Cybersecurity News & Trends
SonicWall hits industry news with the unveiling of the Boundless 2022 global virtual partner experience, hosted by a legendary celebrity duo – learn more. In general news, Microsoft discloses hackers are using device registration to attack enterprises, and they’re also going after your Instagram accounts. In addition, the talent gap in cybersecurity is widening, SBA announced $3 million in grants for small business cybersecurity development, and cybersecurity is broken (but Dark Reading has ideas how to fix it).
Industry News
Register Now for Boundless 2022 – The Global Virtual Partner Experience
Reinforcing ongoing commitment to its partners and customers, SonicWall unveiled Boundless 2022, a virtual international marquee partner event, Feb. 23 & 24. Boundless 2022 will allow attending partners to hear first-hand about SonicWall’s technology vision product investments and gain a deeper understanding of the company’s customer commitment from SonicWall executives. It will also include an appearance from a legendary celebrity duo.
Hackers Using Device Registration Trick to Attack Enterprises with Lateral Phishing
The Hacker News: Microsoft has disclosed details of a large-scale, multi-phase phishing campaign that uses stolen credentials to register devices on a victim’s network to propagate spam emails further and widen the infection pool. The tech giant said the attacks manifested through accounts not secured using multi-factor authentication (MFA). Without MFA, attackers could take advantage of the target’s bring-your-own-device (BYOD) policy to introduce their own rogue devices using the pilfered credentials.
Hackers Hijacking Instagram Accounts Of Companies And Influencers, Demanding Ransom
ZDNet: Hackers are hijacking the Instagram accounts of companies and influencers with huge followings in a new phishing campaign identified by Secureworks. In October, the cybersecurity company said it discovered the effort, finding hackers taking over prominent accounts and demanding a ransom. The people behind the attack start by sending a message pretending to be Instagram, notifying Instagram users of a purported instance of copyright infringement. A link in the message takes victims to a website controlled by hackers. From there, the user is asked to enter their Instagram login information, giving the attackers full access to their accounts.
Cybersecurity Is Broken
Dark Reading: One significant development in the threat landscape is the corporatization of hacking. As with any burgeoning industry, hacking groups have implemented more organization to their structure to scale up. Plus, malware has gotten “smarter,” variants proliferate, and attackers take advantage of the distributed workforce. But the biggest impediments to better cybersecurity, say the authors, is that we stop conceptualizing cybersecurity as a wall and cease our reactive approach for tamping down attacks. Instead, companies need a security stack; efficiently layered to disrupt as many attack methods as possible.
The Widening Cybersecurity Talent Gap
Forbes: Over the past few years, one issue has remained prevalent and will continue to be as we head into 2022: a cybersecurity workforce shortage and talent gap. This is becoming a more recognizable problem as companies come to grips with the reality of cyberattacks, crime and the havoc they’re bringing on their victims. But, unfortunately, these aren’t just big names covered by the media; they’re businesses next door that might’ve already become a statistic of cybercrime.
SBA Announces $3 Million in Grants for Small Business Development
Small Business Trends: The Small Business Administration (SBA) has announced $3 million in new funding for state governments to assist emerging small businesses in developing their cyber security infrastructure. The new funding will help create a safer cyber environment for small businesses by giving them the proper training and tools to help make them less prone to potentially crippling cyberattacks. The funding is part of the Cybersecurity for Small Business Pilot Program, offered through the Office of Entrepreneurial Development.
APTs Quiet Ahead of Beijing Games, But Financially Motivated Hackers Are Lurking
Cyberscoop: State-sponsored hacking groups have been uncharacteristically quiet, leading up to the Olympics next month in Beijing. Researchers say there’s one big reason why: No one wants to get on the wrong side of China. Advanced persistent threat (APT) groups from Iran and Russia, while unlikely to attack China or the games, probably will use the event as a chance to spy on countries considered adversarial, researchers say. Potential avenues for surveillance include unique mobile SIM cards offered to foreign athletes to avoid the Chinese firewall and the MY2022 Olympic Games app all attendees must install.
