New Orcinius Trojan Uses VBA Stomping to Mask Infection

Overview
This week, the SonicWall Capture Labs threat research team investigated a sample of Orcinius malware. This is a multi-stage trojan that is using Dropbox and Google Docs to download second-stage payloads and stay updated. It contains an obfuscated VBA macro that hooks into Windows to monitor running windows and keystrokes and creates persistence using registry keys.
Infection Cycle
The initial infection method is an Excel spreadsheet, in this case, “CALENDARIO AZZORTI.xls”.
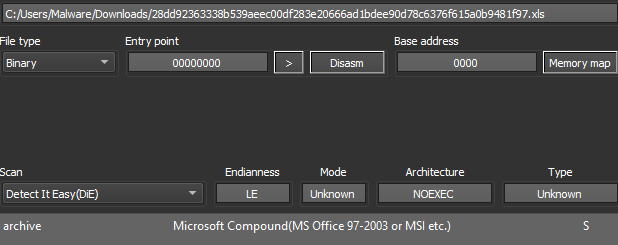
Figure 1: Initial file detection
The file appears to be an Italian calendar with three worksheets that discuss billing cycles in various cities.
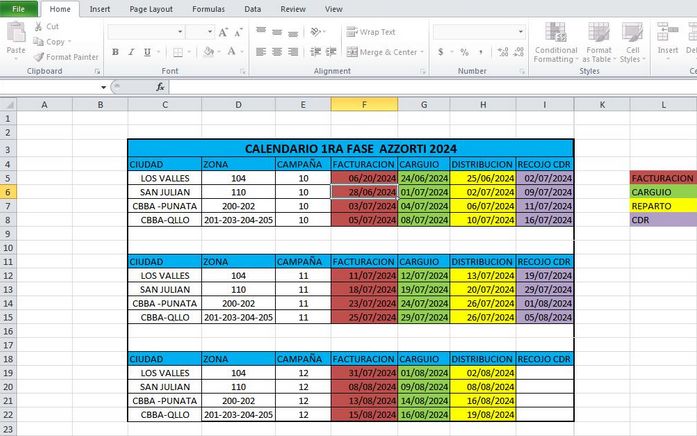
Figure 2: One of the visible sheets seen when opened
The file has a VBA macro that has been modified with a technique called ‘VBA stomping’, where the original source code is destroyed, leaving only compiled p-code. This means that viewing the macro within the document will show either nothing or a harmless version of the code that will run when opening (and closing) the file, as Olevba shows.
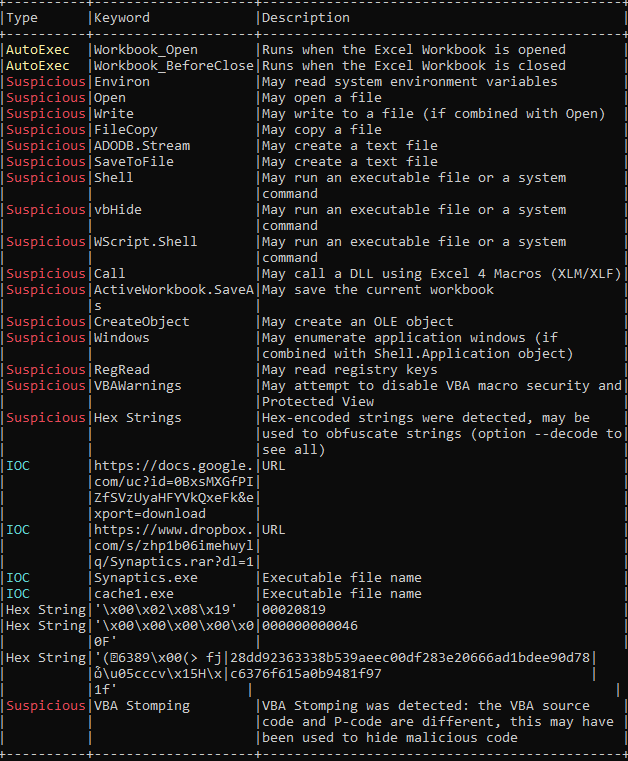
Figure 3: Olevba tool output showing some of the malicious functionality
On runtime, the file will run the macro and perform the following actions:
- Check registry keys and write a new key to hide warnings
- "HKCU\Software\Microsoft\Office\Excel\Security\VBAWarnings"
- "HKCU\Software\Microsoft\Office\Word\Security\VBAWarnings”
- Enumerate windows currently running using EnumThreadWindows
- Set up persistence by writing a key to HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems
- Reach out to both of the encoded URLs and attempt to download using WScript.Shell
- Use SetWindowsHookEx to monitor keyboard input
- Create a number of randomized timers for activation and download attempts
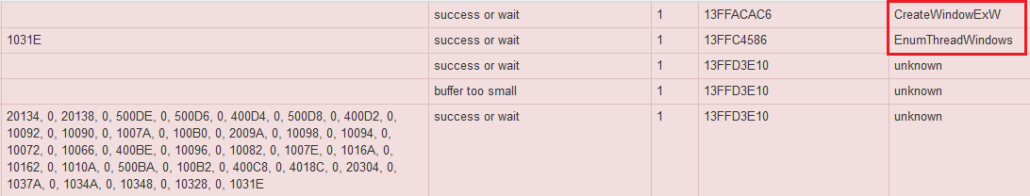
Figure 4: Enumerating running windows
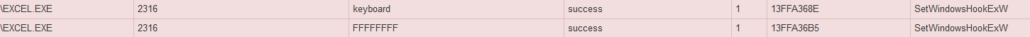
Figure 5: Setting a hook for keyboard monitoring
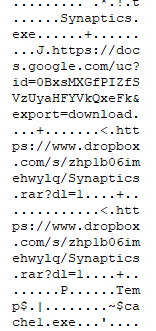
Figure 6: URLs and Synaptics references
There are also references to ‘Synaptics.exe’ and ‘cache1.exe’. This sample and listed URLs have been associated with Remcos, AgentTesla, Neshta, HTMLDropper and others that masquerade as ‘Synaptics.exe’ and can be found on VirusTotal. During runtime, the pages at both addresses were unavailable.
SonicWall Protections
To ensure SonicWall customers are prepared for any exploitation that may occur due to this malware, the following signatures have been released:
- Orcinius
IOCs
28dd92363338b539aeec00df283e20666ad1bdee90d78c6376f615a0b9481f97
URLs
www-env.dropbox-dns[.]com
hxxps://docs.google[.]com/uc?id=0BxsMXGfPIZfSVzUyaHFYVkQxeFk&export=download
hxxps://www.dropbox.com/s/zhp1b06imehwylq/Synaptics.rar?dl=1
Share This Article

An Article By
An Article By
Security News
Security News