UselessDisk: A fake ransomware bootlocker
DescriptionThe SonicWall Capture Labs Threat Research Team have come across a fake ransomware Trojan that functions as a bootlocker. It is named Uselessdisk because of the debugging symbols and project name strings that the developer has left in the executable file. Its aim is simple: render the system unbootable and pretend that files on the system have been encrypted. Ask for $300 USD in bitcoin for file recovery.
Infection Cycle:
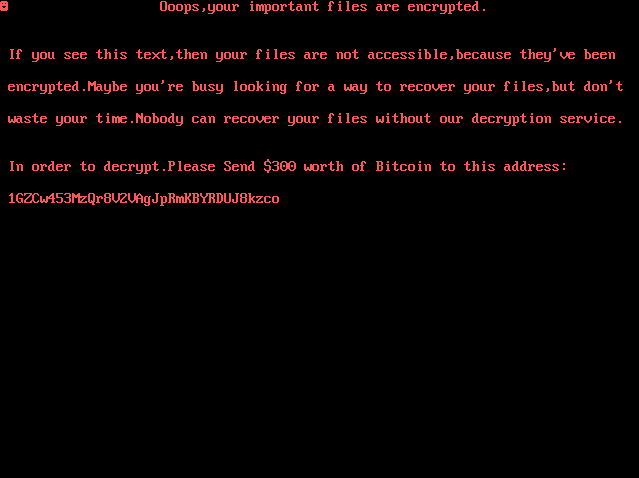
Upon running the malware, it quickly reboots the machine and displays the following message:
Usually the process of encrypting files takes at least a few seconds so we were suspicious when this malware claimed to achieve this so quickly. We were doubtful as to whether any encryption was actually taking place at all. Running the malware through a debugger and analysing its behavior confirmed this doubt.
The Trojan is quite simply, a boot locker. Its first step is to acquire direct access to the physical drive by using the CreateFileA API to open “\\.PHYSICALDRIVE0”. It also attempts to lock the volume for exclusive access to the drive by using the IO control code FSCTL_UNLOCK_VOLUME with the DeviceIOControl API call:

These functions only return successful if the Trojan is run in administrator mode. If the above calls return successfully the Trojan then calls WriteFile to overwrite the MBR (Master Boot Record):

This causes the above message to be shown on the screen at boot time and renders the operating system unbootable.
Once the MBR has been overwritten, the Trojan unlocks the volume then uses WinExec to run the shutdown command with arguments to reboot the system immediately:


There are no other file or encryption API functions present in the malware executable.
The Trojan is unlikely to be lucrative. The bitcoin address (1GZCw453MzQr8V2VAgJpRmKBYRDUJ8kzco) has received no transactions yet at the time of writing this alert:

SonicWALL Gateway AntiVirus provides protection against this threat via the following signature:
- GAV: UselessDisk.RSM (Trojan)




