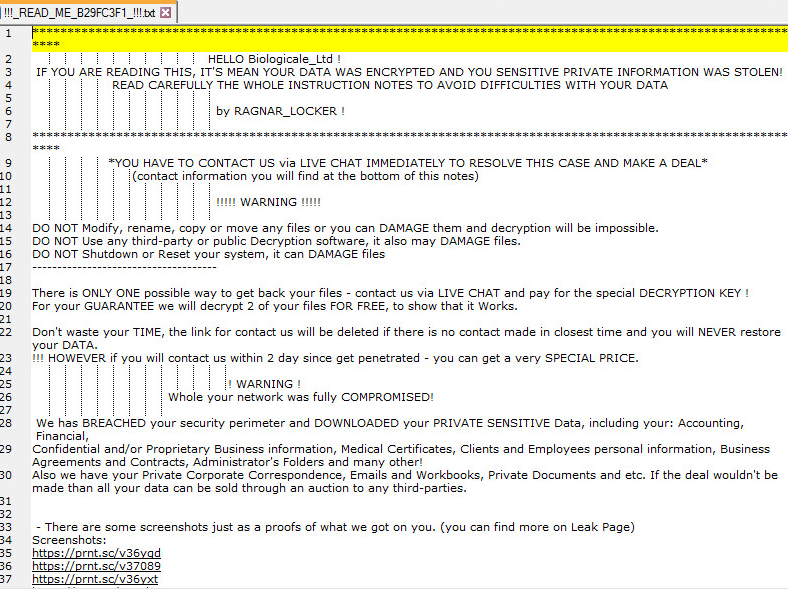
Ransomware document:
Further down the document:
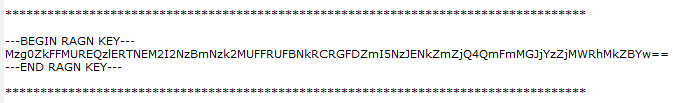
Ragnar Key is at the bottom of the document:
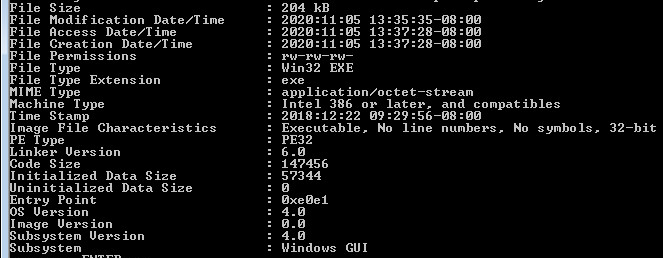
Static Layer, Information:
Overview of sample, checking for any corruption within the PE file format.
Command-Line overview of sample:
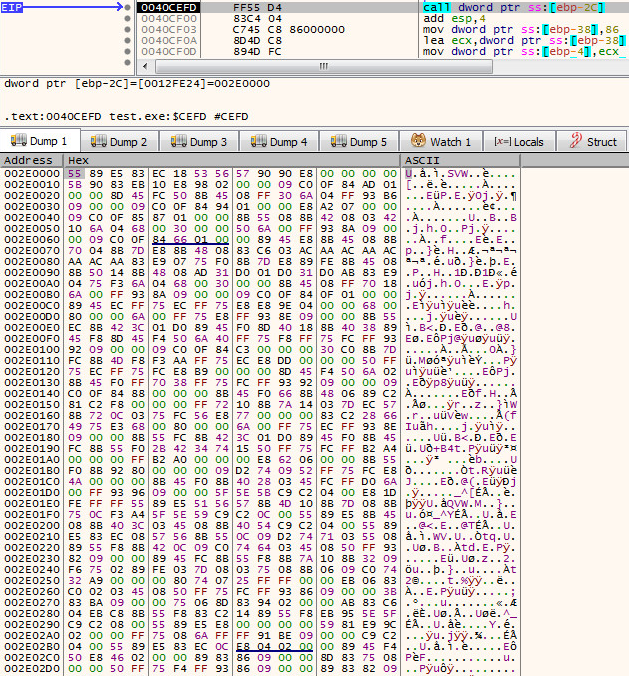
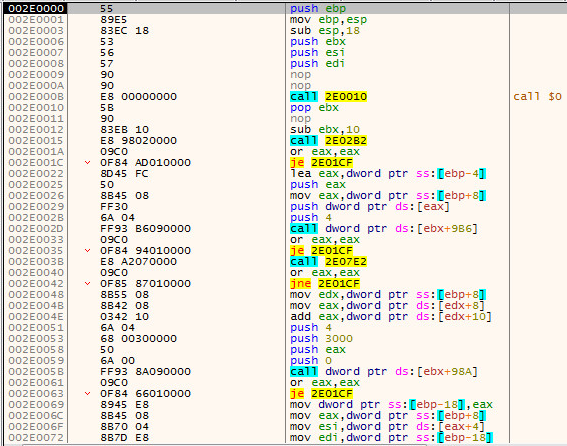
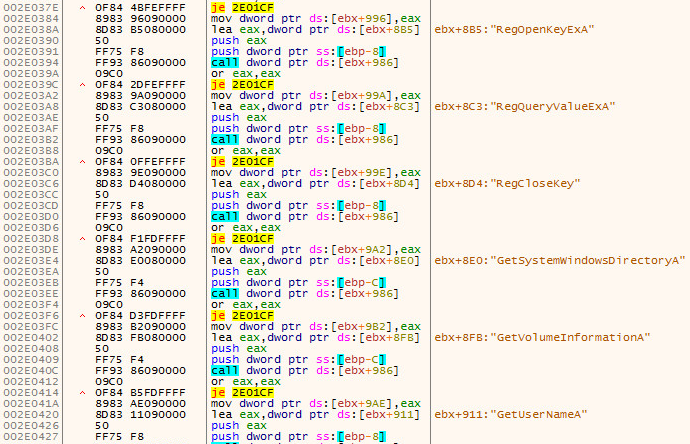
Dynamic Information:
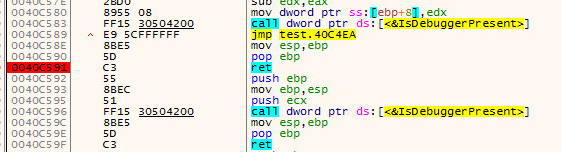
Anti-Debugging Block:
Supported Systems:
- Windows 10
- Windows 8.1
- Windows 8.0
- Windows 7
- Windows Vista
SonicWall, (GAV) Gateway Anti-Virus, provides protection against this threat:
- GAV: RagnarLocker.RSM_2 (Trojan)
Appendix:
Sample SHA256 Hash: 0766beb30c575fc68d1ca134bd53c086d2ce63b040e4d0bbd6d89d8c26ca04f6