Ramnit delivers XMRig Monero Miner
The SonicWall Capture Labs Threat Research Team have come across a variant of the Ramnit trojan dropping a Monero Cryptocurrency miner onto the infected system. As cryptocurrency prices continue to drop (at the current time of writing), malware authors are still betting on its future success as they steal CPU resources in order to generate long term profits.
Infection Cycle:
The Trojan drops the following files on the infected system:
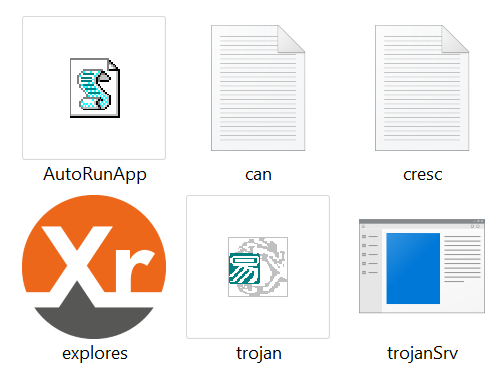
- explores.exe [Detected as: GAV: XMRig.XMR_3 (Trojan)]
- cresc.log
- can.log
- AutoRunApp.vbs
- <originalfilename>Srv.exe [Detected as: GAV: Ramnit.XMR (Trojan)]
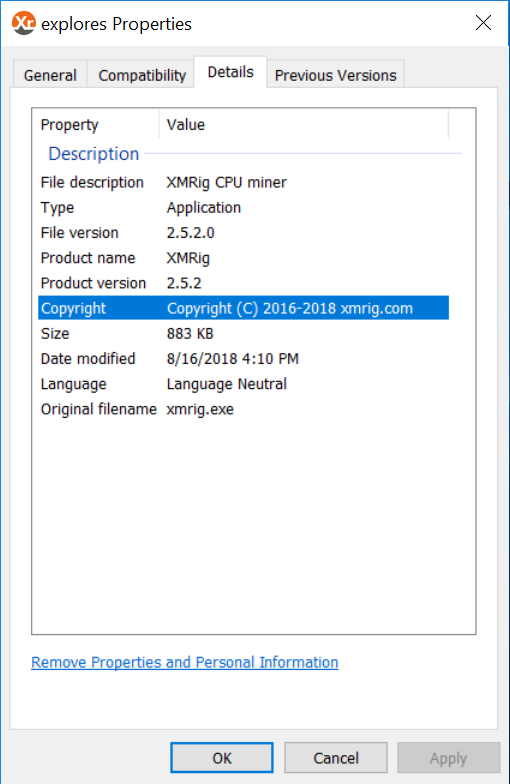
explores.exe and the original Ramnit trojan executable file contain the following metadata:

AutoRunApp.vbs contains the following autorun script:

