Apex Legends for Android – Spyware, Adware, Verification Scams and more
Fortnite was the gaming phenomenon of 2018, we used the word “was” because another title has replaced Fortnite as the new champion – Apex Legends. This game has been raking up the numbers in terms of popularity and the sheer amount of people playing this game at the same time. But in the security world – fame usually lead to scams surrounding the commodity.
YouTube, websites and now Android are being bombarded with scams that surround the name – Apex Legends – with the sole purpose of making this the new Trojan Horse which would deliver malicious content to unsuspecting victims.
SonicWall Threats Research Team has been observing a number of scams for Apex Legends since its launch and below are few highlights of these findings:
YouTube scams
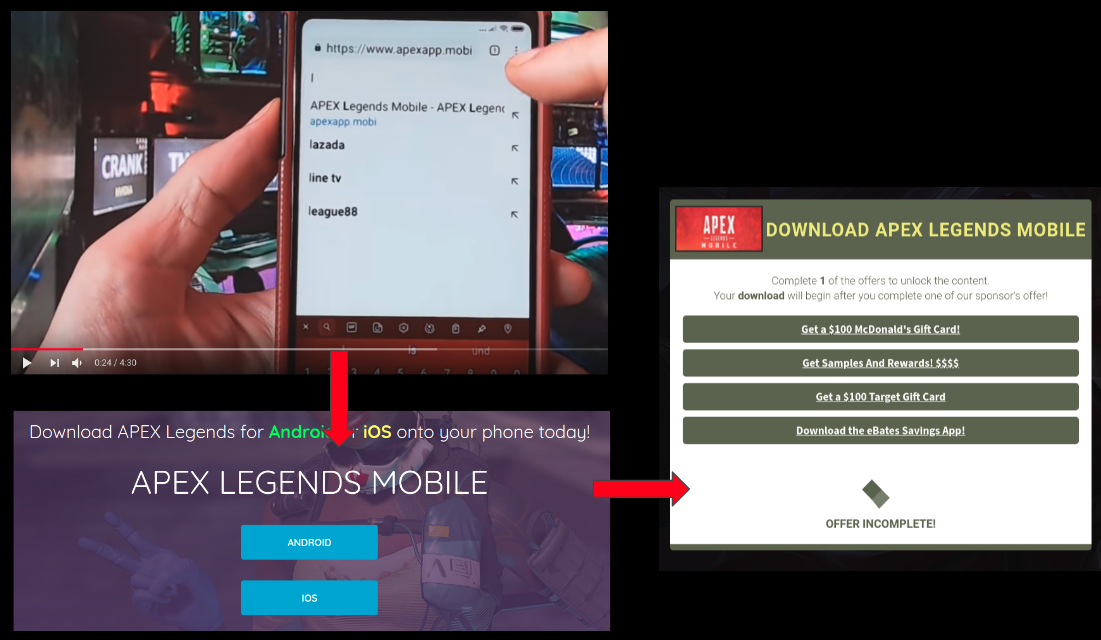
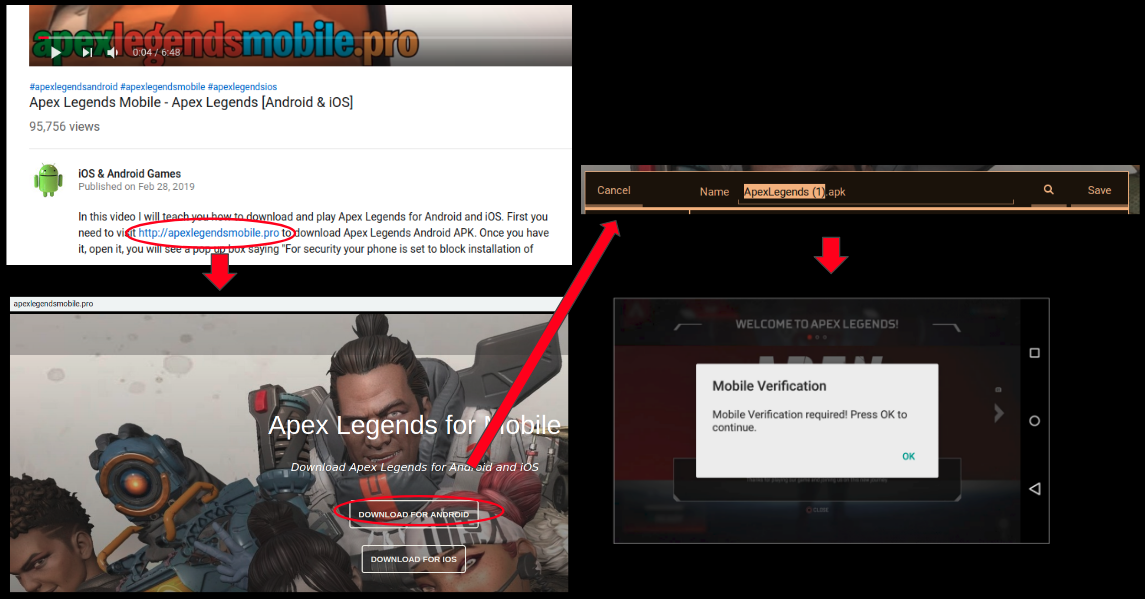
There are a number of Youtube videos that claim Apex Legends can be installed on Android and IOS devices but in reality they just lure victims into clicking suspicious links. These links are usually suspicious phishing pages which duplicate the look and feel of Apex Legends website by using similar/same assets.
