JavaScript is a scripting language widely used for client-side web development. It is so popular that most of the web pages on the Internet have JavaScript codes. The JavaScript provides a lot of functionalities and flexibilities to the users. However, it has also provided the convenience for the attackers to inject JavaScript code, exploit and control the target servers.
JavaScript Injection has multiple implementations, including JavaScript cookie modification, JavaScript HTML Form modification and some Cross Site Scripting. For example, the simple injection of the following JavaScript code will eliminate some authorization checks for the malicious user.
javascript:void(document.cookie=”authorization=true”);
Besides the common methods of the JavaScript Injection mentioned above, there is one special JavaScript Injection method which is used only for the shell code injection, we call it JavaScript Code Injection. They are used with the other vulnerabilities as an assistant. But they are more dangerous because the code injected is no longer to be restricted as JavaScript or any scripts, they can be any assembly codes to be running in the system.
One latest example for JavaScript Code Injection is Microsoft IE 0-Day vulnerability found on Dec 9, 2008. The details are here. Some exploits in the wild are using the JavaScript to inject shell codes, then exploiting the vulnerability to trigger the injected codes to be executed. The injected code is like the following:
var shellcode = unescape(“%ue8fc%u0044%u0000%u458b%u8b3c%u057c%u0178%u8bef%u184f %u5f8b%u0120%u49eb%u348b%u018b%u31ee%u99c0%u84ac%u74c0%uc107%u0dca %uc201%uf4eb%u543b%u0424%ue575%u5f8b
After carefully checking a lot of injected shell codes and related vulnerabilities for the patterns, SonicWALL UTM team has developed seven signatures for JavaScript Code Injection attempts. They are listed as bellow:
- 3127 Javascript Code Injection Attempt (Mac)
- 4665 Javascript Code Injection Attempt (Win/Linux) 2
- 4701 Javascript Code Injection Attempt (Win/Linux) 3
- 4744 Javascript Code Injection Attempt (Win/Linux) 4
- 4760 Unicode Javascript Code Injection Attempt 1
- 4761 Unicode Javascript Code Injection Attempt 2
- 5051 Javascript Code Injection Attempt (Win/Linux) 5
The signatures listed above have not only detected the existing vulnerabilities, but also proactively prevented a lot of attacks addressing zero-day vulnerabilities, including the Microsoft IE 0-Day Vulnerability found on Dec 9, 2008.
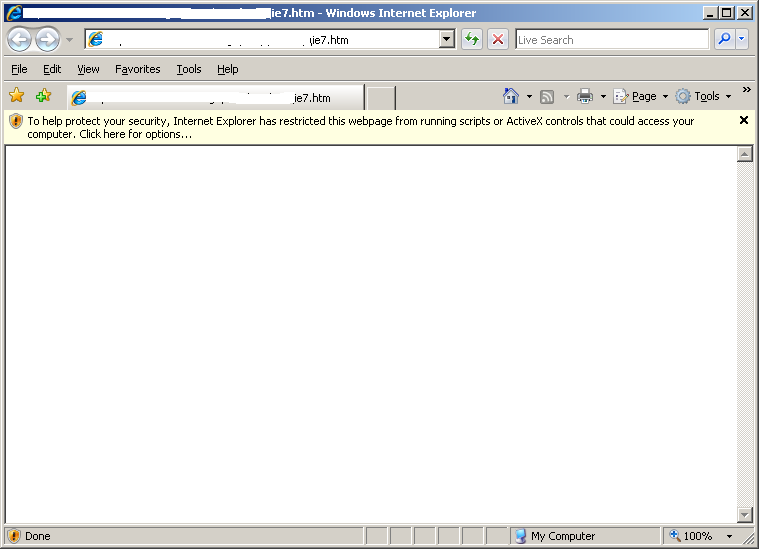
The following figure shows the hits for those signatures within a month.