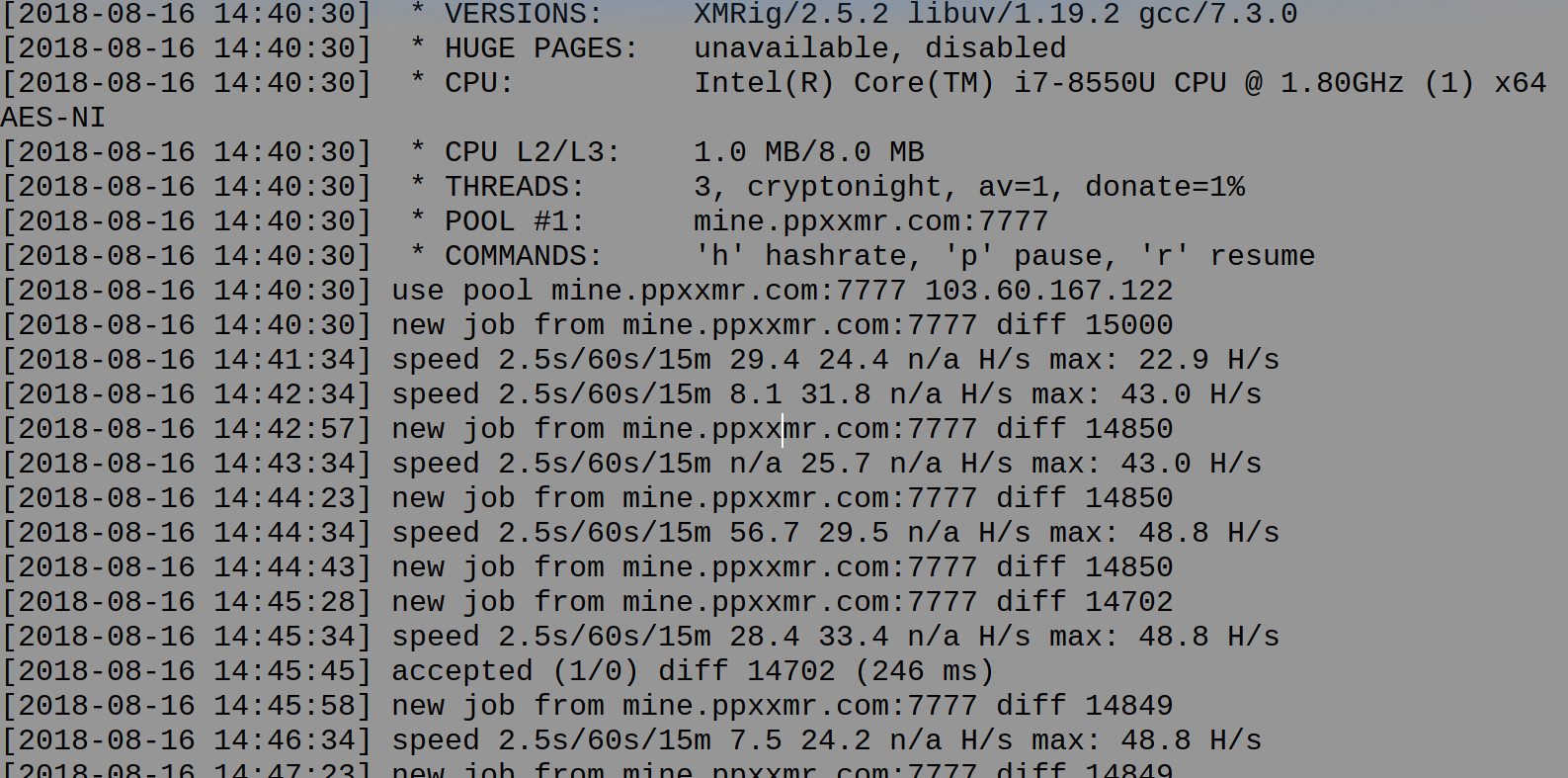
can.log and cresc.log both contain the following log data. This file is populated with mining job info and stats when mining is in progress:
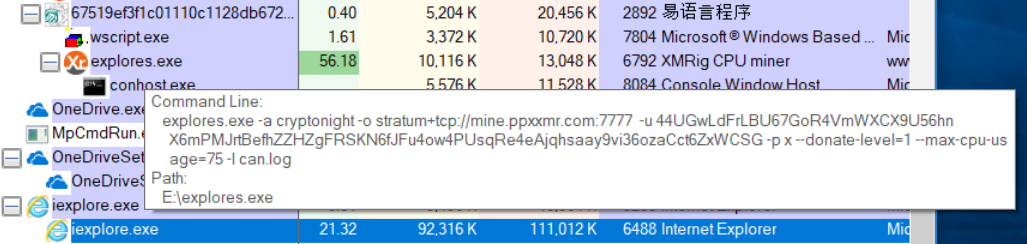
explores.exe can be seen using considerable cpu power whilst mining is in progress:
Mining transaction data can be seen between the miner (explores.exe) and the mining pool at mine.ppxxmr.com:

Sonicwall Capture Labs provides protection against this threat via the following signatures:
- GAV: XMRig.XMR_3 (Trojan)
- GAV: CoinMiner.MN_3 (Trojan)
- GAV: CoinMiner.MON (Trojan)
- GAV: Ramnit.Z (Trojan)
- GAV: Ramnit.MN (Trojan)





