Command Injection and Local File Inclusion in Grafana: CVE-2024-9264

Overview
The SonicWall Capture Labs threat research team became aware of a critical vulnerability in Grafana, assessed its impact and developed mitigation measures. Grafana is a multi-platform open-source analytics and visualization solution that can produce charts, graphs and alerts according to the data.
Identified as CVE-2024-9264, Grafana versions 11.0.x, 11.1.x and 11.2.x allows an attacker with ‘viewer’ or higher permission to achieve command injection and local file inclusion (LFI) using the experimental SQL expressions feature, earning a critical CVSS score of 9.9. Considering a publicly available proof of concept (PoC) code exists for this vulnerability and the popularity of Grafana, exploitation is more likely in the upcoming days. Hence, users are strongly encouraged to upgrade their instances to the latest applicable fixed version, as mentioned by the vendor in the advisory.
Technical Overview
This flaw was introduced in Grafana 11 through the implementation of an experimental feature called ‘SQL Expressions’, which allows the data source query output to be post-processed by SQL queries. It is accomplished by passing the query and data to the DuckDB CLI in the back end, which then executes the query against the formatted results, called DataFrames. The issue arises due to the SQL queries not being sanitized before execution, which can lead to LFI and command injection.
The affected feature, SQL Expressions, was enabled for the API by default, which is supposed to be disabled otherwise due to its experimental nature. This enables attackers to access the feature by default through the API. The DuckDB binary must be installed (which is not bundled with Grafana) and must be accessible through the Grafana’s PATH environment variable to exploit the vulnerability. This significantly reduces the probability of successful exploitation in default installations.
The patch indicates that the SQL Expressions feature is disabled by default and the references to the DuckDB are removed to address the vulnerability, as seen in Figure 1.
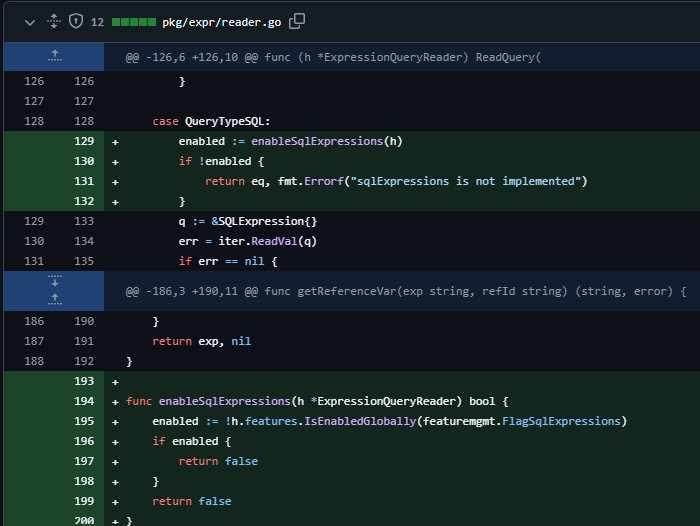
Figure 1: Patch to address vulnerability
Triggering the Vulnerability
Leveraging the vulnerability mentioned above requires the attacker to meet the below prerequisites.
- The system must have installed a DuckDB binary manually and its location must be added to the $PATH variable.
- The attacker must have network access to the target vulnerable system with ‘viewer’ permission or higher.
- The attacker must create a dashboard with Reduce or Math expression, as seen in Figure 2, and modify the expression type to ‘sql’ and inject the malformed SQL expression after intercepting the request.