Once the victim visits this page he is asked to perform an action, this action varies based on the scam. Below are three examples of what we usually observe in a YouTube scam for such popular games:
- Victim get redirected to Fake survey pages after opening the link given in the Youtube video:
- Victim has to share a post on Facebook and only then can he unlock the download page (which leads to a survey page)
- Victim downloads an apk but the apk is not the game but is something else (verification scam in this case, we will touch more on this later in the blog):
Android scams
The Android ecosystem is no stranger to game-based scams, last year we saw a number of scams for Fortnite which were covered in our blog. We are now observing similar scams for Apex Legends as well.
Verifiation based scams
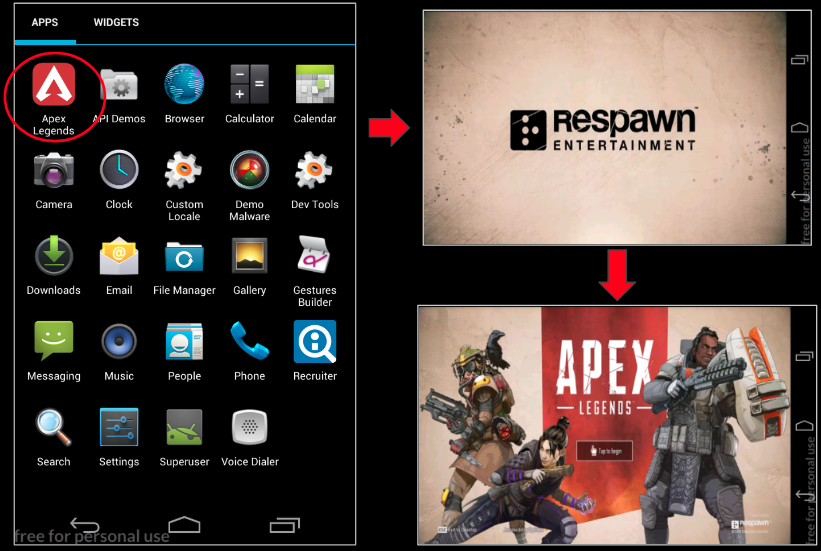
Verification based scams are prevalent on the Android ecosystem as well. For instance, lets look at an Android apk with the application name Apex Legends – MD5: 2620c79372d30f99a667854ff8f3d52a Package name: com.bo4mobi. We see the Apex Legends icon after installation and screens similar to the original game after the app gets executed:
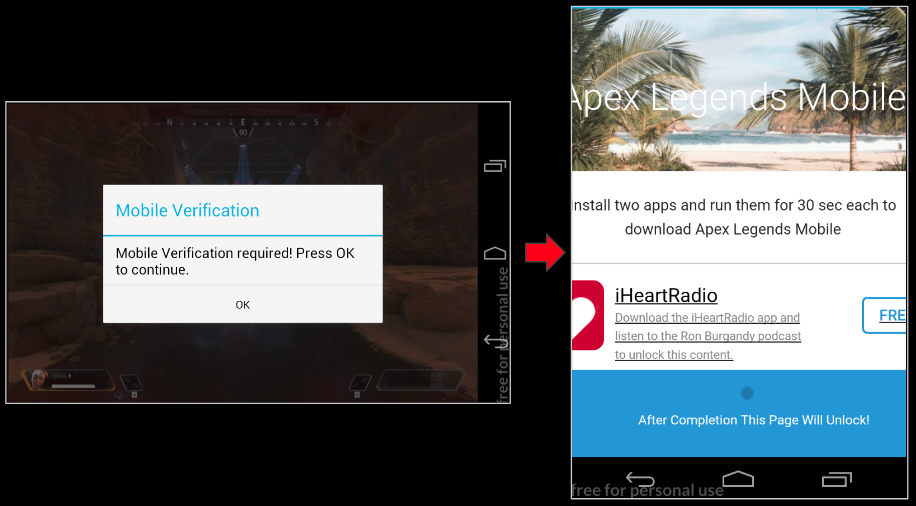
After a short delay as soon as we feel that the game is about to start we see the dreaded “verification required” screen. Upon clicking the OK button we are redirected to a website that asks us to install few apps before the game gets unlocked (which never happens):
