.NET Trojan: Yubby v1.6 w/[CRM Service]…

Overview:
SonicWall Capture Labs Threat Research team has captured and observed the following sample:
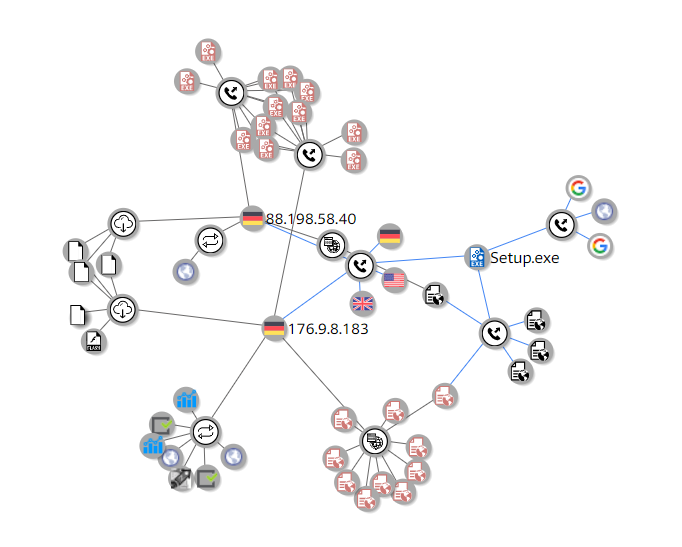
The "Yubby" Trojan is listed as a (Trojan, PUA or PUP) by many anti-virus outfits and help forums around the internet. The application establishes multiple connections to the following IP addresses (88.198.58.40) and (176.9.8.183).
An overview of the behavior (Setup.exe) is listed as:
-
-
- Opens, Deletes, and Modifies Multiple Files.
- Downloads, Installs, and Updates Files.
- Opens, Creates, Modifies, and Deletes Registry Keys.
- Creates, and Terminates Processes.
- Installs, and Executes The "CRMSvc" Service.
- The Packer and Protector uses complex obfuscation techniques using the xor algorithm.
-
SHA-256 Hash: d4db4d74240a34b066207a80080cadd428136c7dd2b8b60d08d42f7559f37e4e
The relationship between the sample and the IP Addresses above can been seen as follows:
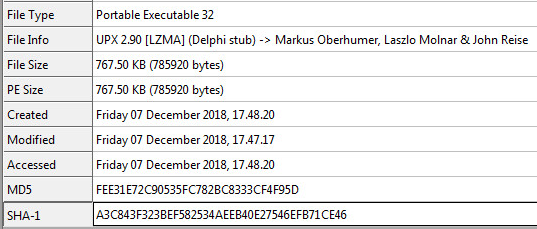
Sample Static Information:
Unpacking The Sample:
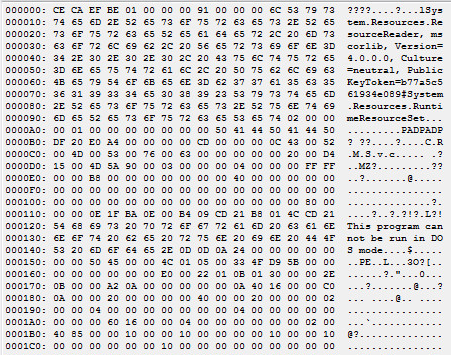
A quick look at the resource section of the sample. We see the famous, "BEEFCACE". Many kewords like this are used to pinpoint areas in memory. We also see that there is a PE File in the resource section by noticing the "MZ" signature a few lines down from "BEEFCACE".