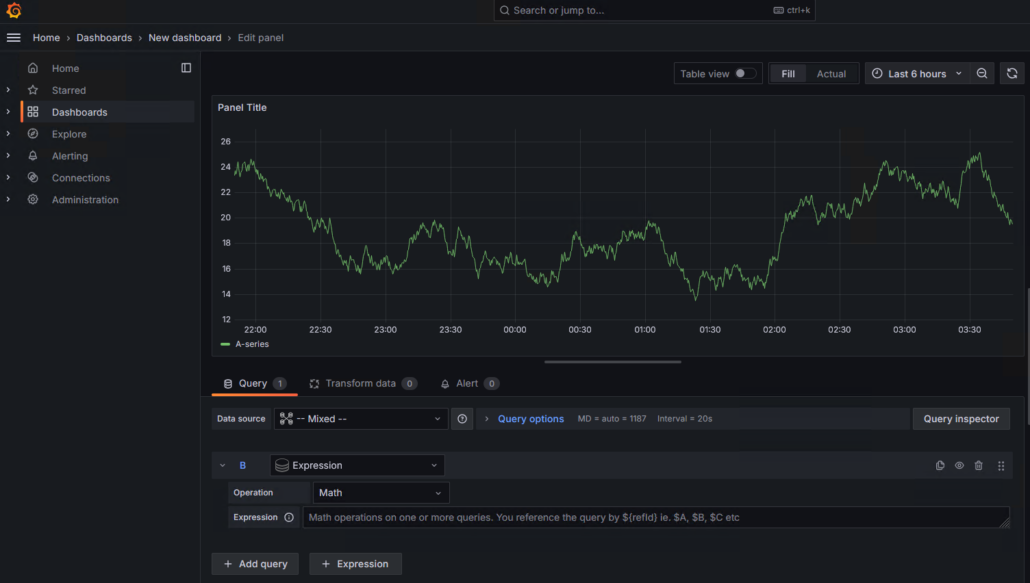
Figure 2: Dashboard with Math expression
Exploitation
Exploiting this vulnerability allows the remote threat actor to execute arbitrary code or read sensitive files on the server. It has a high impact on the confidentiality, integrity and availability of the system and does not require user interaction.
We leveraged publicly available analysis to achieve an LFI on Grafana v11.2.1. As mentioned in step 2 of the above section, the malformed SQL Expression has been injected using the read_csv_auto() function, as seen in Figure 3. It will respond with the contents of the Linux password file.
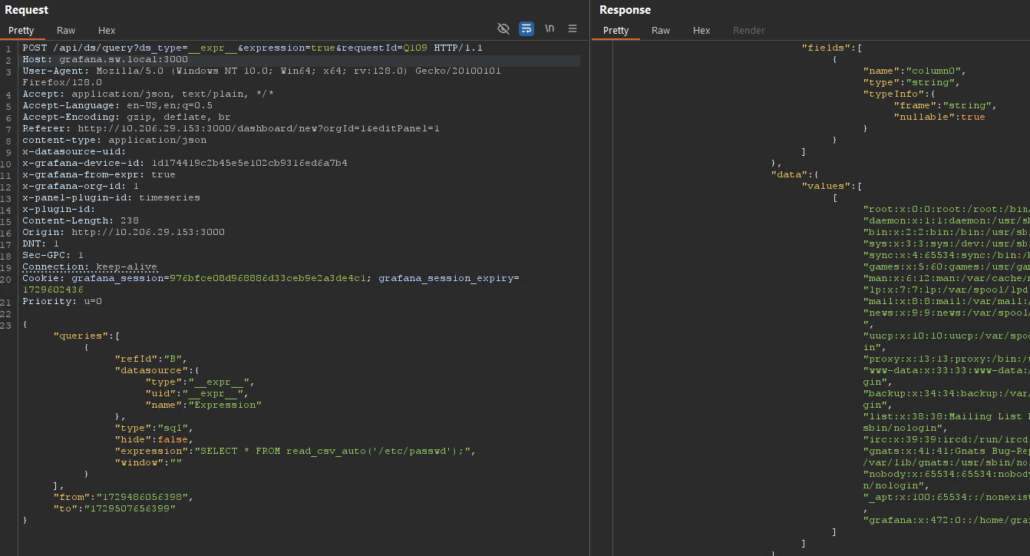
Figure 3: Exploit request for LFI
SonicWall Protections
To ensure SonicWall customers are prepared for any exploitation that may occur due to this vulnerability, the following signatures have been released:
- IPS: 4522 Grafana SQL Expressions Local File Inclusion
Remediation Recommendations
The users of Grafana are strongly encouraged to upgrade their instances to the latest version, as mentioned in the vendor advisory.
Relevant Links
Share This Article

An Article By
An Article By
Security News
Security News