The domain we were redirected to was – verifycaptcha.com – and upon doing some VT investigations we found many other gaming related apps linked to this domain hinting towards similar verification scams for other games as well: 
Adware
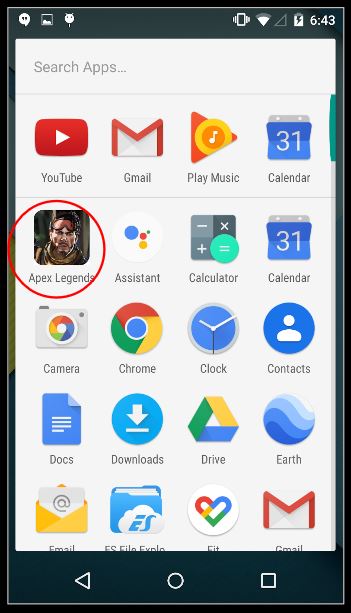
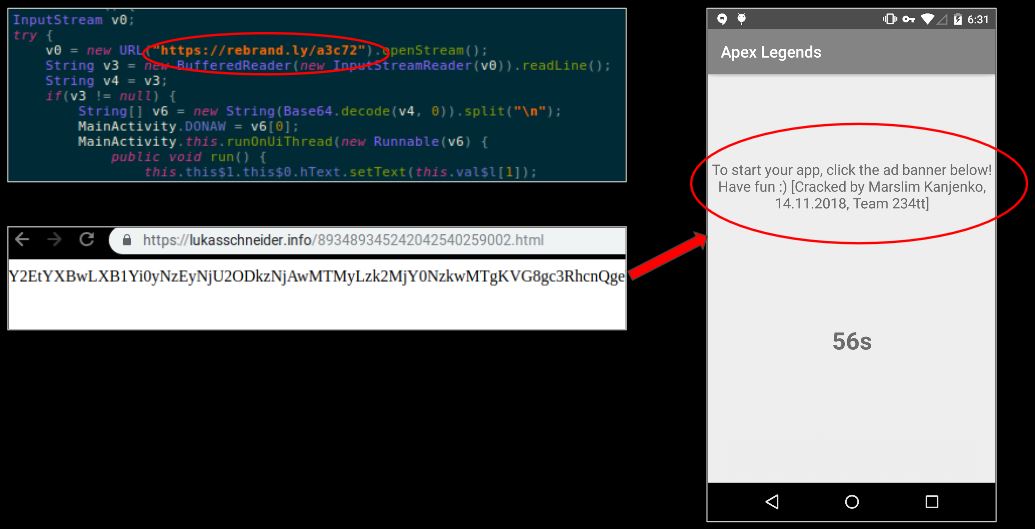
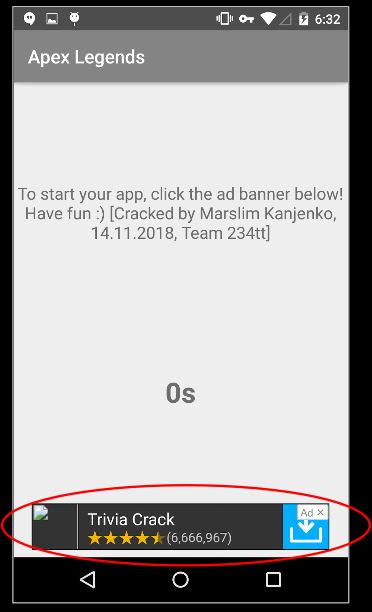
We came across a sample named Apex Legends – MD5: 057eb20bab154b67f0640bc48e3db59a and Package name: com.mt.gb.hd that shows the icon of an Apex Legends character post installation:
Upon execution we see a message on the screen stating that we need to click an advertisement to proceed further. To get this message, the app contacted a domain h[xx]ps://rebrand.ly/a3c72 which later redirected to h[xx]ps://lukasschneider.info/893489345242042540259002.html that contains a Base64 encoded line . This line was extracted, decoded and displayed on the screen:
Once the time runs out an advertisement is displayed and according to the author after clicking the advertisement the victim can play Apex Legends. However to his benefit the victim just gets redirected to the advertisement and ends up making ad-money for the author:
Even though this app is not malicious in itself it does mislead the user and ends up making money for the author via advertisements.
