Third-Party ICSA Testing – Perfect Score Number 4
SonicWall Capture ATP with RTDMI identified all malicious samples with no false positives — four times in a row.
As those in the cybersecurity industry know, ICSA doesn’t grade on a curve: testing rounds with no perfect scores are common, and the standards are both objective and unforgiving. It’s highly unusual for any vendor solution to identify 100% of malicious threats without flagging a single benign sample.
So when SonicWall’s Capture Advanced Threat Protection (ATP) with patented Real-Time Deep Memory Inspection (RTDMI)™ did just that in Q1 2021, it was quite the accomplishment.
Then we did the same thing in Q2, Q3 and Q4, becoming the first cybersecurity vendor in history to earn four consecutive perfect scores in Standard ICSA Labs Advanced Threat Defense (ATD) testing.
How ICSA Testing Works
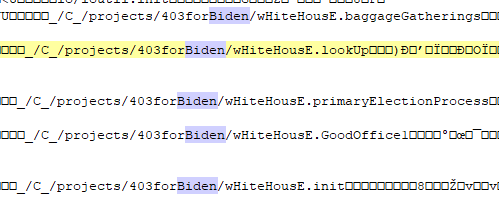
Standard ICSA Labs Advanced Threat Defense (ATD) testing is designed with vendor solutions in mind, and helps determine new threats traditional security products do not detect. Eligible security vendors are tested quarterly for a minimum of three weeks. During that time, the ICSA Labs subjects advanced threat defense solutions to hundreds of test runs. The test set is comprised of a mixture of new threats, little-known threats and innocuous applications and activities.
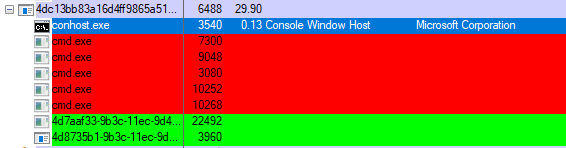
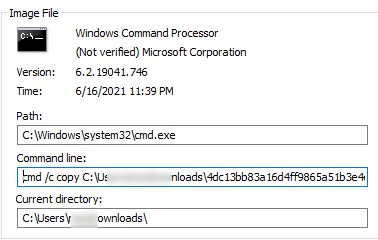
Q4 2021’s testing cycle was particularly rigorous. Over 32 days of continuous testing, a SonicWall NSa 3600 NGFW with Capture ATP was subjected to 1,625 total test runs. During this time, SonicWall Capture ATP detected all 801 of the malicious samples, including the 432 threats that were four hours old or less. The testing also included 824 innocuous apps — none of which were improperly categorized as malicious by Capture ATP.
As a result, SonicWall received the highest ranking in this category, concluding a full year of perfect scores and eight consecutive ICSA certifications for SonicWall Capture ATP.
Capture ATP: Superior Threat Detection
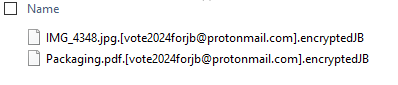
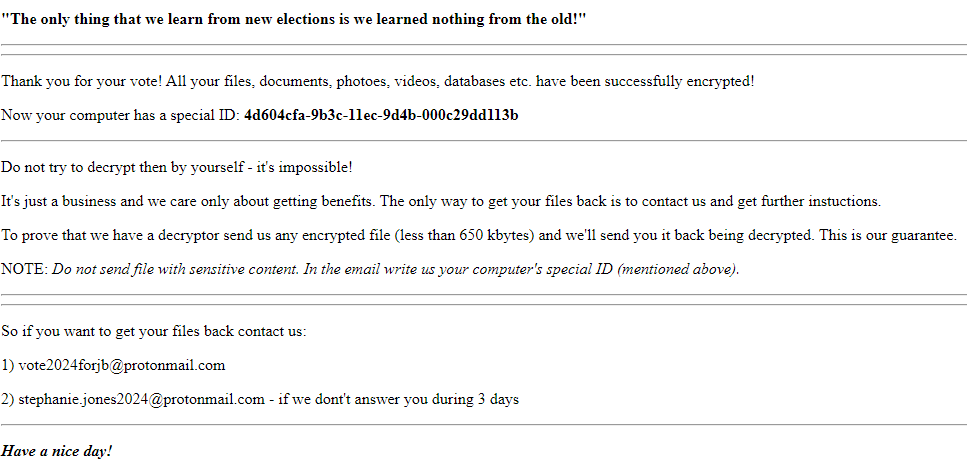
Third-party testing cycles like these become even more important as cyberattacks become increasingly sophisticated and stealthy. The introduction of state-sponsored attacks in particular has changed the game, and what used to be no more than a hobby or a source of secondary income has turned into a full-time job. As a result, we are seeing a slew of complex and refined never-before-seen attacks that are capable of passing through the defenses of many organizations.
This highlights two tenets of modern cybersecurity: the importance of sandboxing technology for a security vendor and the fact that not all technologies are created equally.
SonicWall Capture ATP — a cloud-based service available with SonicWall firewalls — detects and can block advanced threats at the gateway until verdict. This service is the only advanced threat-detection offering that combines multi-layer sandboxing (including SonicWall’s RTDMI™ technology), full-system emulation and virtualization techniques in order to analyze suspicious code behavior.

This combination allows Capture ATP to detect more threats than single-engine sandbox solutions, which are compute-environment specific and susceptible to evasion. And because it incorporates AI and machine learning technologies, it’s constantly becoming more effective.
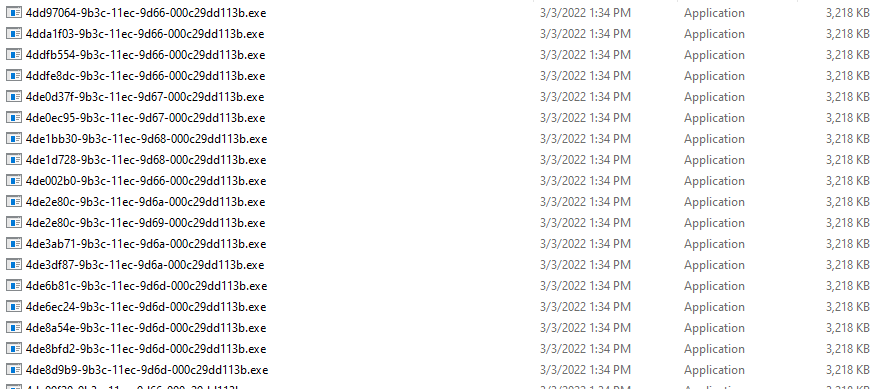
For example, 141,390 never-before-seen malware variants were recorded in Q4 2021 — more than any quarter on record. A total of 442,151 total never-before-seen malware variants was identified in 2021, a 65% increase over 2020’s count and an average of 1,211 per day.
The full ICSA Labs report can be downloaded here. To learn more about SonicWall Capture ATP with RTDMI, visit our website.