New Lilith ransomware in early development
The Sonicwall CaptureLabs threat research team has observed reports of the launch of a new ransomware family named Lilith. Lilith ransomware is written in C/C++ and targets 64-bit Windows machines. Encrypted files are marked with a “.lilith” extension. The sample we obtained indicates that it is in early development, as some features reported in the AV community were not present during our analysis.
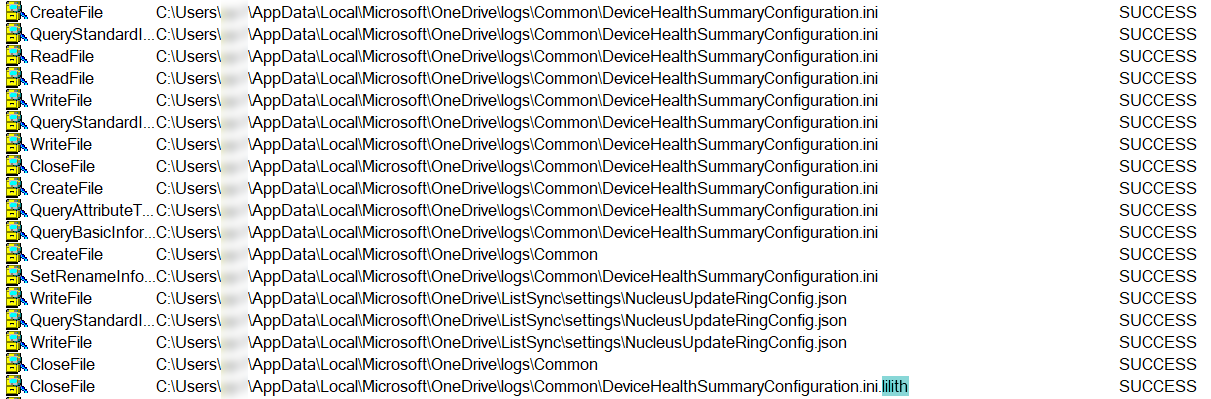
Infection Cycle:
Upon running the executable, files on the system are encrypted
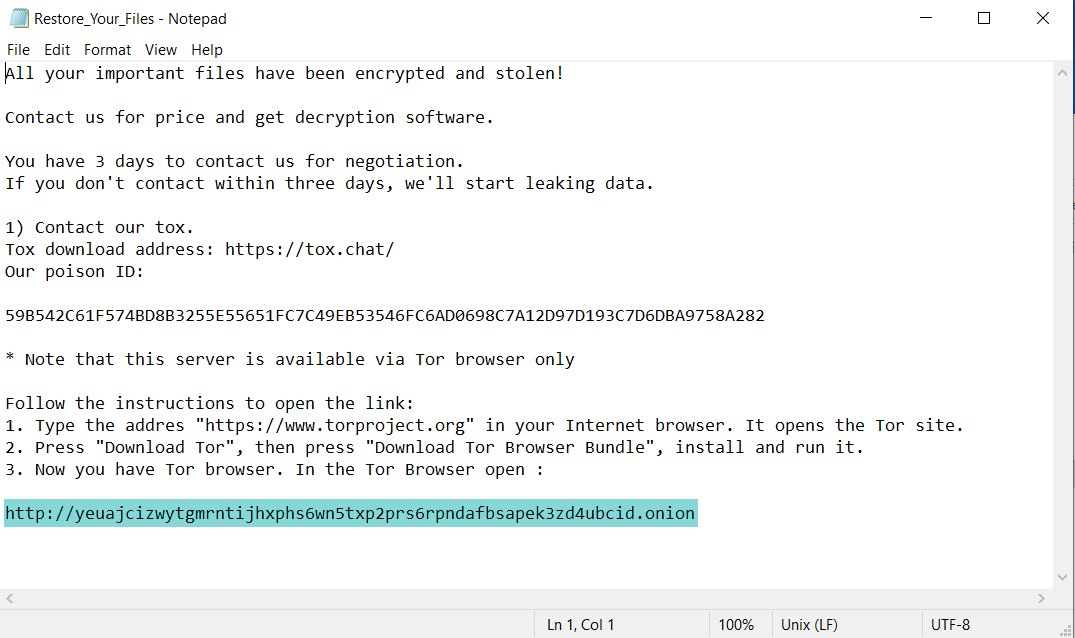
Restore_Your_Files.txt contains the following message:
During our analysis, no data was leaked from the system.
