CVE-2019-11581 Atlassian Jira Unauthorized Template Injection Vulnerability
Jira is a proprietary issue tracking product developed by Atlassian that allows bug tracking and agile project management. It runs on a bundled Apache Tomcat application server and accessible via HTTP over port 8080/TCP or HTTPS over port 8443/TCP.
Vulnerability Description:
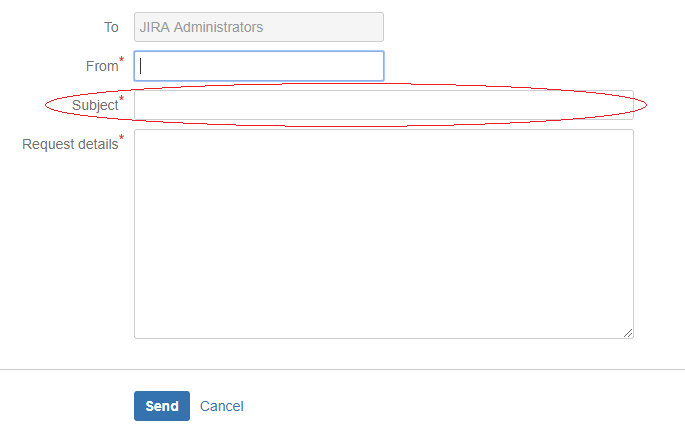
CVE-2019-11581 is a server-side template injection vulnerability in Jira Server and Data Center, in the “ContactAdministrators” and the “SendBulkMail” actions. For this issue to be exploitable at least one of the following conditions must be met:
- an SMTP server has been configured in Jira and the Contact Administrators Form is enabled; or
- an SMTP server has been configured in Jira and an attacker has “JIRA Administrators” access.
In the first case, where the Contact Administrators Form is enabled, attackers are able to exploit this issue without authentication. In the second case, attackers with “JIRA Administrators” access can exploit this issue. In either case, successful exploitation of this issue allows an attacker to remotely execute code on systems that run a vulnerable version of Jira Server or Data Center.
Vulnerability Details:

Mitigation
If you are unable to upgrade Jira immediately, then as a temporary workaround, you can:
- Disable the Contact Administrators Form
- Block access to the endpoint /secure/admin/SendBulkMail!default.jspa
Fix
Atlassian has released the latest versions of Jira Server & Jira Data Center to address this issue. it’s advisory can be found here: https://confluence.atlassian.com/jira/jira-security-advisory-2019-07-10-973486595.html
SonicWall Capture Labs Threat Research team provides protection against this exploit with the following signatures:
IPS: 14330 Atlassian JIRA Template Injection 1
IPS: 14331 Atlassian JIRA Template Injection 2
WAF: 1719 Atlassian JIRA Template Injection Code Execution
WAF: 1681 EXEC Statement (Possible SQL Injection)