Hackers Steal $80 Million In Cryptocurrency From The Qubit Defi Platform
The Verge: Qubit Finance, a decentralized finance (Defi) platform, has become the latest victim of a high-value theft, with hackers stealing around $80 million in cryptocurrency on Thursday. The value of cryptocurrency stolen makes this the largest hack of 2022 so far. Qubit Finance acknowledged the hack in an incident report published through Medium. According to the report, the hack occurred at around 5 PM ET on the evening of January 27th. Qubit provides a service known as a “bridge” between different blockchains, effectively meaning that deposits made in one cryptocurrency can be withdrawn in another. For example, Qubit Finance operates a bridge between Ethereum and the Binance Smart Chain (BSC) network.
Despite Attacks, Companies Leave Vast Amounts of Sensitive Data Unprotected
ProPublica: Companies leave data exposed online with little or no security, says Pompompurin, a pseudonymous hacker who posted millions of stolen records. The hacker then cited the attacks on RaidForums, a discussion board popular with cybercriminals seeking personal data. Pompompurin told ProPublica that he often doesn’t need to do much hacking to get his hands on sensitive personal data. Many times, it’s left in cloud storage folders available to anyone with internet access. Pompompurin said he scans the web for such unguarded material and then leaks it on RaidForums “because I can and it’s fun.”
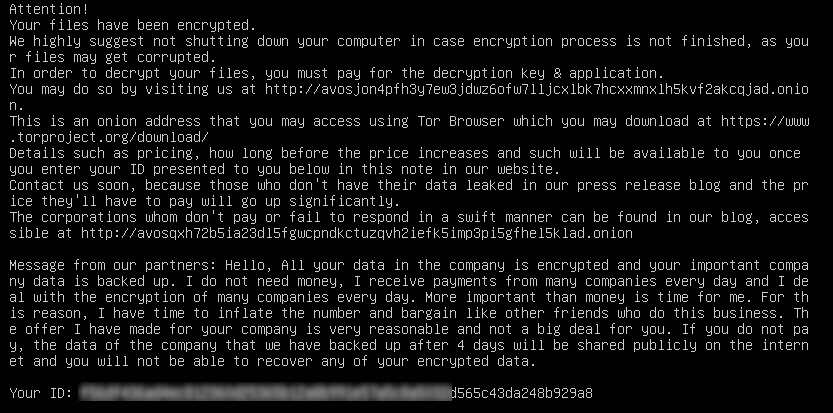
Ransomware Hackers Have a New Tactic: They Call You Directly
NBC News: Wayne didn’t know his son’s school district had been hacked — its files stolen and computers locked up and held for ransom — until last fall when the hackers started emailing him directly with garbled threats. “We hold control on the network several months, so we had a ton of time to carefully study, exfiltrate the data and prepare attack,” said one of the three emails he received. If his son’s district, the Allen Independent School District in the Dallas suburbs, didn’t pay up, all its files, including information on him and his son, “would be released in the dark market.” It was a credible threat. Ransomware hackers frequently leak files of organizations that don’t meet their demands and have littered the dark web with school children’s personal information.
In Case You Missed It
- Unpacking the U.S. Cybersecurity Executive Order – Kayvon Sadeghi
- Everything Old Is New Again: Remote Access Comes Full Circle – James Whewell
- How SonicWall ZTNA protects against Log4j (Log4Shell) – Rishabh Parmar
- 10 Tips for a Safe and Happy Holiday – Amber Wolff
- The Rise and Growth of Malware-as-a-Service – Ray Wyman
- A Record-Breaking Year for SonicWall’s Boundless Future – Ray Wyman
- Cybersecurity is Infrastructure – Ray Wyman
- Frost & Sullivan Commend SonicWall for Security Excellence – Kayvon Sadeghi
- SonicWall Answers the Call with New NGFWs – Ajay Uggirala
- Illuminating Cybersecurity with Unified Insights – Suroop Chandran
- How Unified Cloud Simplifies Network Switch Management – Tiju Cherian
- Cyber Threat Alert: Ransomware Breaks Another Record – Ray Wyman
- Why Cybersecurity Must be First – Ray Wyman
- How to Protect Multi-Cloud Environments with a NSv Virtual Firewall – Tiju Cherian
- What’s driving job growth in cybersecurity? – Ray Wyman