The .onion link leads to the following Lilith home page:
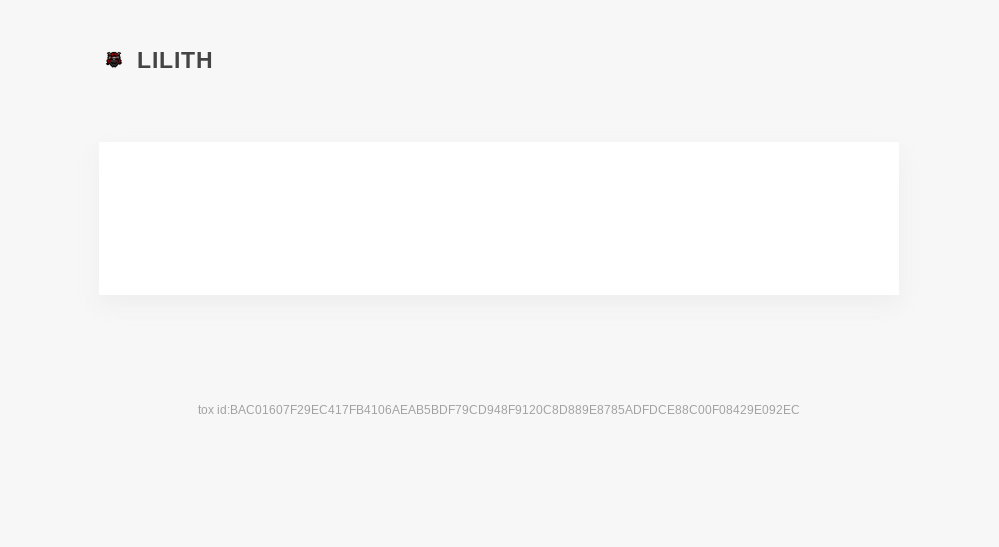
This page appears to be a placeholder and does not contain any functionality yet. It is speculated that this may become an extortion page that threatens to leak victim data.
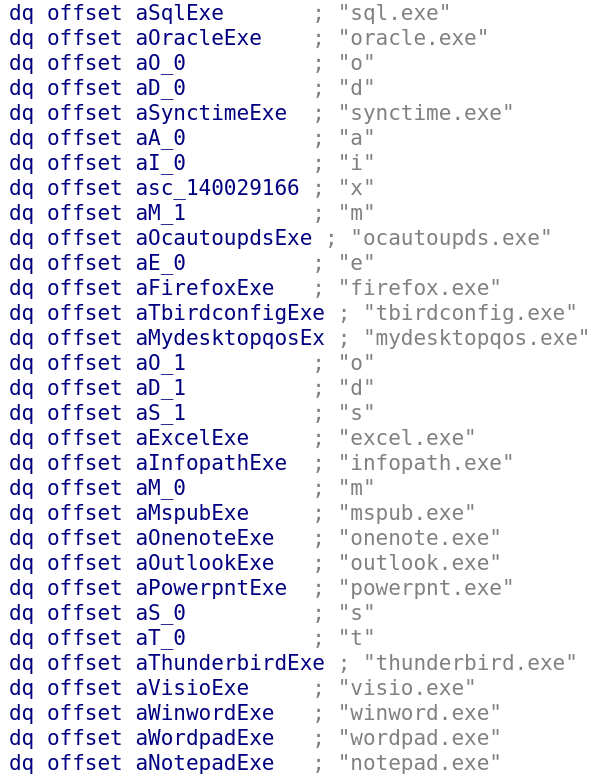
The following programs are terminated if they are running:
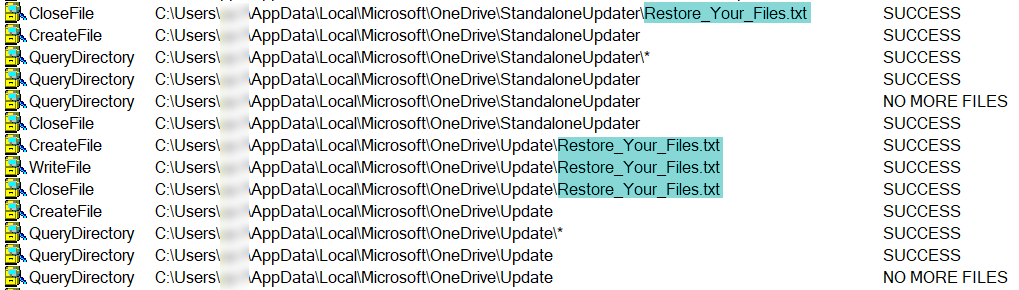
Restore_Your_files.txt is dropped into each directory that contains encrypted files:
Each encrypted file is given a .lilith extension:
We reached out to the operators via the supplied tox ID in the ransom note but received no response.
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: Lilith.RSM (Trojan)
This threat is also detected by SonicWall Capture ATP w/RTDMI and the Capture Client endpoint solutions.