The main function starts out with a lot of xor'ing bytes and shifting of pointers. You can see the first of many decryption functions below:
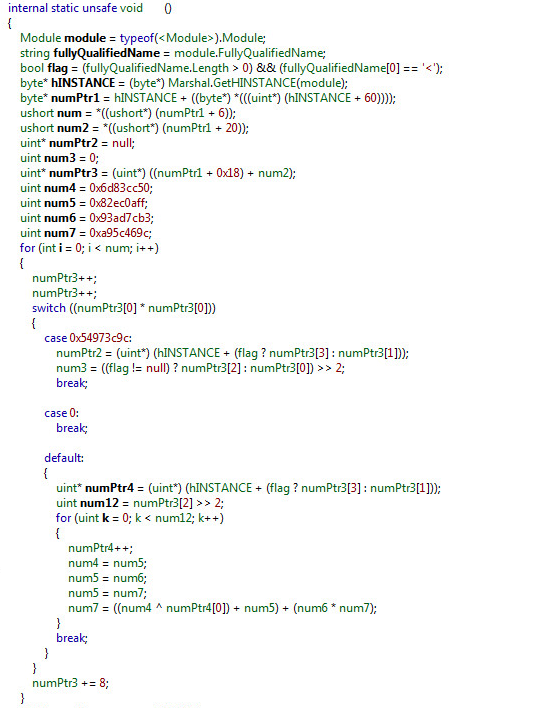
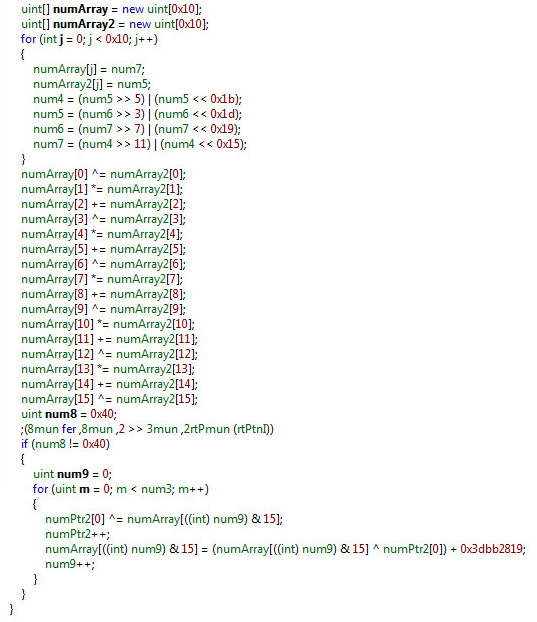
Unfortunately, this is only 1 of about 200 other decryption functions like this you have to step through in order to get to dump the array[]. After stepping through the starting function and others that follow you will arrive at the location you can dump the array:
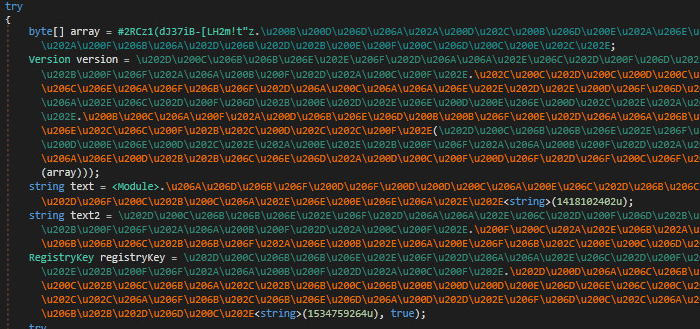
Once the sample's resource has been decrypted, you will see the installed location here:
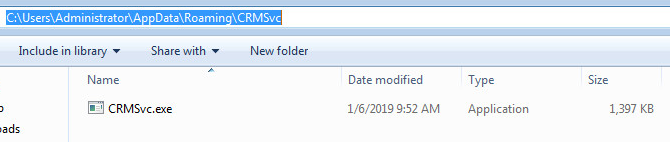
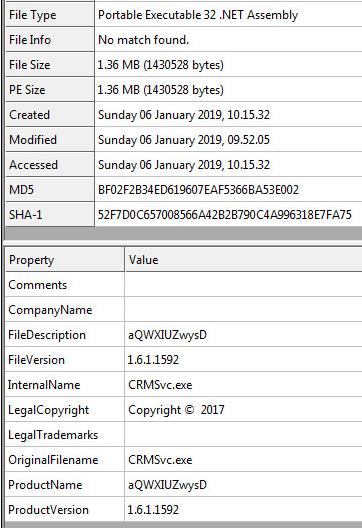
CRMSvc.exe, Static Information:
The CRM Service .EXE is also a .NET PE File.
Registry Details
- "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D105DFE2-8DF6-4BA0-ABF1-392716658963}"
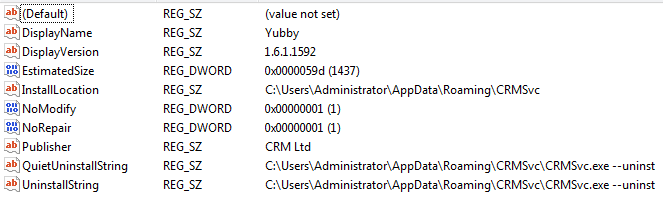
This one registry key gives us a lot of information about the sample:
- The Display Name
- Display Version
- Estimated Size of File
- Installation Location
- Publisher
- Uninstall parameters of the Trojan.
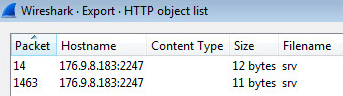
HTTP Network Objects
:
:
SonicWall Gateway AntiVirus, provides protection against this threat:
- GAV: Gdsda.A ( Trojan )
Share This Article

An Article By
An Article By
Security News
Security News