Microsoft Windows IE Vulnerability (CVE-2013-3897) attacks spotted in the wild (October 8, 2013)
The Dell SonicWALL Threats Research team observed reports of CVE-2013-3897 vulnerability being actively exploited in the wild. The vulnerability enables attacker to trigger memory corruption in Microsoft Internet Explorer via a crafted web site, allowing the remote attackers to execute arbitrary code upon successful exploitation. Microsoft released security update for this vulnerability and we highly recommend applying these security updates.
Dell SonicWALL customers were proactively secured from the attacks involving this 0-day exploit that started sometime in September, 2013.
Infection Cycle:
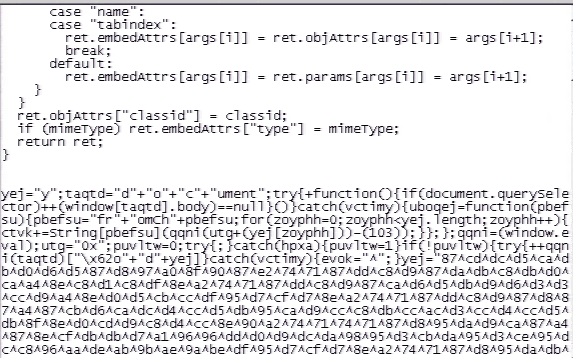
The exploit cycle begins with a highly obfuscated JavaScript being embedded on a compromised site. This JavaScript is responsible for redirecting the user to a remote server hosting the CVE-2013-3897 vulnerability exploit as seen below:


Here is a screenshot of an active exploit page that we captured from the wild:

It uses heap spray and ROP techniques to bypass ASLR and DEP. As seen below it uses unescape function to set up spray and ROP chain for specific targets:

If the exploit is successful, the shellcode will trigger the download of a malicious executable from a remote server. We saw similar attacks targeting CVE-2013-3893 two weeks ago.
The exploit fails on Windows XP even with with the language packs installed as we noticed only crashes.
We specifically reproduced the exploit on IE 8 running on Japanese XP that explains how the ROP gadgets were designed to target specific systems.
The Javascript code below shows shows checks for Japanese or Korean systems.

Debugging shows how the ROP chain is set up and how it executes it.


Which translates to

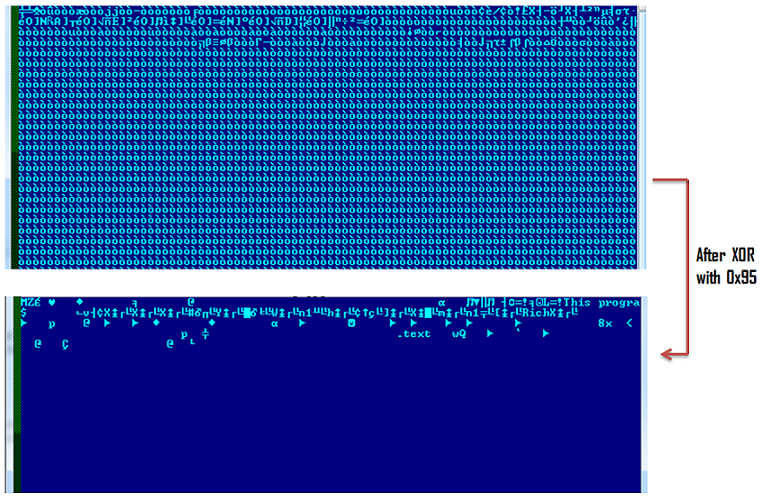
Another similar pattern seen here if we compare it to CVE-2013-3893 exploit, is a set of bytes being ‘xored’ with 0x94

The following bytes were used after a successful run to download and execute a malicious binary.

The downloaded malicious executable further connects to the same server to download another malicious executable pretending to be an image file firw.gif. This file is still actively being served by the remote server at the time of writing this alert.
Dell SonicWALL Gateway AntiVirus proactively blocked these attacks in the wild with the following signature:
- GAV: Shellcode.GEN_12 (Trojan)
- GAV: Magania.FFAD (Trojan)
- GAV: Patched.OX (Trojan)
We additionally have added following signatures to detect the Exploit:
- IPS: 7553 Windows IE Use-After-Free Vulnerability (MS13-080) 7
- SPY: 4684 CVE-2013-3897