Spyware
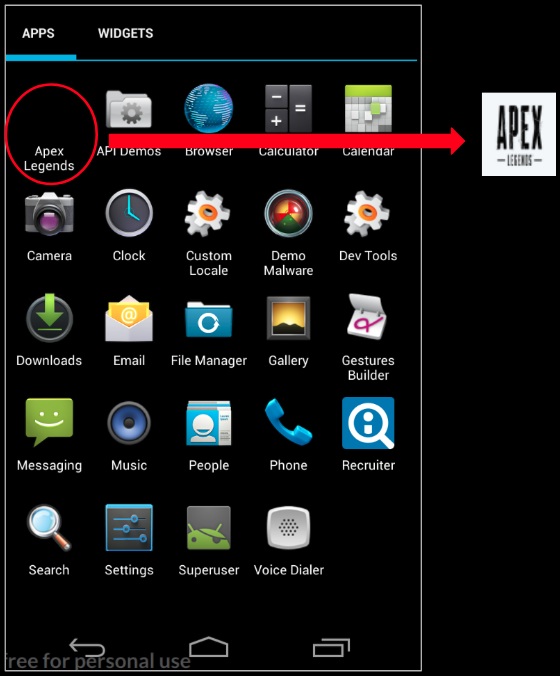
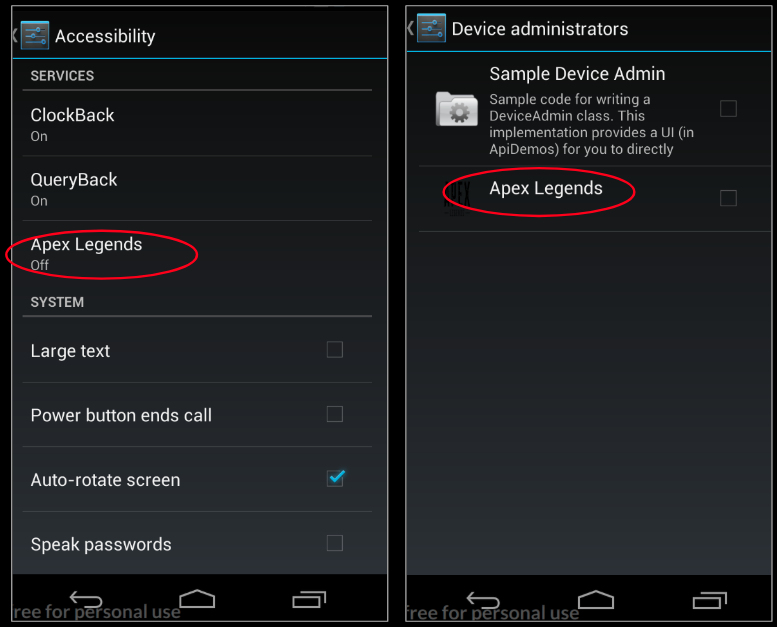
We observed a sample named Apex Legends – MD5: 253489a49d14719a4c29dc0f5e9f9c79 and Package name: yps.eton.application – it shows a different yet believable icon after installation:
Upon execution we are shown the accessibility screen with an entry for Apex Legends. Usually when a malware wants the victim to grant such privileges it comes up with a fake yet somewhat believable story to convince the user to do so. But in this case perhaps the story part did not work for us during our analysis. Same goes for device administrator privileges:
Code examination of the sample reveals that this sample is actually a potent Spyware which has been around for a while. Few key capabilities of this Spyware are as follows:
