Microsoft Word Zero Day(CVE-2014-1761) Exploit Analysis (Apr 4, 2014)
Dell Sonicwall Threat research team has spotted Microsoft Word Zero Day attacks in the wild.
Last week, Microsoft released a Security Advisory that addresses this vulnerability.
Following is the Technical Analysis of this attack.
The attack comes down as a malicious RTF file.

Minimum crash file showed following crash

We can see how ROP chain is constructed using MSCOMCTL.
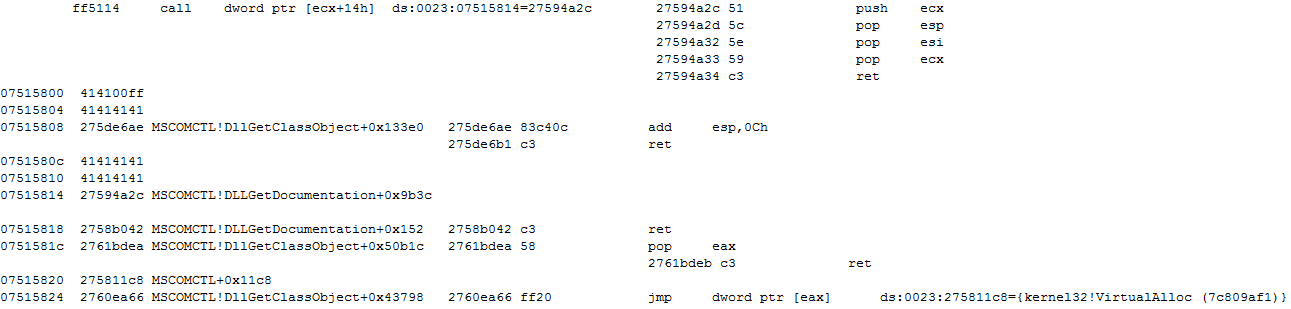
VirtualAlloc is used to create an executable page

Now it returns back to ROP Chain.

More ROP Gadgets, navigate control to Shellcode
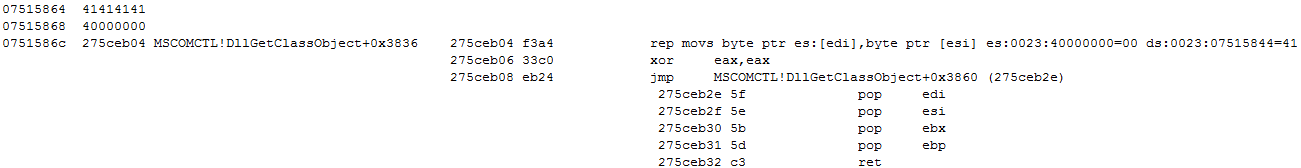
Shellcode takes control from here on.

On successful execution, we can see how svchost is spawned by word.

Following is our Detection Coverage.
- GAV: CVE-2014-1761 (Exploit)



