Jigsaw Ransomware spotted in the wild (April 22, 2016)
The Dell SonicWall Threats Research team has received reports of a new Ransomware Trojan, Jigsaw (named after the fictional character) which encrypts the system files and also deletes them if the payment is not made on time.
Infection cycle:
The Trojan poses as firefox with the following properties:

The Trojan adds the following files to the filesystem:
- %APPDATA%RoamingFrfxfirefox.exe (copy of original) [Detected as GAV: Jigsaw.A (Trojan)]
The Trojan creates the following key to the Windows registry to enable startup after reboot:
- HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun “”%APPDATA%RoamingFrfxfirefox.exe””
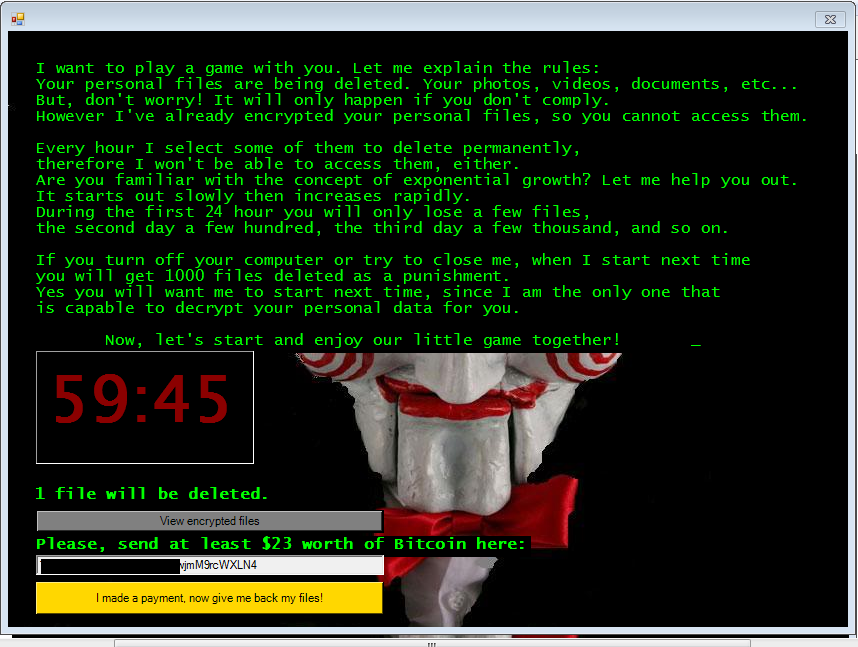
It displays the following iconic image and the message while encrypting the files:


It starts countdown and threatens to delete the files mentioned each hour.
The trojan finds the following files on the victim’s machine and encrypts them:

It copies the filenames before encrypting at the following location:

It encrypts all the victims files listed above with .fun extension.

When trying to close the ransom window, it displays the following message:

It checks for the payment contacting the C&C server:

SonicWALL Gateway AntiVirus provides protection against this threat via the following signature:
- GAV: Jigsaw.A (Trojan)