- This spyware can extract sensitive information from the device:
- Device information – Model, brand, serial number and more
- Information about the SIM – serial number, country name, phone number
- Contacts information
- Call Logs
- SMS present on the device
- View pictures on the device
- Find location related data from the device
- The spyware can perform a number of functions on the device which an Android spyware typically performs:
- Make phone calls
- Record audio
- Send SMS
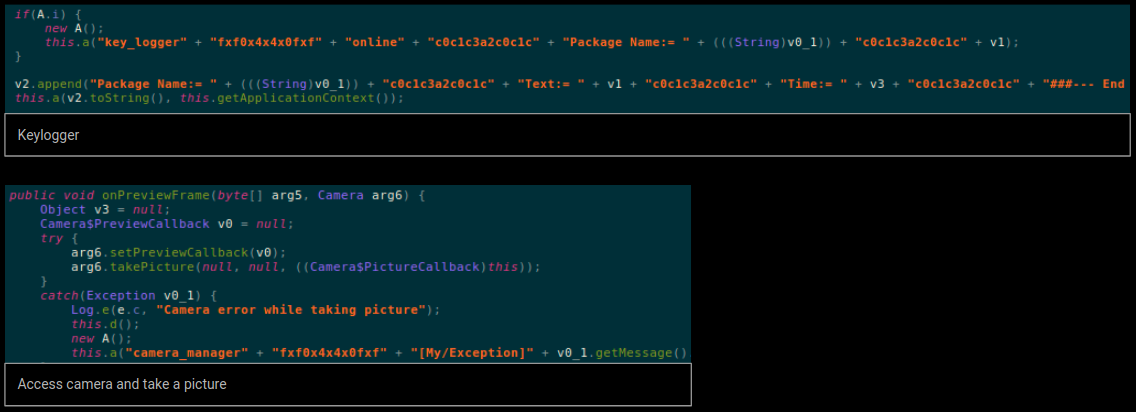
- Take photos from the camera
- Record videos from the camera
- Record keystrokes (keylogger)
- Check if the device is rooted
- Start the spyware each time the device reboots
Few snippets from the code:
Upon further investigations we saw this package name being mentioned in a forum where people were discussing about the workings of an Android RAT named SpyNote.
