OpenSSL X509 Certificate Vulnerabilities
Overview:
SonicWall Capture Labs Threat Research Team has observed the following threat:
The OpenSSL Project develops and maintains the OpenSSL software a robust, commercial-grade, full-featured toolkit for general-purpose cryptography and secure communication. OpenSSL contains an open-source implementation of the SSL and TLS protocols. The core library, written in the C programming language, implements basic cryptographic functions and provides various utility functions.
Overview of OpenSSL Vulnerabilities:
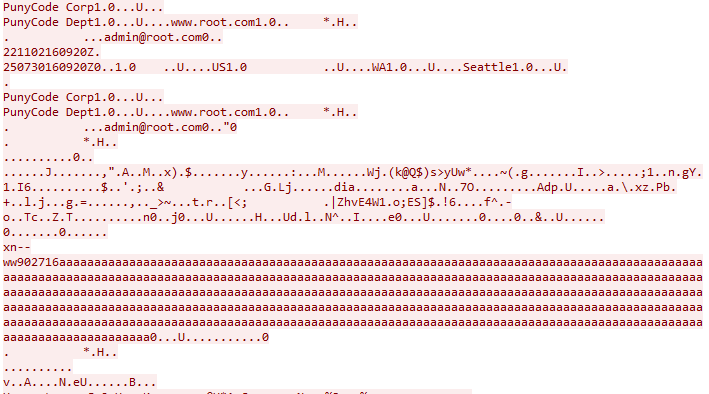
(CVE-2022-3602) ossl_punycode_decode(), punycode domain name “xn--” buffer overflow.
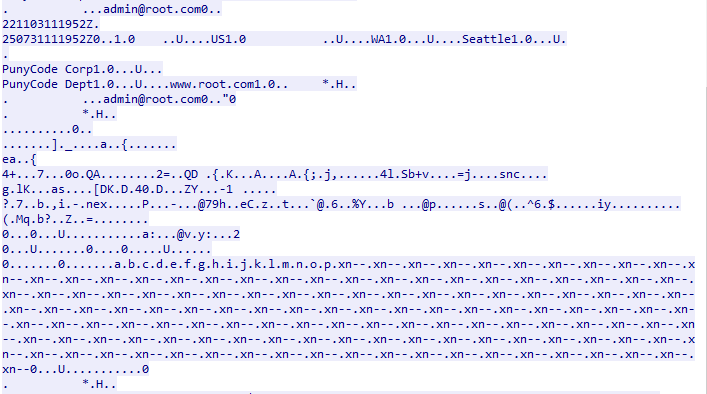
(CVE-2022-3786) ossl_a2ulabel(), punycode string that includes a dot “.” ensuring buffer overflow.
A stack-based buffer overflow can be triggered in the X.509 certificate verification process, specifically in the ossl_punycode_decode buffer.
An attacker can craft a malicious certificate to overflow the ossl_punycode_decode buffer in multiple scenarios. This buffer overflow could result in a DoS(Denial of Service) or potentially RCE(Remote Code Execution).
CVE Reference:
The vulnerabilities have been assigned the Common Vulnerabilities and Exposures (CVE) identifiers:
Common Vulnerability Scoring System (CVSS):
CVE-2022-3602 – Base 10.0 (AV:N/AC:L/Au:N/C:C/I:C/A:C), Temporal 7.8 (E:POC/RL:OF/RC:C).
CVE-2022-3786 – Base 7.8 (AV:N/AC:L/Au:N/C:N/I:N/A:C), Temporal 5.8 (E:U/RL:OF/RC:C).
Technical Overview:
Related to CVE-2022-3602:
The vulnerability is due to a 4-byte (32-bit) buffer overflow that is caused by an off-by-one error inside OpenSSL’s Punycode library (ossl_punycode_decode) in punycode.c, where the “max length” argument (unsigned int *pout_length) is the number of elements allocated and not verified if out of bounds. The vulnerable function ossl_punycode_decode() is responsible in parsing all sub-domains starting with “xn--“. That means that any Punycode string that decodes to exactly one more 32-bit character than the maximum length will overwrite the memory immediately following the decoded string.
Related to CVE-2022-3786:
The vulnerability exists in the ossl_a2ulabel function within punycode.c, The vulnerability is due to improper validation of Punycode encoded strings. Memory addresses stored right after the buffer, causes a partial address overwrite that might lead to an exploitable memory corruption. The code is mostly contained in a infinite while loop, which processes each label (ie, the portions of the name between periods) until it runs out. If the label does not start with xn-- (ie, it’s a standard label), it’s basically copied directly into the output buffer. If the label does start with xn--, the else statement executes, and it decodes the punycode encoded string using the vulnerable ossl_punycode_decode function.
The vulnerable Punycode functions are apart of the libcrypto.so shared library. (also libcrypto.a) They’re accessible through certificate-validation functions after certificate validation. In a trusted certificate, this can potentially affect any client application running a vulnerable server version of OpenSSL.
Triggering the Problem:
• The target must have the vulnerable software installed.
• The attacker must have network connectivity to the target server.
Triggering Conditions:
TLS Connections:
Normal Client/Server handshake connection. (Server sends Certificate)
Mutual Authentication handshake connection. (Server sends Certificate and Server Asks For Client Certificate)
Attack Delivery:
The following application protocols can be used to deliver an attack that exploits this vulnerability:
• SSL/TLS transport mechanisms such as (HTTPS, SMTPS, SIPS, etc…)
SonicWall’s, (IPS) Intrusion Prevention System, provides protection against this threat:
• IPS: 3332 OpenSSL X.509 Name Constraint Check Buffer Overflow
• IPS: 3335 OpenSSL X.509 Name Constraint Check Buffer Overflow 2
Remediation Details:
The risks posed by this vulnerability can be mitigated or eliminated by:
• Upgrading the product to a non-vulnerable version.
• Detecting and filtering malicious traffic using the signatures above.
The vendor has released the following advisory regarding this vulnerability:
Vendor Advisory