Badlock: Windows SAM and LSAD Downgrade Vulnerability

An elevation of privilege vulnerability exists in the Security Account Manager (SAM) and Local Security Authority (Domain Policy) (LSAD) remote protocols. Microsoft and SAMBA are vulnerable to these attacks. The vulnerability is triggered when these protocols accept authentication levels that do not protect them adequately. It is caused by the way the SAM and LSAD remote protocols establish the Remote Procedure Call (RPC) channel. An attacker who successfully exploited this vulnerability could gain access to the SAM database. To exploit the vulnerability, an attacker could launch a man-in-the-middle (MiTM) attack, force a downgrade of the authentication level of the SAM and LSAD channels, and then impersonate an authenticated user. The attacker can access domain passwords as well. The security update addresses the vulnerability by modifying how the SAM and LSAD remote protocols handle authentication levels.
There are two different CVE identifiers associated with this vulnerability:
- Microsoft: CVE-2016-0128
- SAMBA: CVE-2016-2118
In addition to this, the vulnerability has been known by 'badlock'.
Microsoft has two protocols that are vulnerable to this attack:
- Security Account Manager Remote Protocol(SAMR): This protocol provides management functionality for user account store and for user/group directries.
- Local Security Authority (LSAD): This protocol provides management functionality for user account store and for user/group directries.
These protocols manintain security account manager database. They are supported by both Windows and Samba and they support all domain profiles.
In addition to these, SAMBA's following protocols are susceptible to this vulnerability:
- Directory Replication Service Remote Protocol (DRSR): RPC protocol for replication and management of data in Active Directory
- BackupKey Remote Protocol (BKRP): Encrypts and decrypts sensitive data (such as cryptographic keys)
Attack mechanism:
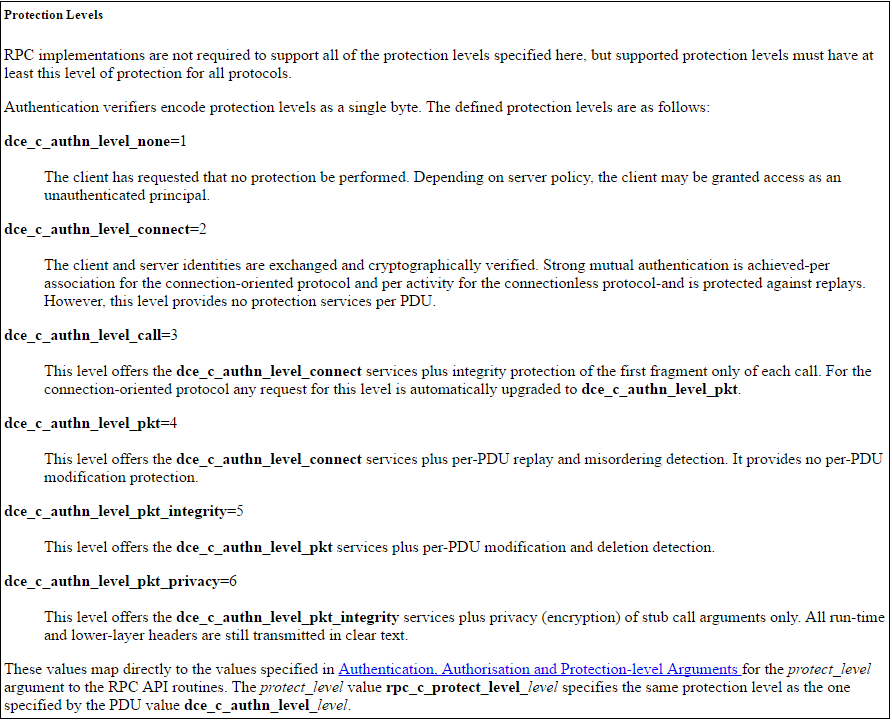
There are 6 authentication level (auth levels), as described in dcerpc protocol. '1' is the lowest and '6' being the highest:
Example of an attack scenario:
- 1: Client sends a bind request to the server with highest security level '6'.
- 2: MITM intercepts this request and changes the value from '6' to '2'
- 3: Server responds with auth level '2' instead.
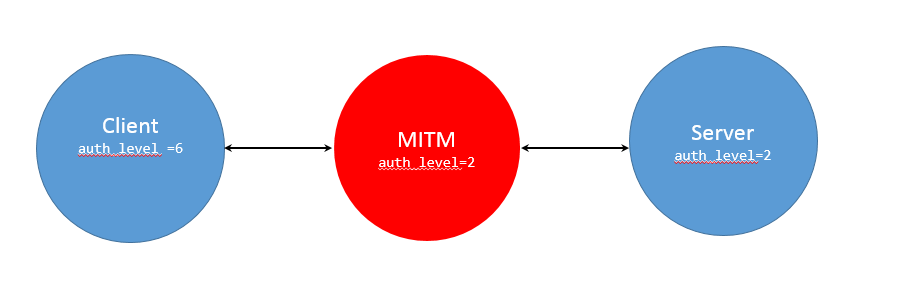
The attacker lowers the auth level to '2'. Level '2', as shown earlier, provides minimum authetication. Note that it does not protect the messages tranferred between the client and the server. This is an ideal scenario for an attacker. With this, the attacker can achieve read/write access to the SAMR services and potentially obtain passwords and any other sensitive information
Dell Sonicwall has written the following signature that protects our cutomers from this issue. It will be available in today's (04/12/2016) release.
- 11560: BadLock Vulnerability
- 11555: DCERPC AuthLevel Downgrade
Share This Article

An Article By
An Article By
Security News
Security News