Miscellaneous scams
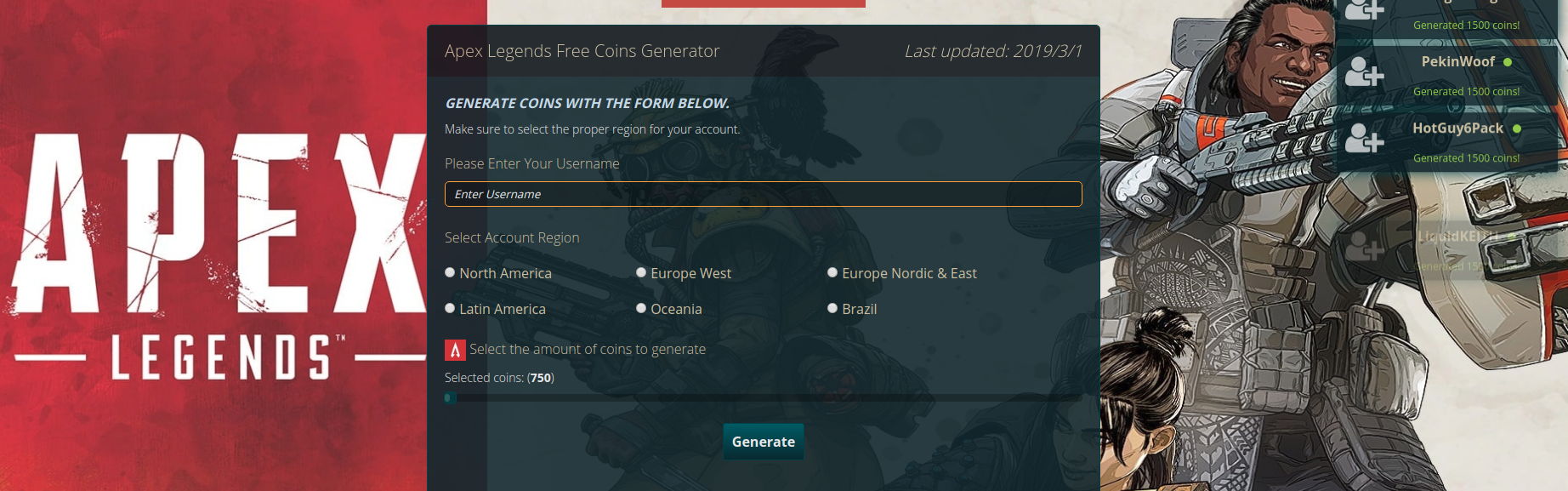
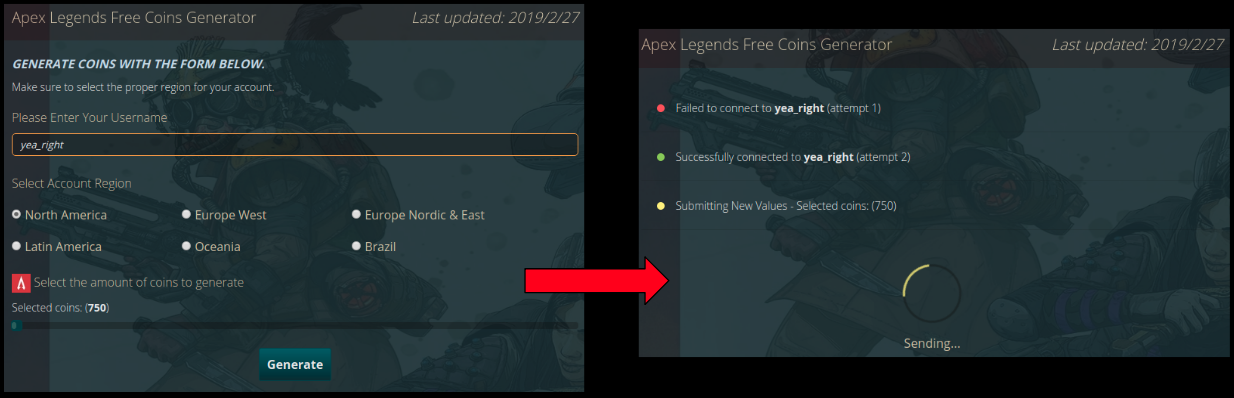
On a lighter note there is a website h[xx]p://cbldc.io/4efe9a5 that claims to generate coins for Apex Legends – which is an in-game currency used to purchase cosmetic upgrades:
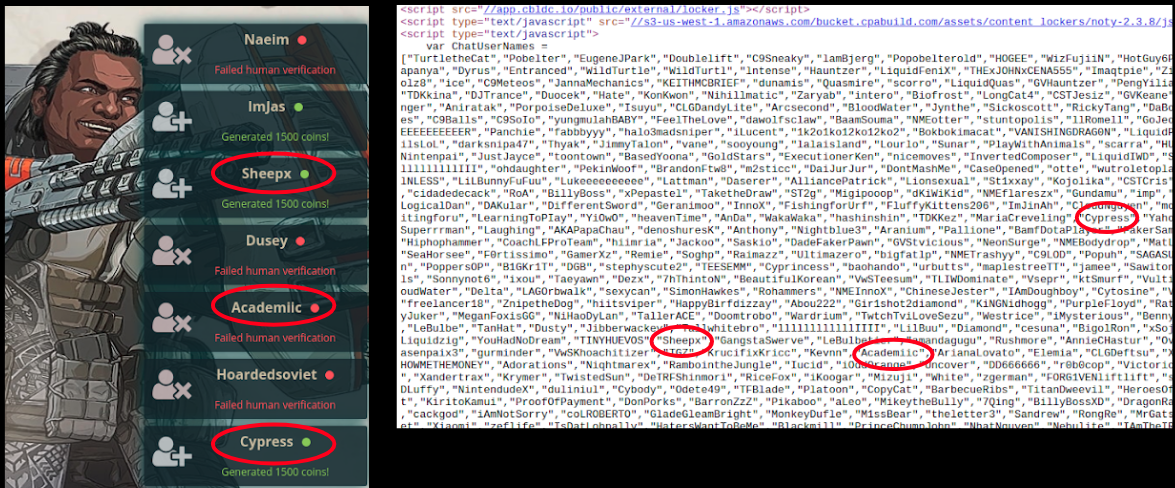
This site constantly shows updates of users generating coins on the right side. If we look at the code of this page and search for the usernames, we can see a list of those that appear on the website. The site simply goes through this list and shows us a fake update:
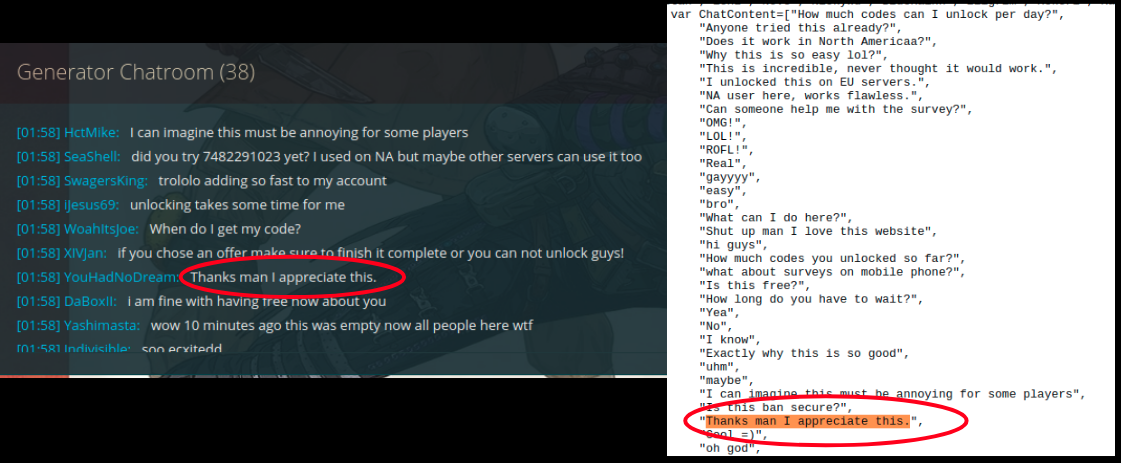
Same goes for the chat shown on the website:
We tried generating coins for ourselves using a fake username:
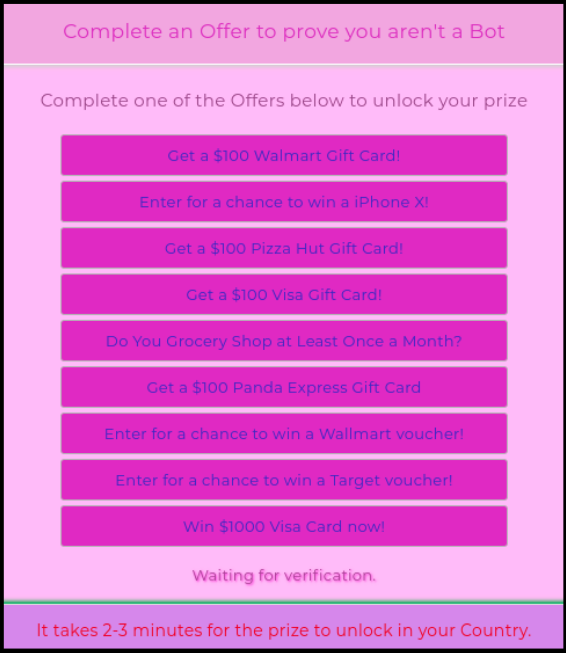
As expected it led us to a fake survey link:
