CVE-2015-5119(Recent Adobe Flash 0-day) Exploit in the wild
We called out in our previous SonicAlert that CVE-2015-5119 is very easy to exploit. It’s not a surprise that the exploit kits have already updated their arsenal to include this CVE. Here’s an analysis of a sample used by Nuclear Exploit Kit:

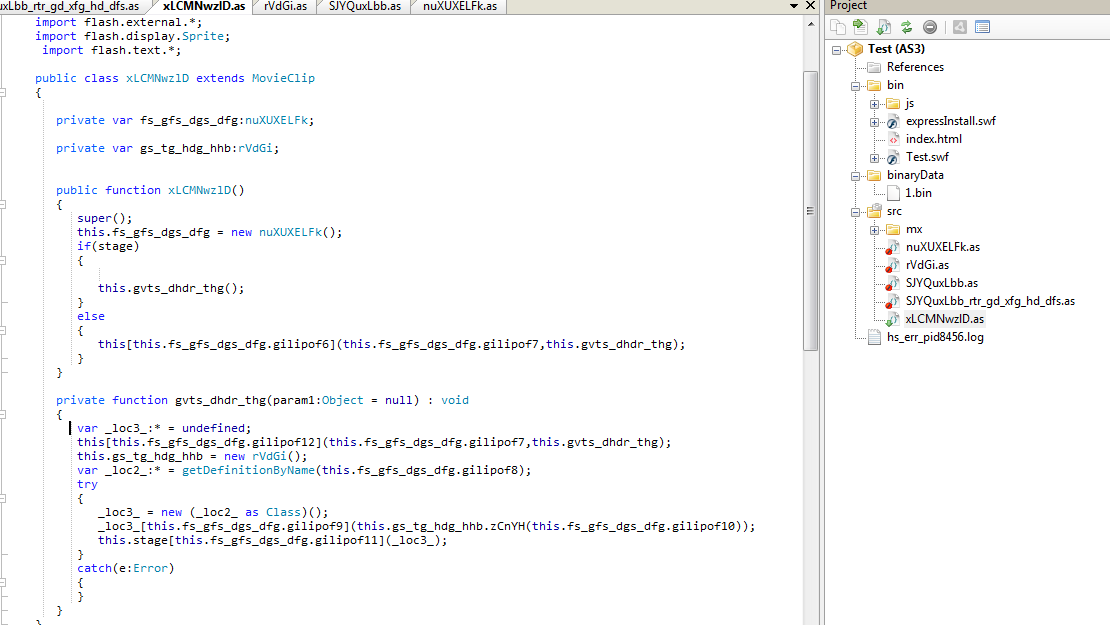
As you can see, the sample is heavily obfuscated. While many times, decompilation of obfuscated swf exploits is not perfect, this time it was successful. We used FlashDevelop IDE to ‘debug’ this sample. First we exported the ‘Scripts’ and the ‘binaryData’ section from this exploit and created a new Flex ActionScript project.
This is a typical 2 stage exploit where stage 1 loads bytes from ‘binaryData’ and decrypts it. This decrypted data is the 2nd stage SWF file which actually contains the exploit. We can see the key being passed to the decrypt routine:

This decrypt routine returns a Bytearray which contains stage2 SWF file. We used Actionscript’s trace functionality to dump this array. A trace statement was injected in the decryption routine to print this array to log file:

The log dumps the bytes

Looking at it in a hex view, we can see a compressed hex file.

Let’s decompile this file:

We can clearly see the vulnerability being exploited.
Sonicwall team has created the following signatures that protects customers from this exploit.
- [GAV] CVE-2015-5119.B_3 (Exploit)
- [GAV] CVE-2015-5119.A_12 (Exploit)
- [GAV] CVE-2015-5119.A_11 (Exploit)
- [GAV] CVE-2015-5119.A_10 (Exploit)
- [GAV] CVE-2015-5119.A_9 (Exploit)
- [GAV] CVE-2015-5119.A_8 (Exploit)
- [GAV] CVE-2015-5119.A_7 (Exploit)
- [GAV] CVE-2015-5119.TTY (Exploit)
- [GAV] CVE-2015-5119.A_6 (Exploit)
- [GAV] CVE-2015-5119.A_5 (Exploit)
- [GAV] CVE-2015-5119.A_4 (Exploit)
- [GAV] CVE-2015-5119.A_3 (Exploit)
- [GAV] CVE-2015-5119.C_2 (Exploit)
- [GAV] CVE-2015-5119.C (Exploit)
- [GAV] CVE-2015-5119.B_2 (Exploit)
- [GAV] CVE-2015-5119.B (Exploit)
- [GAV] CVE-2015-5119.A_2 (Exploit)
- [GAV] CVE-2015-5119.A (Exploit)
- [GAV] CVE-2015-5119.DH_2 (Exploit)
- [GAV] CVE-2015-5119.DH (Exploit)