See what sticks
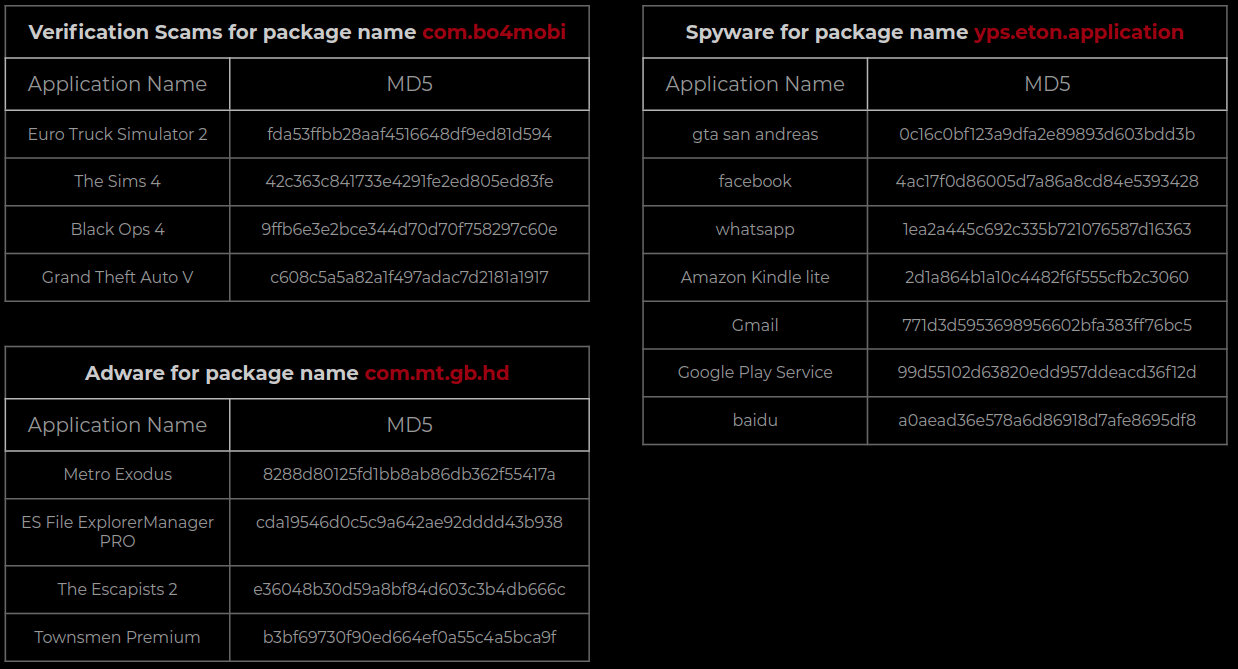
Throughout our analysis we observed that a developer for an Apex Legends fake app also has fake apps for a number of different popular applications. This helps us understand the mindset of some of the malware writers. They try to re-package their creations to look like popular applications in an effort to increase the chances of their infections. Basically – throw everything at the wall and see what sticks.
Below screenshot shows popular apps with same package name for different types of scams, adware and spyware:
Overall this post was a round-up of popular scams related to Apex Legends. The popularity of this game is being misused by malware writers to further their objectives. We urge our readers to be vigilant of apps that make use of the name Apex Legends or the next popular thing after this game.
SonicWall Capture Labs provides protection against this threat via the following Gateway Antivirus signatures:
- GAV: AndroidOS.Verification.PG (Trojan)
- GAV: AndroidOS.SpyNote.SP (Trojan)
- GAV: AndroidOS.AdwareDec.AL (Trojan)
Indicators of Compromise (IOC’s):
- Verification Scam:
- 4e37fe6a140b64a281e2ea08b2c116f0
- fda53ffbb28aaf4516648df9ed81d594
- 2620c79372d30f99a667854ff8f3d52a
- 42c363c841733e4291fe2ed805ed83fe
- Spyware
- 22649508c8056351c6ad3a760c39ba39
- 3b452e48a4e34e1749daff64a9f32103
- c50ba073c878602a9d1341db2909aa76
- 31672c86ecc67b9875a863bcb393b203
- fd1af1966792aff23856a6cf58db38b2
- 0c16c0bf123a9dfa2e89893d603bdd3b
- Adware
- 057eb20bab154b67f0640bc48e3db59a
- cda19546d0c5c9a642ae92dddd43b938
- e36048b30d59a8bf84d603c3b4db666c
- 8288d80125fd1bb8ab86db362f55417a